
Your “Quick Fix” for Permission Errors is a Security Nightmare
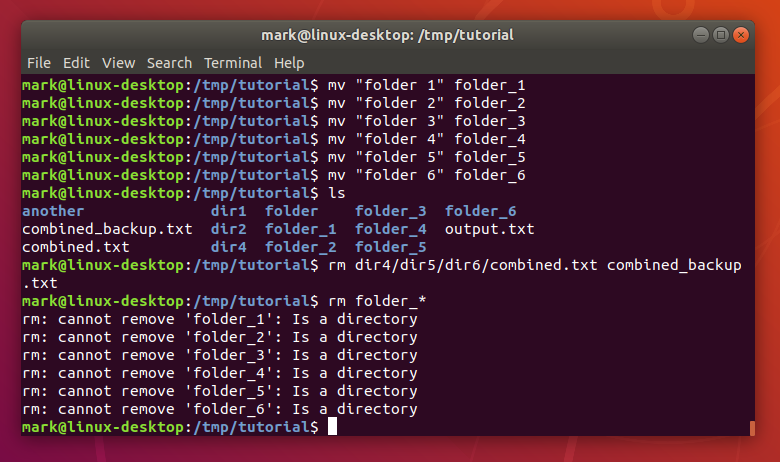
Actually, I should clarify — I looked at the audit logs last Tuesday and wanted to scream. Not a little frustration sigh, but a full-on, scream-into-a-pillow moment. A junior dev, bless his heart, had “fixed” a permission denied error on our staging server by running the forbidden command. You know the one.
chmod -R 777 /var/www/html
It worked. The app started writing logs again. But he basically just unlocked the front door, the back door, and the windows, then put up a neon sign saying “Free data inside.” This isn’t 1999. We aren’t setting up a local LAMP stack for a high school project. We are running production workloads on RHEL 9.5, and frankly, I expected better.
The “It Works” Trap
Here’s the thing about Linux file permissions: they are annoying by design. And they are supposed to get in your way. If the web server user (www-data or nginx usually) can’t write to a directory, that is a feature, not a bug. It means if someone manages to pop a shell through your web app, they can’t just overwrite your system binaries or inject a backdoor into your startup scripts.
But when you broad-stroke permissions to 777 (read, write, and execute for everyone), you remove that layer of defense. And I see this constantly in Dockerfiles too. People get an EACCES error during the build, panic, and throw a chmod 777 in the RUN instruction just to get the build green. I saw a container image on Docker Hub last month — downloaded 50,000 times — that had the entire application code world-writable. One exploit in the app, and the attacker could rewrite the source code on the fly. Terrifying.
The Silent Killer: SUID Binaries
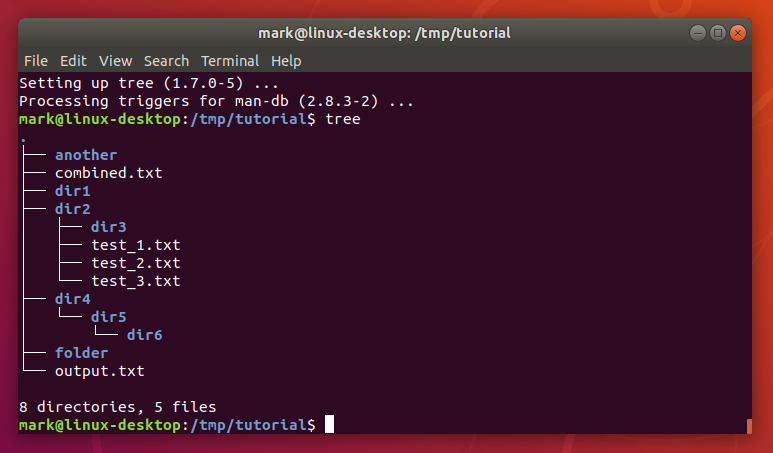
While 777 is loud and stupid, SUID (Set User ID) misconfigurations are quiet and deadly. These are files that run with the permissions of the file owner (usually root), not the user running them. You need them for things like passwd or sudo. You do not need them for your custom backup script.
I ran a scan on a legacy box we inherited — running an ancient CentOS stream — and found vim with the SUID bit set. Do you know what that means? It means any user on the system could open /etc/shadow, edit it, and change the root password. Game over. It took me less than 12 seconds to escalate privileges.
