The Evolving Landscape of Linux DNS: Securing Network Communications with DNS-over-HTTPS
The Double-Edged Sword of DNS Encryption on Linux
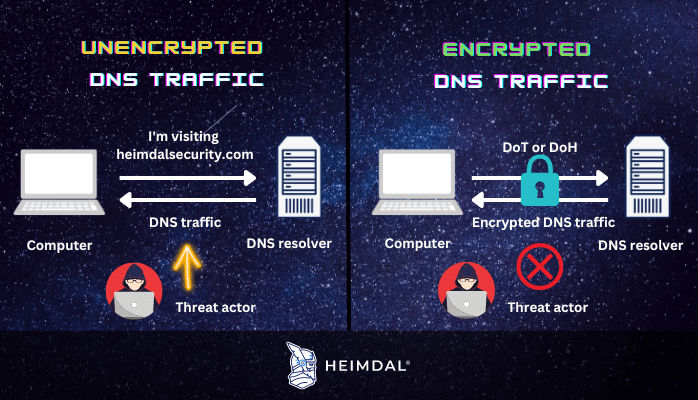
The Domain Name System (DNS) is the foundational directory of the internet, a critical yet historically insecure protocol that translates human-readable domain names into machine-readable IP addresses. For decades, these queries have been sent in plaintext over UDP port 53, making them susceptible to eavesdropping, manipulation, and censorship. This fundamental weakness has been a persistent concern in the cybersecurity community, leading to the development of encrypted DNS protocols. Among these, DNS-over-HTTPS (DoH) has emerged as a powerful standard for bolstering privacy and security.
DoH wraps DNS queries in standard HTTPS traffic, effectively hiding them from prying eyes on the network. This is a significant step forward for user privacy, preventing ISPs and malicious actors from snooping on browsing history or performing DNS hijacking attacks. However, this same encryption and obfuscation make DoH an attractive tool for threat actors. By tunneling their command-and-control (C2) communications through DoH, malware can bypass traditional network security measures that rely on monitoring plaintext DNS traffic. This duality presents a new challenge for Linux administrators and security professionals, making it crucial to understand, implement, and control DoH within their environments. This article explores the technical details of DoH on Linux, from basic implementation to advanced security considerations.
Core Concepts: From Plaintext Queries to Encrypted Tunnels
To appreciate the significance of DoH, one must first understand the vulnerabilities it aims to solve. Traditional DNS is a trust-based system with little to no built-in security, a relic of an earlier, more open internet. This design has several critical flaws that are actively exploited.
The Vulnerabilities of Traditional DNS
When you use a command like dig or nslookup, or when your browser looks up a website, a plaintext query is sent to a recursive DNS server. Anyone positioned between your device and the resolver—a compromised router, a malicious actor on a public Wi-Fi network, or even an Internet Service Provider—can intercept and read this query. This opens the door to several attacks:
- Eavesdropping: Attackers can passively collect data on which websites you visit, building a profile of your online activity.
- DNS Spoofing/Hijacking: An attacker can intercept a query and return a fraudulent IP address, redirecting a user to a phishing site or a server hosting malware.
- Censorship and Redirection: ISPs or nation-states can block access to certain domains by refusing to resolve them or redirecting them to a block page.
How DNS-over-HTTPS Provides a Solution
DNS-over-HTTPS (RFC 8484) fundamentally changes the transport mechanism for DNS queries. Instead of sending a UDP packet to port 53, a DoH-enabled client sends an HTTP GET or POST request to a specific URL on a DoH resolver, such as https://cloudflare-dns.com/dns-query. Because the entire transaction is wrapped in an HTTPS tunnel, it inherits all the security benefits of TLS encryption:
- Confidentiality: The content of the DNS query (the domain name being requested) is encrypted and unreadable to network observers.
- Integrity: HTTPS ensures that the response from the DNS server has not been tampered with in transit.
- Obfuscation: DoH traffic uses TCP port 443, the same port used for all HTTPS web traffic. This makes it incredibly difficult for network filters to distinguish DNS queries from regular web browsing, thwarting simple port-based blocking.
You can demonstrate this mechanism yourself with a simple curl command, which effectively bypasses your system’s traditional DNS resolver and queries a DoH provider directly.
# Manually perform a DoH query for example.com using Google's DNS resolver
# The 'Accept' header specifies the wireformat for the DNS response
curl -s -H 'accept: application/dns-json' 'https://dns.google/resolve?name=example.com&type=A' | python3 -m json.toolThis command sends an HTTPS GET request and receives a JSON-formatted DNS response, all securely encrypted and indistinguishable from other web API calls. This is the core reason why the latest Linux security news often highlights both the privacy benefits and the potential for misuse of this powerful protocol.
