
Mastering Network Automation: A Deep Dive into Modern Linux DHCP Solutions
The Unsung Hero of Your Network: Why Linux DHCP Still Matters
In the complex world of network administration, some of the most critical services are the ones we take for granted. At the top of that list is the Dynamic Host Configuration Protocol (DHCP), the silent workhorse that automatically assigns IP addresses and network configurations to devices. Without it, every phone, laptop, and server would require manual setup, an impossible task at any scale. While the protocol itself is standardized, the implementation on the server side is where the real power lies. For decades, Linux has offered the most robust, flexible, and reliable DHCP solutions available, and this remains a cornerstone of Linux networking news. From the venerable ISC DHCP daemon to modern, API-driven platforms, understanding the landscape of Linux DHCP is essential for any system administrator, DevOps engineer, or network architect. This article delves into the state of DHCP on Linux, exploring the classic tools that still dominate, the lightweight alternatives for simpler setups, and the next-generation solutions shaping the future of network automation.
Whether you’re managing a small office network on Ubuntu, a massive enterprise data center on Red Hat Enterprise Linux, or a cluster of IoT devices running on a custom Yocto build, the principles remain the same. The latest Linux server news consistently highlights the importance of stable, secure, and manageable core services. As we’ll see, the evolution of DHCP servers on Linux reflects broader trends in the industry: a move towards automation, better observability, and API-first design, all while retaining the stability that has made tools like dhcpd legendary.
The Bedrock of Linux DHCP: Understanding ISC DHCP (`dhcpd`)
For over two decades, the Internet Systems Consortium’s (ISC) DHCP daemon, commonly known as dhcpd, has been the undisputed king of DHCP servers. It’s the default or a primary option in nearly every major distribution, from Debian news to CentOS news. Its power lies in its incredible flexibility, exhaustive feature set, and battle-tested stability. However, a significant piece of Linux DHCP news has been the announcement of its End-of-Life (EOL) status, with ISC shifting focus to its modern successor, Kea. Despite this, dhcpd remains deeply entrenched and will be supported by long-term-support distributions for years to come, making it a critical tool to master.
Why `dhcpd` is Still a Go-To Choice
The primary reason for dhcpd‘s longevity is its powerful and declarative configuration file, dhcpd.conf. It allows administrators to define complex network topologies, create different pools for different device classes, set up failover pairs for high availability, and handle vendor-specific options with ease. This level of control is paramount in enterprise environments. For many sysadmins, the “if it ain’t broke, don’t fix it” mantra applies perfectly. Its behavior is predictable, it’s well-documented, and an enormous body of knowledge exists online for troubleshooting any conceivable scenario. This makes it a safe and reliable choice for production systems running on everything from Rocky Linux news to SUSE Linux news.
Practical Configuration for a Standard LAN
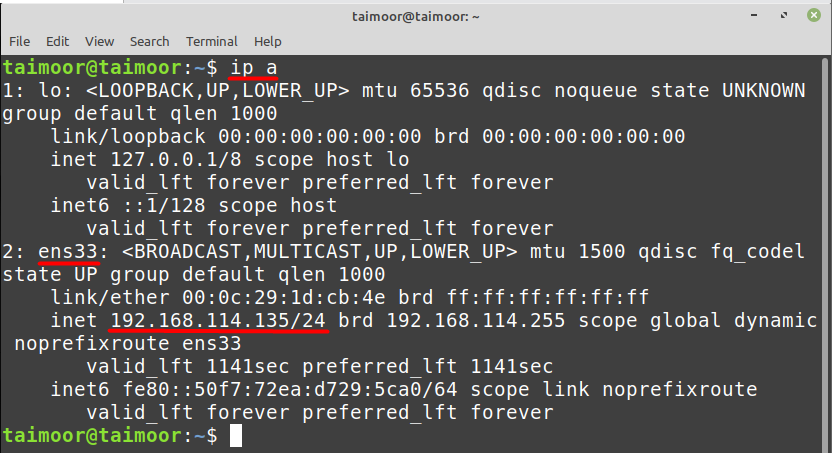
Getting started with dhcpd involves editing the /etc/dhcp/dhcpd.conf file. The syntax is straightforward but requires precision. A typical setup for a small office network defines the default lease times, DNS servers, and the subnet configuration, including the IP range to be allocated and the default gateway.
