
Beyond `apt install`: A Deep Dive into Advanced APT Package Management
The Heartbeat of Debian and Ubuntu: Mastering the APT Ecosystem
For anyone navigating the vast landscape of Debian, Ubuntu, or their many derivatives like Linux Mint and Pop!_OS, the Advanced Package Tool (APT) is an indispensable companion. It’s the silent workhorse that installs software, resolves dependencies, and keeps systems up-to-date. Most users are familiar with the holy trinity of apt update, apt install, and apt upgrade. However, this only scratches the surface of what APT can do. True system mastery, whether on a personal Linux desktop or a fleet of production servers, comes from understanding its deeper mechanics.
This article moves beyond the basics to explore the powerful, lesser-known features of APT. We will delve into the nuances of repository management, the strategic use of package pinning, advanced security automation, and powerful auditing techniques. Mastering these skills is critical for any modern Linux administrator or power user. This is the latest apt news you need to transform your package management from a routine task into a strategic advantage, ensuring your systems are not just functional, but also secure, stable, and efficiently managed. This knowledge is crucial for anyone following Debian news or Ubuntu news and wanting to get the most out of their operating system.
Section 1: Unifying the Toolbox with the Modern `apt` Command
The history of APT involves a collection of specialized tools: apt-get for package installation and removal, apt-cache for querying the package cache, and others. While these commands are still available and powerful, the modern apt command was introduced to provide a more user-friendly, consolidated interface with sensible defaults and improved feedback, like progress bars during installations.
From a Fragmented Past to a Unified Future
The primary goal of the apt command is to combine the most frequently used functions of apt-get and apt-cache into a single, intuitive tool. For day-to-day administration, it’s the recommended choice. It simplifies workflows and provides clearer, more concise output.
apt install <package>vs.apt-get install <package>: Functionally similar, butaptprovides a progress bar and more user-friendly output.apt search <term>vs.apt-cache search <term>: Both search for packages, butaptoffers a more readable, formatted output.apt show <package>vs.apt-cache show <package>: Again,aptpresents the information in a cleaner format.
A crucial distinction lies in upgrading. apt upgrade is the standard command for applying updates. However, apt full-upgrade (equivalent to the old apt-get dist-upgrade) is more powerful. It will intelligently handle changing dependencies, installing new packages or removing conflicting ones if necessary to complete a system-wide upgrade, which is often required for major release updates or complex Linux kernel news updates.
Practical Example: A Modern System Maintenance Script
Here is a simple Bash script that demonstrates a complete system maintenance routine using the modern apt command. This is a common task in Linux administration news, especially for managing servers running on platforms like DigitalOcean or Linode.
#!/bin/bash
# A simple script to update and clean a Debian/Ubuntu-based system
# Ensure the script is run as root
if [[ $EUID -ne 0 ]]; then
echo "This script must be run as root"
exit 1
fi
echo "--- Starting System Update ---"
# Step 1: Resynchronize the package index files
apt update
echo -e "\n--- Performing System Upgrade ---"
# Step 2: Upgrade all installed packages to their newest versions.
# The '-y' flag automatically answers 'yes' to prompts.
apt full-upgrade -y
echo -e "\n--- Cleaning Up Unused Dependencies ---"
# Step 3: Remove packages that were automatically installed to satisfy
# dependencies for other packages and are now no longer needed.
apt autoremove -y
echo -e "\n--- Cleaning Up APT Cache ---"
# Step 4: Clear out the local repository of retrieved package files.
# This frees up disk space.
apt clean
echo -e "\n--- System Maintenance Complete ---"Section 2: Advanced Repository Management and APT Pinning
The true power of APT lies in its ability to manage software from multiple sources, or “repositories.” Understanding how to control these sources is key to building a stable and customized system, a topic frequently discussed in Linux server news and DevOps circles.
Decoding `sources.list` and the Perils of PPAs

APT knows where to find packages by reading the configuration file /etc/apt/sources.list and any .list files within the /etc/apt/sources.list.d/ directory. These files contain URLs pointing to repositories, which are organized collections of software packages.
For Ubuntu users, repositories are typically categorized:
- Main: Officially supported, open-source software.
- Restricted: Officially supported, but proprietary software (e.g., hardware drivers).
- Universe: Community-maintained, open-source software.
- Multiverse: Unsupported, proprietary, and patent-encumbered software.
Personal Package Archives (PPAs) are a popular way for developers to distribute newer versions of software directly to users. While convenient, adding a PPA requires caution. You are trusting the PPA maintainer with root access to your system. Always verify the source of a PPA before adding it. This is a critical aspect of Linux security news that cannot be overlooked.