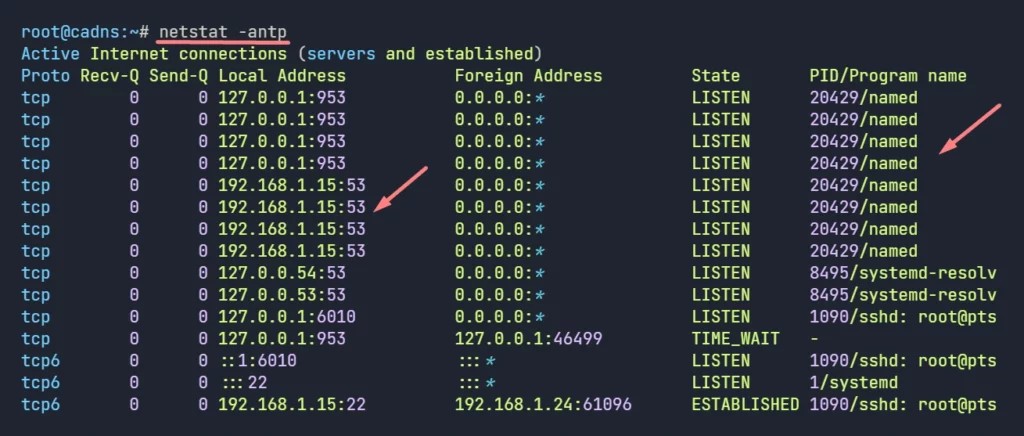
Implementing DoH on Modern Linux Systems with systemd-resolved
Many modern Linux distributions, including those covered in recent Ubuntu news, Fedora news, and Debian news, use systemd-resolved as their default DNS management service. The good news for administrators is that systemd-resolved has built-in support for DoH, making the transition relatively seamless. This represents a significant update in recent systemd news, simplifying what was once a complex configuration task.

Configuration Steps for systemd-resolved
Enabling DoH is a matter of editing the main configuration file and restarting the service. The configuration is managed in /etc/systemd/resolved.conf.
1. Open the configuration file with a text editor like nano or vim:
sudo nano /etc/systemd/resolved.conf2. Modify the [Resolve] section: Uncomment and set the DNS, FallbackDNS, and DNSOverHTTPS directives. The DNS entry will specify the IP addresses of your chosen DoH providers, which are used to bootstrap the DoH connection. The DNSOverHTTPS directive enables the feature.
[Resolve]
# Specify your chosen DoH providers' IP addresses and domains
# Example using Cloudflare (privacy-focused) and Quad9 (security-focused)
DNS=1.1.1.1#cloudflare-dns.com 1.0.0.1#cloudflare-dns.com 9.9.9.9#dns.quad9.net
# Provide fallback DNS servers in case DoH fails
FallbackDNS=8.8.8.8 8.8.4.4
# Enable DoH. "yes" will use it if the server supports it. "opportunistic" is also an option.
DNSOverHTTPS=yes
# Optional: You can also enable DNSSEC for an extra layer of validation
DNSSEC=yes3. Save the file and restart the service to apply the changes:
sudo systemctl restart systemd-resolvedVerification and Troubleshooting
After restarting the service, you must verify that DoH is active. The resolvectl command is the primary tool for this.
Run resolvectl status to see the current DNS server configuration. In the output for your active network interface, you should see your configured DoH server listed with “(DNSOverHTTPS)” next to its name, and the “Current DNS Server” should be one of the IPs you specified.
If you encounter issues, the first place to look for clues is the service’s journal, a key practice in Linux troubleshooting news. You can view the logs for systemd-resolved using journalctl.
journalctl -u systemd-resolved --since "5 minutes ago"This will show you logs related to establishing connections, certificate validation, and any errors encountered while communicating with the DoH servers.
Advanced Techniques and Security Monitoring
While systemd-resolved is excellent for desktop and many server use cases, advanced scenarios may require more granular control or network-wide policies. This is where dedicated proxies and vigilant network monitoring come into play, a critical topic in Linux server news and Linux administration news.
Using Dedicated DoH Proxies
Tools like cloudflared or dnscrypt-proxy can act as local DoH forwarders. You configure the proxy to connect to upstream DoH resolvers, and then point your system’s (or your entire network’s) DNS settings to the local proxy instance. This offers several advantages:
- Local Caching: The proxy can cache DNS responses locally, speeding up subsequent lookups for frequently accessed domains.
- Advanced Filtering: Some proxies offer advanced features like ad-blocking, malware domain filtering, and custom blocklists.
- Network-Wide Service: A single proxy instance running on a server can provide encrypted DNS for all devices on a local network, including those that don’t natively support DoH.
