The Open Source Shift: Analyzing Linux VPN Client Architecture and Security Transparency
Introduction: The New Standard for Linux Privacy Tools
The landscape of Linux security news and privacy tools is undergoing a significant transformation. For years, the standard for proprietary VPN services on Linux involved closed-source binaries, opaque daemons, and a “trust us” approach to security. However, the community driving Linux desktop news—from Ubuntu news and Fedora news to Arch Linux news enthusiasts—has long demanded greater transparency. The recent trend of major security providers releasing the source code for their Linux clients and networking libraries marks a pivotal moment in this evolution. This shift isn’t just about compliance; it is about architectural honesty, allowing the community to audit, improve, and understand the code running with root privileges on their machines.
When a VPN provider opens its repositories, it allows developers and system administrators to inspect how the application handles Linux networking news concepts like routing tables, iptables news, and WireGuard news implementation. It bridges the gap between proprietary service and the open-source ethos that defines distributions like Debian news, openSUSE news, and Linux Mint news. This article delves deep into the technical architecture of modern open-source VPN clients on Linux, exploring how they interact with the kernel, manage encryption, and how developers can programmatically interact with these networking stacks.
Core Concepts: The Anatomy of a Linux VPN Client
To understand the significance of open-sourced VPN libraries, one must understand the underlying architecture. A robust Linux VPN client is rarely just a GUI or a CLI wrapper; it is a complex orchestration of kernel modules, userspace networking, and encryption protocols. Whether running on Pop!_OS news, Manjaro news, or a headless Rocky Linux news server, the fundamental mechanics rely on the Linux kernel’s TUN/TAP interfaces.
TUN/TAP Interfaces and Go Implementation
Most modern VPN clients, particularly those leveraging Go Linux news or Rust Linux news for performance and safety, operate by creating a TUN (Layer 3) or TAP (Layer 2) device. This virtual network interface captures packets which the userspace application then encrypts and encapsulates before sending them out the physical interface. With the source code available, developers can see exactly how these interfaces are initialized and managed.
Below is a practical example using Go (Golang), a language frequently used in modern cloud-native and networking tools (like Docker Linux news and Kubernetes Linux news components), demonstrating how a VPN client initializes a TUN device. This illustrates the low-level access required by these libraries.
package main
import (
"fmt"
"log"
"os"
"syscall"
"unsafe"
)
const (
IFF_TUN = 0x0001
IFF_NO_PI = 0x1000
TUNSETIFF = 0x400454ca
)
type ifreq struct {
name [16]byte
flags uint16
_ [22]byte
}
// CreateTunInterface demonstrates how VPN clients request virtual interfaces from the kernel
func CreateTunInterface(name string) (*os.File, error) {
// Open the clone device
fd, err := os.OpenFile("/dev/net/tun", os.O_RDWR, 0)
if err != nil {
return nil, fmt.Errorf("error opening /dev/net/tun: %v", err)
}
var req ifreq
req.flags = IFF_TUN | IFF_NO_PI
copy(req.name[:], name)
// Perform the ioctl call to create the interface
// This is the critical step often hidden in closed-source binaries
_, _, errno := syscall.Syscall(
syscall.SYS_IOCTL,
fd.Fd(),
uintptr(TUNSETIFF),
uintptr(unsafe.Pointer(&req)),
)
if errno != 0 {
fd.Close()
return nil, fmt.Errorf("ioctl failed: %v", errno)
}
fmt.Printf("Interface %s created successfully.\n", name)
return fd, nil
}
func main() {
// Requires root privileges (sudo)
if os.Geteuid() != 0 {
log.Fatal("This program must be run as root.")
}
tunDevice, err := CreateTunInterface("tun0")
if err != nil {
log.Fatal(err)
}
defer tunDevice.Close()
// In a real VPN client, the loop below would read packets,
// encrypt them, and send them to the server.
fmt.Println("Listening on tun0... (Press Ctrl+C to exit)")
select {}
}This code snippet reveals the interaction between userspace and Linux kernel news features. By open-sourcing libraries that handle these operations, vendors allow the community to verify that flags like `IFF_NO_PI` (No Packet Information) are used correctly to prevent protocol leaks, a common concern in Linux security news.
