Securing Your Linux Infrastructure: A Deep Dive into Detecting and Mitigating Stealthy Rootkit-based Trojans
Linux has become the undisputed backbone of modern computing, powering everything from massive cloud deployments on AWS and Azure to the smallest Internet of Things (IoT) devices. Its stability, open-source nature, and flexibility have made it the go-to choice for servers, embedded systems, and critical infrastructure worldwide. However, this ubiquity also paints a large target on its back. As highlighted by recent Linux security news, threat actors are continuously developing more sophisticated malware to compromise these systems. Among the most insidious threats are Remote Access Trojans (RATs) that leverage rootkits to achieve deep, persistent, and often invisible access.
These advanced threats are a far cry from simple scripts. They are meticulously crafted to evade traditional detection methods, embedding themselves deep within the operating system. Once active, they can exfiltrate sensitive data, participate in botnets, or serve as a beachhead for broader network intrusions. For system administrators, DevOps engineers, and security professionals, understanding the mechanics of these threats is the first step toward building a resilient defense. This article provides a comprehensive technical guide to understanding, detecting, and mitigating rootkit-based RATs targeting the diverse Linux ecosystem, from enterprise servers running Red Hat news-making distributions to edge devices in the world of Linux embedded news.
Understanding the Dual Threat: The Anatomy of a Rootkit-RAT
To effectively combat this class of malware, it’s crucial to understand its two core components: the Remote Access Trojan (RAT) and the rootkit. While they serve different purposes, their combination creates a formidable security challenge.
What is a Remote Access Trojan (RAT)?
A RAT is a type of malware that provides an attacker with covert, administrative-level control over a compromised system. Unlike a simple backdoor, a RAT offers a rich feature set, often including:
- Remote Shell Access: Executing arbitrary commands as if the attacker were logged in directly.
- File System Management: Uploading, downloading, modifying, and deleting files.
- Process and Service Control: Starting, stopping, and manipulating running processes.
- Data Exfiltration: Searching for and stealing sensitive information like credentials, database dumps, and configuration files.
- Keystroke Logging and Screen Capture: Spying on user activity on desktop systems.
The RAT is the “brain” of the operation, carrying out the attacker’s objectives. However, its activity can be noisy and easily detected by monitoring tools. This is where the rootkit comes in.
The Role of the Rootkit: A Cloak of Invisibility
A rootkit’s primary function is stealth. It actively modifies the host operating system to hide the presence and activities of the malware. This is achieved by intercepting and altering the output of standard system calls and utilities. Rootkits can be broadly categorized into two types:
- User-mode Rootkits: These operate at the application layer, often by replacing system binaries (like
ls,ps,netstat) with trojanized versions or by using techniques likeLD_PRELOADto inject malicious shared libraries into processes. - Kernel-mode Rootkits: These are far more powerful and dangerous. They operate with the highest privileges by inserting themselves directly into the Linux kernel, often as a malicious Linux Kernel Module (LKM). They can manipulate core kernel data structures to hide files, directories, processes, and network connections from the entire system.
When a RAT is paired with a rootkit, an administrator running ps aux | grep suspicious will see nothing, a call to ls -l /usr/bin will show no malicious files, and netstat -anp will not reveal the attacker’s C2 (Command and Control) connection. The system lies to itself, making detection incredibly difficult.