The Art of APT Pinning
What if you need a newer version of a single application (like Nginx or PostgreSQL) from a backports or third-party repository, but want to keep the rest of your system on the stable release? This is where APT pinning comes in. Pinning allows you to assign a priority to packages from different repositories, telling APT which version to prefer.
Priorities are set in files within /etc/apt/preferences.d/. A priority value greater than 1000 will force an install, even if it’s a downgrade. A priority between 500 and 1000 allows installation but doesn’t force it. A priority between 100 and 500 means the version will only be installed if there’s no other candidate from a higher-priority source.
Practical Example: Pinning a Newer Nginx Version
Imagine you are running Debian 11 “Bullseye” (stable) but need a feature from a newer Nginx version available in the official Nginx repository. You add the Nginx repository, but you want to ensure that only Nginx packages are installed from it, preventing other packages from being accidentally upgraded.
First, you’d create a preferences file, for example, /etc/apt/preferences.d/nginx-pin:
# This file configures APT pinning for the official Nginx repository.
# Give the official Nginx repository a higher priority, but only for nginx packages.
Package: nginx*
Pin: origin "nginx.org"
Pin-Priority: 900
# To prevent other packages from this repo from being installed,
# we can give the repository a low default priority.
Package: *
Pin: origin "nginx.org"
Pin-Priority: 50This configuration tells APT to assign a high priority (900) to any package whose name starts with “nginx” coming from the “nginx.org” origin, while all other packages from that same origin get a very low priority (50). This is a cornerstone technique in Linux DevOps news for maintaining stable production environments.
Section 3: Automation, Auditing, and Security Hardening
For system administrators, managing packages across multiple machines requires automation and robust auditing capabilities. APT provides tools that, when configured correctly, can significantly enhance system security and maintainability.
Automating Security with Unattended Upgrades
Manually applying security patches is tedious and prone to human error. The unattended-upgrades package is a crucial tool for automating this process. Once installed and configured, it can automatically download and install security updates, ensuring your systems are protected against known vulnerabilities without manual intervention. This is a non-negotiable best practice for any internet-facing server, a frequent topic in Linux firewall news and security discussions.
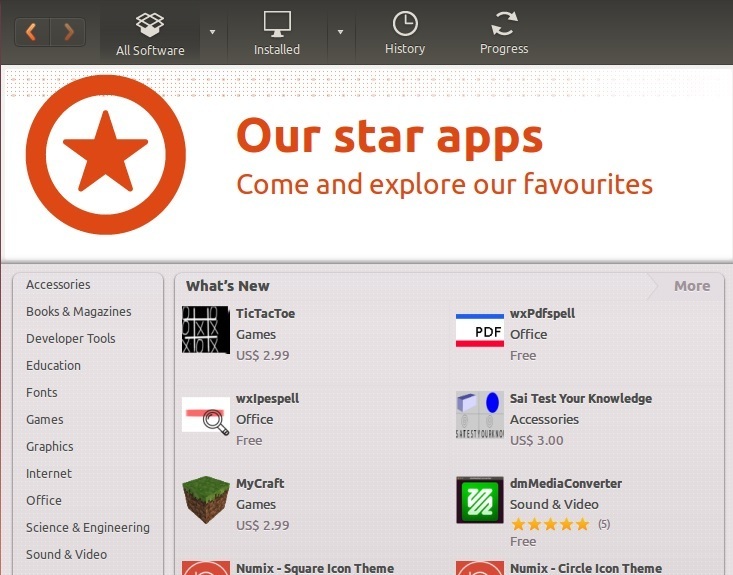
![Ubuntu apt - How to Use 'apt-get' Command in Ubuntu [20 Examples]](https://linux-digest.com/wp-content/uploads/2025/12/inline_9caad109.png)
Practical Example: Configuring Unattended Upgrades
The main configuration file is /etc/apt/apt.conf.d/50unattended-upgrades. You can enable it to install updates from specific origins, such as the security repositories for your distribution.
// Automatically install packages from these origins
Unattended-Upgrade::Allowed-Origins {
// Standard security updates
"${distro_id}:${distro_codename}-security";
// Optional: Other repositories like updates or backports
// "${distro_id}:${distro_codename}-updates";
// "${distro_id}:${distro_codename}-backports";
};
// Optional: Blacklist packages you do not want to automatically update
Unattended-Upgrade::Package-Blacklist {
// "nginx";
// "postgresql";
};
// Automatically remove unused dependencies after an upgrade
Unattended-Upgrade::Remove-Unused-Kernel-Packages "true";
Unattended-Upgrade::Remove-Unused-Dependencies "true";
// Optional: Enable automatic reboots if required
// Unattended-Upgrade::Automatic-Reboot "true";
// Unattended-Upgrade::Automatic-Reboot-Time "02:00";This configuration ensures that only security updates are applied automatically, and it also helps with system cleanup by removing old dependencies and kernel packages, a key part of modern systemd news and maintenance practices.