Implementation Details: Daemon Communication and IPC

Open source code on screen – What Is Open-Source Software? (With Examples) | Indeed.com
A secure VPN client on Linux usually splits into two parts: a privileged background daemon (running as root) and an unprivileged CLI or GUI client (running as the user). This separation of privilege is crucial for security. In the context of GNOME news, KDE Plasma news, or i3wm news environments, the client communicates with the daemon via Inter-Process Communication (IPC).
D-Bus and Socket Communication
When libraries are open-sourced, we can inspect the IPC mechanisms. Is the client sending cleartext passwords to the daemon? Is the socket permissioned correctly? Most enterprise-grade Linux software uses Unix Domain Sockets or D-Bus. For Python Linux news developers and Linux automation news specialists, understanding this API allows for custom integrations.
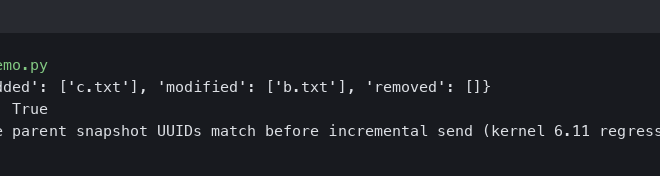
The following Python example demonstrates how an external tool might interact with a VPN daemon’s control socket. This is relevant for Linux DevOps news professionals who wish to automate VPN connections within Ansible news playbooks or Terraform Linux news scripts.
import socket
import json
import os
# Configuration for the hypothetical VPN daemon socket
SOCKET_PATH = "/var/run/vpn-client/daemon.sock"
def get_vpn_status():
"""
Connects to the VPN daemon via Unix Domain Socket
to retrieve status and connection metrics.
"""
if not os.path.exists(SOCKET_PATH):
return {"error": "VPN daemon is not running"}
try:
# Create a Unix domain socket
client = socket.socket(socket.AF_UNIX, socket.SOCK_STREAM)
client.connect(SOCKET_PATH)
# Send a status command
command = {"action": "get_status", "version": "1.0"}
client.sendall(json.dumps(command).encode('utf-8'))
# Receive the response
response_data = client.recv(4096)
response = json.loads(response_data.decode('utf-8'))
client.close()
return response
except socket.error as e:
return {"error": f"Socket communication failed: {e}"}
except json.JSONDecodeError:
return {"error": "Invalid response from daemon"}
# Example usage for system monitoring
if __name__ == "__main__":
status = get_vpn_status()
if "connected" in status and status["connected"]:
print(f"[SECURE] VPN Connected to {status.get('server_ip')}")
print(f"Protocol: {status.get('protocol')} | Uptime: {status.get('uptime')}")
else:
print("[ALERT] VPN Disconnected! Check your configuration.")This transparency is vital. In the past, Linux administration news often involved parsing log files from journalctl news or dmesg news to guess the VPN state. With open libraries, we can see the exact JSON or Protobuf structures used, enabling the creation of robust extensions for Polybar (common in Arch Linux news setups) or GNOME extensions.
Advanced Techniques: The “Kill Switch” and Routing Logic
One of the most critical features of any VPN client is the “Kill Switch”—the mechanism that prevents traffic from leaking over the default gateway if the VPN tunnel collapses. In proprietary clients, this logic is a black box. In open-source implementations, we can verify if the client uses nftables news, iptables news, or policy-based routing.
Netlink and Rust for Network State Monitoring
Modern Linux networking relies heavily on Netlink sockets to modify routing tables and monitor interface states. Rust Linux news is gaining traction for these tasks due to its memory safety, preventing buffer overflows that could be exploited in security tools. An open-source library allows us to see how the client reacts to network changes (e.g., switching from Linux WiFi news to Ethernet).
Here is a conceptual Rust snippet demonstrating how a VPN library might listen for network interface changes to trigger a kill switch. This level of low-level control is what separates a script from a professional application.

Open source code on screen – Open-source tech for nonprofits | India Development Review
use std::sync::{Arc, Mutex};
use std::thread;
use std::time::Duration;
// Mocking structures to represent Netlink interaction
// In a real scenario, crates like `netlink-packet-route` would be used.