And if you haven’t audited your SUID binaries since the start of 2026, do it now. Seriously. Open a terminal.
# Find all SUID files owned by root
find / -user root -perm -4000 -print 2>/dev/nullIf you see anything in that list that isn’t a standard system utility (like ping, su, mount), you need to ask some hard questions. I once found a python script in there. A python script! Running as root! I almost quit on the spot.
The “Group” Blind Spot
And everyone focuses on the Owner (user) and Others (world), but the Group permission is where the subtle bugs live. I spent three hours debugging a deployment failure on our Kubernetes cluster last month. The issue? The CI/CD runner was in the docker group, but the socket file permissions had drifted after a package update.
Most distros are getting better at this. Ubuntu 24.04 LTS defaults to pretty sane umasks1. But if you have multiple users — say, developers ssh-ing into a dev box — shared group writability (g+w) is a mess waiting to happen. If User A creates a file that User B needs to edit, and the umask is 022, User B is blocked. So they sudo chmod 777 it. And the cycle of stupidity continues.
Use Access Control Lists (ACLs). Please. setfacl has been around forever. It allows you to say “User A and User B can write to this directory” without opening it up to the entire staff group or the world.
# Give 'john' write access without changing group ownership
setfacl -m u:john:rwx /var/www/project/logsI started enforcing ACLs on our shared storage mounts back in Q4 2025, and the number of “permission denied” tickets dropped by about 60%. It’s cleaner, it’s safer, and it doesn’t make security auditors cry.
Unowned Files: The Ghosts in the Machine
And here is a scenario that happens more than you think. You delete a user account, say jdoe (UID 1005). But you forget to wipe their home directory or some temp files they owned in /var/tmp. Those files are now owned by UID 1005, which no longer maps to a name.
Six months later, you create a new service account for your shiny new monitoring tool. The system assigns it the next available UID… 1005. Suddenly, your monitoring tool owns jdoe‘s old files. If those files contained sensitive scripts or config data, your monitoring tool now has access it shouldn’t. Or worse, if jdoe left a malicious script set to run on cron (which you also forgot to clear), the new user inherits that execution context.
And I run this check every time I decommission a user. It saved my bacon on a client audit just two weeks ago:
# Find files not owned by any valid user
find / -nouser -printFixing It Without Nuke-and-Pave
But look, I get it. Permissions are tedious. When you’re trying to ship code, a 403 Forbidden feels like a personal insult. But sloppy permissions are low-hanging fruit for attackers. They don’t need a zero-day kernel exploit if you left the config file world-readable.
So stop guessing. Stop using 777. Learn how chown and chgrp actually work. Use groups effectively. And for the love of everything holy, check your SUID bits. If I have to fix one more server where /etc/ is writable by the web user, I’m going to switch to farming2.
Questions readers ask
Why is chmod -R 777 /var/www/html considered a security risk on production servers?
Setting 777 permissions grants read, write, and execute access to everyone, removing a critical defense layer. If an attacker exploits your web app, they can overwrite system binaries, inject backdoors into startup scripts, or modify application source code on the fly. The article describes a Docker Hub image downloaded 50,000 times with world-writable code as a terrifying example of this anti-pattern.
How do I find SUID binaries on Linux that could allow privilege escalation?
Run this command as root: find / -user root -perm -4000 -print 2>/dev/null. This locates all files owned by root with the SUID bit set, meaning they execute with root permissions regardless of who runs them. Anything beyond standard utilities like ping, su, or mount warrants investigation. The author found vim with SUID set on a legacy CentOS box, allowing any user to edit /etc/shadow and escalate to root in 12 seconds.
How do I give one user write access to a directory without using chmod 777?
Use Access Control Lists with setfacl. For example, setfacl -m u:john:rwx /var/www/project/logs grants user john write access without changing group ownership or opening permissions to the entire group or world. The author enforced ACLs on shared storage mounts starting Q4 2025 and saw permission denied tickets drop by roughly 60%. It’s cleaner, safer, and avoids the cycle of escalating to 777.
What happens to files owned by a deleted Linux user account?
When you delete a user like jdoe (UID 1005) but leave their files behind, those files remain owned by the orphaned UID. When you later create a new service account, the system may reassign UID 1005, giving the new account ownership of the old files, including any sensitive scripts or cron jobs. Detect these orphaned files by running find / -nouser -print before decommissioning users.