Here is a complete and practical example of a basic dhcpd.conf file:
# dhcpd.conf - Example for a simple office network
# Set global options that apply to all subnets
# Use Google's DNS servers and a local domain name
option domain-name "office.lan";
option domain-name-servers 8.8.8.8, 8.8.4.4;
# Set default lease times in seconds
default-lease-time 3600; # 1 hour
max-lease-time 7200; # 2 hours
# This DHCP server is the official one for this network
authoritative;
# Log using the standard syslog facility
log-facility local7;
# Define the network segment (subnet)
subnet 192.168.1.0 netmask 255.255.255.0 {
# The range of IP addresses to hand out to clients
range 192.168.1.100 192.168.1.200;
# The default gateway (router) for clients on this subnet
option routers 192.168.1.1;
# The broadcast address for this subnet
option broadcast-address 192.168.1.255;
}
# Example of a static IP assignment for a known server
host fileserver {
hardware ethernet 00:1A:2B:3C:4D:5E;
fixed-address 192.168.1.10;
}After configuring, you would typically enable and start the service using systemd commands like sudo systemctl enable --now dhcpd, a common practice discussed in systemd news. Checking the logs with journalctl -u dhcpd is crucial for troubleshooting.
The Lightweight Contender: `dnsmasq` for Integrated Services
While dhcpd is a heavyweight champion, not every situation requires its extensive feature set. For home networks, small offices, or specialized use cases like PXE booting, dnsmasq is an incredibly popular and efficient alternative. As its name suggests, dnsmasq is a lightweight, integrated DNS forwarder and DHCP server. This combination is its killer feature: it can serve DHCP leases and automatically provide DNS resolution for those leased hostnames without any complex integration with a separate BIND server. This simplicity is often highlighted in community discussions around Arch Linux news and Raspberry Pi Linux news, where ease of use and a small resource footprint are highly valued.
Configuring DHCP and DNS with `dnsmasq`
The configuration for dnsmasq, typically found at /etc/dnsmasq.conf, is much simpler than dhcpd. You define the network interface to listen on, the DHCP range, and any additional options. Its ability to read hostnames from /etc/hosts and serve them via DNS makes local network name resolution trivial.
# /etc/dnsmasq.conf - A simple configuration for a home network
# Don't read /etc/resolv.conf for upstream DNS servers
no-resolv
# Specify upstream DNS servers directly
server=8.8.8.8
server=1.1.1.1
# Listen for requests only on the local LAN interface
interface=eth0
# Define the range of IPs to lease, the netmask, and the lease time
# Format: <start-ip>,<end-ip>,<netmask>,<lease-time>
dhcp-range=192.168.1.50,192.168.1.150,255.255.255.0,12h
# Provide the default gateway to clients
# Option 3 is the router/gateway
dhcp-option=option:router,192.168.1.1
# Provide DNS servers to clients
# Option 6 is DNS server. Here we provide the dnsmasq server itself.
dhcp-option=option:dns-server,192.168.1.1
# Enable local DNS resolution for DHCP clients
domain-needed
bogus-priv
# Set a domain for the local network
domain=home.arpaStatic Leases and Host Naming
One of the most common tasks in Linux administration news is ensuring a specific device always receives the same IP address. With dnsmasq, this is accomplished with a simple dhcp-host line, which ties a MAC address to an IP address and a hostname. This hostname is then automatically resolvable on the network.
# Add these lines to /etc/dnsmasq.conf for static assignments
# Assign a static IP to a printer
dhcp-host=B8:27:EB:12:34:56,printer,192.168.1.20,infinite
# Assign a static IP to a NAS device
dhcp-host=00:11:22:AA:BB:CC,nas-storage,192.168.1.21,infiniteThis tight integration of DHCP and DNS makes dnsmasq an excellent choice for environments where simplicity and ease of management are the primary goals, a frequent topic in forums related to Linux Mint news and Pop!_OS news.
The Future is Now: Kea DHCP
The most significant development in the Linux DHCP news space is the rise of Kea, ISC’s modern replacement for dhcpd. Written from the ground up in C++, Kea is designed for the modern era of networking. It addresses many of the architectural limitations of its predecessor, offering superior performance, a clean JSON-based configuration, and, most importantly, a REST API for dynamic management and monitoring. This API-first approach is a game-changer, aligning perfectly with modern Linux DevOps news and the push for infrastructure-as-code. Major distributions are taking note, with Fedora news and Ubuntu news increasingly positioning Kea as the recommended DHCP solution for new deployments.
A Glimpse into Kea’s JSON Configuration
Moving away from the custom syntax of dhcpd.conf, Kea uses JSON, a format familiar to any developer or DevOps engineer. This makes configuration easier to parse, generate, and validate programmatically. While the structure is different, the core concepts remain the same: defining subnets, pools, and options.
{
"Dhcp4": {
"interfaces-config": {
"interfaces": [ "eth0" ]
},
"lease-database": {
"type": "memfile",
"lfc-interval": 3600
},
"valid-lifetime": 4000,
"renew-timer": 1000,
"rebind-timer": 2000,
"subnet4": [
{
"subnet": "192.168.1.0/24",
"pools": [
{ "pool": "192.168.1.100 - 192.168.1.200" }
],
"option-data": [
{
"name": "routers",
"data": "192.168.1.1"
},
{
"name": "domain-name-servers",
"data": "8.8.8.8, 1.1.1.1"
}
]
}
]
}
}Automation and Integration with the Kea API
The true power of Kea lies in its Control Agent, which exposes a REST API. This allows for dynamic, real-time management of the DHCP server without restarting services or manually editing configuration files. You can query lease information, add or remove subnets, and check server statistics using simple HTTP requests. This is invaluable for automation with tools like Ansible, Puppet, or custom scripts, a hot topic in Linux automation news.