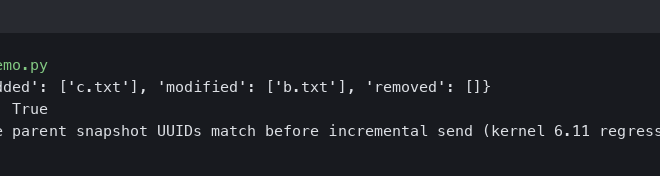
Programmatic DoH and Its Implications
The simplicity of DoH—being just an HTTPS request—makes it trivial to implement in any programming language. This is a boon for developers but also for malware authors. A simple Python script can replicate DoH functionality, completely bypassing system-level DNS settings. This is a core reason why endpoint security is so important.
import requests
import json
def resolve_doh(domain, resolver_url="https://cloudflare-dns.com/dns-query"):
"""
Performs a DNS A record lookup using DNS-over-HTTPS.
"""
headers = {
"Accept": "application/dns-json",
}
params = {
"name": domain,
"type": "A",
}
try:
response = requests.get(resolver_url, headers=headers, params=params)
response.raise_for_status() # Raise an exception for bad status codes
results = response.json()
if "Answer" in results:
for answer in results["Answer"]:
if answer["type"] == 1: # Type 1 is an A record
print(f"Domain: {domain}, IP Address: {answer['data']}")
else:
print(f"No A record found for {domain}")
except requests.exceptions.RequestException as e:
print(f"An error occurred: {e}")
if __name__ == "__main__":
resolve_doh("github.com")
resolve_doh("bleepingcomputer.com")This script, relevant to Python Linux news, demonstrates how easily an application can hardcode its own DoH resolver, making its network activity invisible to system-level or network-level DNS monitoring that only watches port 53.
Best Practices for a Secure DNS Infrastructure
Given that DoH can be used for both good and ill, a proactive security posture is essential. Simply enabling DoH is not enough; administrators must manage its use across their infrastructure, a key theme in modern Linux security news.
Enforce a Centralized DNS Policy
For any organization, from a home network to a large enterprise, the first step is to establish a clear DNS policy. If you decide to use DoH, standardize on a trusted, managed resolver. This could be an internal DoH proxy or a public provider whose policies align with your security goals (e.g., one that filters malicious domains).
To enforce this policy, you must block unauthorized DoH traffic. Since DoH runs over port 443, you cannot simply block the port. Instead, you must block the IP addresses of known public DoH resolvers that you do not want clients to use. This can be done with a firewall like nftables, a topic of frequent discussion in Linux firewall news.
#!/usr/sbin/nft -f
# This is a basic nftables ruleset snippet.
# Do not apply without understanding your existing firewall configuration.
table inet filter {
chain output {
# Block outgoing connections to Google's DNS IPs on the HTTPS port
ip daddr { 8.8.8.8, 8.8.4.4 } tcp dport 443 reject with tcp reset
ip6 daddr { 2001:4860:4860::8888, 2001:4860:4860::8844 } tcp dport 443 reject with tcp reset
}
}This nftables rule prevents devices on the network from reaching Google’s DoH servers, forcing them to use the DNS servers assigned by the network (e.g., via DHCP).
Layer Your Security
DoH is one layer in a deep defense strategy. It protects the transport of DNS queries but does not inherently block malicious domains. It should be combined with:
- Endpoint Security: An EDR or anti-malware solution can detect malicious processes making suspicious network calls, regardless of the protocol used.
- Network Monitoring: While DoH content is encrypted, metadata can still be revealing. Analyzing traffic patterns, such as a device making many HTTPS connections to a single, non-CDN IP address, can indicate C2 activity.
- DNSSEC: Use DoH in conjunction with DNSSEC to ensure the authenticity and integrity of DNS responses from the authoritative server.
In containerized environments, a topic of constant evolution in Docker Linux news and Kubernetes Linux news, it’s vital to ensure that containers inherit the host’s secure DNS configuration or are explicitly configured by the orchestrator to use the approved network resolver.
Conclusion: Embracing an Encrypted Future
DNS-over-HTTPS represents a necessary and pivotal evolution in internet infrastructure, bringing long-overdue privacy and security to one of its oldest protocols. For users of all major Linux distributions, from Arch Linux and Gentoo to Red Hat and openSUSE, implementing DoH is more accessible than ever, thanks to tools like systemd-resolved.
However, the adoption of DoH is not without its challenges. Its ability to mask traffic makes it a potent tool for adversaries seeking to hide their tracks. This reality forces a paradigm shift for network defense. Linux administrators and security professionals must move beyond legacy port-53 monitoring and adopt a more sophisticated, layered approach. The key takeaways are to implement DoH deliberately through a centralized policy, use firewalls to block unauthorized resolvers, and complement DNS security with robust endpoint and network traffic analysis. By understanding both the promise and the peril of DoH, we can harness its benefits while mitigating the risks, ensuring a more secure and private Linux ecosystem for everyone.