Auditing Installed Packages and Their Files
When troubleshooting or performing a security audit, you often need to know exactly what is installed on your system. APT and its underlying tool, dpkg, provide powerful introspection capabilities.
apt list --installed: Lists all installed packages.apt-cache policy <package>: Shows which repository a package was installed from and what other versions are available.dpkg -L <package>: Lists every single file installed by a package and its location on the filesystem.dpkg -S /path/to/file: Determines which installed package owns a specific file. This is invaluable for Linux forensics news and incident response.
Practical Example: Finding Manually Installed Packages
This one-liner script is incredibly useful for creating a list of packages you have explicitly installed, filtering out the hundreds of dependencies that were pulled in automatically. This is perfect for recreating a system or for a quick audit.
#!/bin/bash
# List all packages that were marked as manually installed.
# This is useful for system documentation or migration.
echo "--- Manually Installed Packages ---"
# comm compares two sorted files.
# apt-mark showmanual lists all manually installed packages.
# The second command generates a list of all installed packages.
# The '-23' flags tells comm to suppress lines unique to file 2 and lines that are common,
# effectively showing only lines unique to file 1 (the manually installed list).
comm -23 <(apt-mark showmanual | sort -u) <(gzip -dc /var/log/installer/initial-status.gz | sed -n 's/^Package: //p' | sort -u)Section 4: Best Practices and Avoiding Common Pitfalls
Using APT effectively also means knowing what *not* to do. Adhering to best practices will prevent a “broken” system and ensure long-term stability, whether you’re using Arch Linux with `pacman` or Fedora with `dnf`, the principles remain similar.
Best Practices for a Healthy System
- Be Wary of Third-Party Repositories: Only add repositories from sources you trust completely. A malicious repository can compromise your entire system.
- Use `apt-mark` to Hold Packages: If you need to prevent a specific package from being upgraded (e.g., a critical kernel module or a database server), use the
apt-markcommand. This is a much safer alternative to manual intervention. - Regularly Clean Up: Use
apt autoremove --purgeperiodically. The--purgeflag removes configuration files in addition to the package itself, helping to keep your system tidy. - Prefer Backports Over “FrankenDebian”: Avoid mixing repositories from different releases (e.g., adding Debian Testing repos to a Stable system). This can lead to an unresolvable dependency hell. If you need newer software, look for official backports repositories first.
Practical Example: Holding a Kernel Version
If a new kernel update is causing issues with your hardware, you can “hold” the current working version to prevent it from being upgraded until you are ready.
# To prevent the generic kernel package and its headers from being upgraded
sudo apt-mark hold linux-image-generic
sudo apt-mark hold linux-headers-generic
# To check the status of held packages
apt-mark showhold
# To release the hold when you are ready to upgrade
sudo apt-mark unhold linux-image-generic
sudo apt-mark unhold linux-headers-genericCommon Pitfalls
- Ignoring GPG Errors: When
apt updateshows GPG errors, it means it cannot verify the authenticity of a repository. Do not ignore this. It could indicate a misconfiguration or a man-in-the-middle attack. - Force-Installing Packages: Using flags like
--force-yeswithdpkgcan break your system’s dependency tree, leading to major problems down the line. The “broken packages” error is often a symptom of this. Always try to resolve dependency issues withapt --fix-broken installfirst.
Conclusion: Elevating Your Linux Expertise
The Advanced Package Tool is far more than a simple software installer; it is a sophisticated system for managing the entire lifecycle of software on your Debian or Ubuntu-based system. By moving beyond the basic commands, you unlock a new level of control and insight. We’ve explored the modern apt interface, the strategic power of repository management and pinning, the critical importance of automated security updates, and the practical commands for auditing your system.
By integrating these advanced techniques into your workflow, you can build more robust, secure, and maintainable Linux environments. Whether you are managing a single laptop running Kubuntu news or a cluster of servers powering a cloud application, a deep understanding of APT is a hallmark of a skilled Linux professional. The next step is to experiment. Use a virtual machine with KVM news or a Docker Linux news container to safely test these commands and configurations. Your journey to becoming an APT power user starts now.