#[derive(Debug, Clone)]
struct NetworkState {
vpn_interface_up: bool,
default_gateway_reachable: bool,
}
fn monitor_network_integrity(state: Arc<Mutex<NetworkState>>) {
println!("Starting Netlink monitor for Kill Switch logic...");
loop {
// Simulate checking interface flags via Netlink
// In reality, this would be an event loop listening for RTM_NEWLINK / RTM_DELLINK
let is_tun_up = check_interface_flags("tun0");
let mut current_state = state.lock().unwrap();
if current_state.vpn_interface_up && !is_tun_up {
// CRITICAL: VPN dropped unexpectedly
engage_kill_switch();
current_state.vpn_interface_up = false;
} else if is_tun_up {
current_state.vpn_interface_up = true;
}
thread::sleep(Duration::from_millis(500));
}
}
fn check_interface_flags(iface: &str) -> bool {
// This function would interface with the kernel via libc or netlink
// Returning true for simulation purposes
true
}
fn engage_kill_switch() {
println!("[EMERGENCY] VPN Interface down! Engaging firewall rules via nftables...");
// Execute nftables command to drop all non-tun traffic
// std::process::Command::new("nft").args(&["add", "rule", ...]).output();
}
fn main() {
let state = Arc::new(Mutex::new(NetworkState {
vpn_interface_up: true,
default_gateway_reachable: true,
}));
let monitor_handle = thread::spawn(move || {
monitor_network_integrity(state);
});
monitor_handle.join().unwrap();
}By analyzing the open source code, users of Kali Linux news or Parrot OS news can determine if the kill switch is reactive (detects drop -> adds rule) or proactive (rules exist permanently, allowing only VPN traffic). The latter is preferred for high-security environments, and open source confirms which method is utilized.
Best Practices and Optimization
With the availability of source code for VPN clients and libraries, Linux systemd news administrators and Linux security news experts should adopt specific best practices to maximize security and performance.
1. Verify Signatures and Builds
Just because code is open source doesn’t mean the binary you downloaded matches that code. Users should utilize Linux CI/CD news principles. If the vendor provides a reproducible build process, verify it. Use GPG to verify source tarballs.
#!/bin/bash
# Example script to verify a source code release
VENDOR_KEY_ID="0x12345678ABCDEF00"
SOURCE_FILE="vpn-client-source-v1.0.tar.gz"
SIG_FILE="vpn-client-source-v1.0.tar.gz.asc"
# Fetch the public key if not present
gpg --list-keys $VENDOR_KEY_ID > /dev/null 2>&1
if [ $? -ne 0 ]; then
echo "Importing vendor public key..."
gpg --keyserver keyserver.ubuntu.com --recv-keys $VENDOR_KEY_ID
fi
# Verify the signature
echo "Verifying signature for $SOURCE_FILE..."
gpg --verify $SIG_FILE $SOURCE_FILE
if [ $? -eq 0 ]; then
echo "SUCCESS: The source code is authentic and unmodified."
# Proceed to build
# cargo build --release or go build
else
echo "DANGER: Signature verification failed! Do not compile."
exit 1
fi2. Kernel Module vs. Userspace (Go/Rust)

Open source code on screen – Design and development of an open-source framework for citizen …
When compiling or configuring these open-source clients, pay attention to the implementation of the protocol. WireGuard news often highlights the performance benefits of kernel-space implementations. However, userspace implementations (often written in Go or Rust) are easier to update and less likely to crash the entire system. For Linux server news environments, a kernel module might be preferred for throughput, while Linux laptop news users might prefer userspace for stability.
3. Integration with Systemd
Open-source clients allow you to inspect the systemd unit files. Ensure that the service utilizes modern hardening features. Look for directives like `ProtectSystem=strict`, `ProtectHome=yes`, and `PrivateTmp=yes` in the `.service` file. If the vendor’s default unit file is too permissive, you can now write a drop-in replacement with confidence, knowing how the binary behaves.
Conclusion
The movement toward open-sourcing Linux VPN clients and networking libraries is a massive win for the ecosystem. It impacts everyone from Gentoo news compilation enthusiasts to Enterprise Linux administrators. It transforms a VPN client from a “black box” security appliance into a transparent, auditable tool that integrates seamlessly with the Linux open source news philosophy.
For developers, this opens the door to contributing fixes, optimizing Linux networking news stacks, and building custom wrappers. For system administrators, it provides the assurance that the code running as root is doing exactly what it claims to do—and nothing more. As we see more tools in the Linux VPN news sector adopt this approach, the standard for privacy and security on the platform will only rise. The next step for the community is to actively engage: audit the code, report issues, and leverage these libraries to build a more secure internet.