For example, you could use a simple curl command to retrieve statistics from a running Kea server:
#!/bin/bash
# A simple script to query Kea DHCPv4 statistics via its API
KEA_CTRL_AGENT_URL="http://127.0.0.1:8000"
# Construct the JSON payload for the command
JSON_PAYLOAD=$(cat <<EOF
{
"command": "statistic-get",
"service": [ "dhcp4" ],
"arguments": { "name": "packets-received" }
}
EOF
)
# Send the command to the Kea Control Agent
curl -X POST -H "Content-Type: application/json" -d "$JSON_PAYLOAD" "$KEA_CTRL_AGENT_URL"
This level of programmability makes Kea the clear choice for large-scale, dynamic, and cloud-native environments, reflecting the direction of modern Linux cloud news.
Best Practices, Security, and Troubleshooting
Regardless of the DHCP server you choose, adhering to best practices is crucial for a stable and secure network. The principles of network security and administration are universal, whether you’re using Kali Linux news for penetration testing or deploying a production web server.
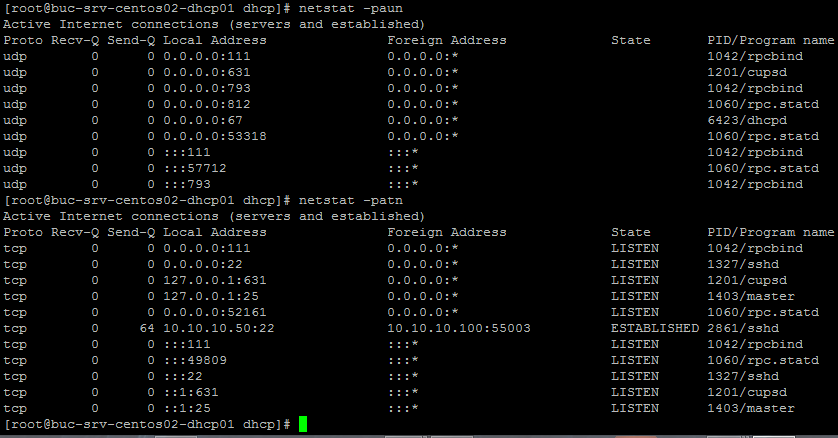
Securing Your DHCP Server
A rogue DHCP server can bring a network to its knees by handing out incorrect IP addresses and malicious DNS server information. To combat this, use DHCP snooping features on managed switches. On the server itself, employ a firewall using nftables or the older iptables to ensure that only legitimate DHCP traffic on UDP ports 67 and 68 is processed. This is a fundamental aspect of Linux security news. Additionally, run the DHCP daemon under a dedicated, unprivileged user account to limit potential damage if the service is ever compromised.

Monitoring and Logging
Effective monitoring is non-negotiable. Keep a close eye on your DHCP lease pools to prevent exhaustion, which would stop new devices from joining the network. Use tools like journalctl on systemd-based systems to review logs for errors or unusual activity. For more advanced setups, integrate your DHCP server’s metrics into a monitoring stack like Prometheus and Grafana, a common pattern in Linux observability news, to visualize lease usage over time and set up alerts.
High Availability and Failover
In any critical environment, DHCP cannot be a single point of failure. Both dhcpd and Kea support high-availability configurations. The classic DHCP failover protocol allows two servers to synchronize their lease databases and act as a hot standby for each other. Kea offers a more modern high-availability mode that provides faster and more robust failover. Implementing this is a standard practice for enterprise-grade deployments discussed in RHCE news and other certification tracks.
Conclusion: Choosing the Right Tool for the Job
The world of Linux DHCP is more vibrant and relevant than ever. The landscape offers a clear progression of tools tailored to different needs. The classic ISC dhcpd, while entering its twilight years, remains a powerful and stable workhorse for countless existing networks, its deep feature set and predictable behavior making it a trusted foundation. For simpler, integrated needs, dnsmasq provides an elegant and lightweight solution that combines essential services with minimal fuss, making it a favorite in the home lab and embedded communities. Looking forward, Kea DHCP represents the future, with its modern architecture, API-driven management, and high-performance design making it the definitive choice for new, large-scale, and automated deployments.
For any Linux administrator, mastering these tools is not just about assigning IP addresses; it’s about understanding the core of network automation and reliability. The right choice depends entirely on your environment’s scale, complexity, and management philosophy. The good news is that the Linux ecosystem provides a world-class, open-source solution for every possible scenario, reinforcing its position as the ultimate platform for building and managing modern networks.