Detection and Forensic Analysis: Pulling Back the Curtain
Detecting a rootkit-based threat requires moving beyond standard system utilities and employing specialized tools and techniques that can identify discrepancies between the system’s expected state and its actual state.
Initial Triage and Behavioral Analysis
Even the stealthiest malware can leave subtle traces. The first step is often to investigate unexplained system behavior, such as a sudden spike in CPU usage, unexpected outbound network traffic, or strange log entries in journalctl. While the rootkit may hide the specific process, the system-wide resource consumption is harder to mask completely.
A simple but effective initial check is to look for files that have been recently modified in critical system directories. While a rootkit can tamper with timestamps (a technique known as “timestomping”), this is not always perfectly executed.
#!/bin/bash
# A simple script to find recently modified files in key system directories.
# This is a basic check and can be fooled, but is a good starting point.
echo "--- Checking for files modified in the last 2 days ---"
find /bin /sbin /usr/bin /usr/sbin /etc /lib /lib64 -mtime -2 -type f -ls
echo "\n--- Checking for files with immutable flag (less common for malware, but good to check) ---"
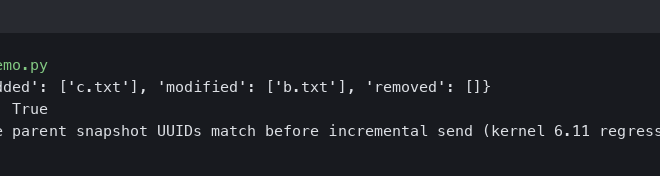
lsattr -R /etc 2>/dev/null | grep 'i'Specialized Rootkit Scanners
Since standard tools can be compromised, you must use tools designed specifically to look for rootkits. Two of the most well-known are chkrootkit and rkhunter (Rootkit Hunter). These utilities work by:
- Signature Scanning: Searching the filesystem for files and directories associated with known rootkits.
- Binary Comparison: Comparing the properties of essential system binaries (like
login,ps,sshd) against a database of known-good values. - System Checks: Looking for signs of kernel-level manipulation, such as hooked system calls or hidden processes.
Running these tools is a critical step in any security audit. Whether you’re managing a server based on Debian news or a fleet of devices from the Raspberry Pi Linux news world, these tools are invaluable.
# Installation on Debian/Ubuntu-based systems
sudo apt-get update
sudo apt-get install -y chkrootkit rkhunter
# First, update rkhunter's data files
sudo rkhunter --update
sudo rkhunter --propupd
# Run a system check with rkhunter (press Enter to proceed through warnings)
# Review the log file at /var/log/rkhunter.log for details
sudo rkhunter --check --sk
# Run chkrootkit (note: it may produce false positives, requires careful analysis)
sudo chkrootkitLive vs. Offline Analysis
A key challenge is that a running kernel infected with a rootkit cannot be trusted. For a truly thorough investigation, forensic analysis should be performed “offline.” This involves booting the suspect system from a trusted, clean live environment (like a Kali Linux or a generic rescue USB) and mounting the original filesystem as read-only. From this clean environment, you can inspect files, analyze logs, and run scans without the active rootkit interfering with your tools.
Advanced Mitigation and Proactive Hardening

Detection is reactive. A robust security posture focuses on proactive hardening to prevent malware from gaining a foothold in the first place or to severely limit its capabilities if it does.
Leveraging Linux Security Modules (LSMs)
Modern Linux distributions, from Fedora news releases to enterprise platforms like RHEL and SUSE, include powerful mandatory access control (MAC) frameworks like SELinux and AppArmor. Unlike traditional file permissions, LSMs can confine applications to a strict set of allowed actions. An AppArmor profile, for example, can prevent a web server from executing programs in /tmp or writing to /etc, even if it’s compromised and running as root. This can effectively neuter a RAT, preventing it from performing most of its malicious functions.
# Example of a simple AppArmor profile for a hypothetical service
# This would be located in /etc/apparmor.d/usr.sbin.my-web-service
#include <tunables/global>
profile my_web_service /usr/sbin/my-web-service {
#include <abstractions/base>
#include <abstractions/nameservice>
#include <abstractions/networking>
# Allow reading its own configuration
/etc/my-web-service.conf r,
# Allow reading web content
/var/www/html/** r,
# Allow writing to log files
/var/log/my-web-service.log w,
# Explicitly deny execution of shells or other interpreters
deny /bin/sh x,
deny /usr/bin/python* x,
deny /usr/bin/perl x,
# Deny writing to most of the filesystem
deny /** w,
}Immutable Infrastructure and Read-Only Filesystems
A powerful paradigm, especially in Linux embedded news and container orchestration (Kubernetes Linux news), is the concept of immutable infrastructure. If the root filesystem is mounted as read-only, it becomes impossible for malware to persist across reboots by modifying system files or installing new services. Systems like Fedora Silverblue and many IoT platforms use this approach, applying updates by replacing the entire OS image rather than patching it live. This greatly reduces the attack surface for persistent threats.
Real-time Threat Detection with eBPF

For high-security environments, runtime monitoring is essential. Modern tools like Falco and Cilium’s Tetragon leverage eBPF (extended Berkeley Packet Filter) to safely instrument the Linux kernel. They can monitor system calls in real-time and detect anomalous behavior based on a set of rules, providing instant alerts for suspicious activity that a rootkit might otherwise hide.
# Example Falco rule to detect a shell being run inside a container
# This helps catch reverse shells or interactive sessions opened by malware.
- rule: Terminal shell in container
desc: A shell was spawned in a container with an attached terminal.
condition: >
spawned_process and container.id != host and proc.name in (shell_binaries) and tty != 0
output: >
A shell was spawned in a container (user=%user.name container_id=%container.id container_name=%container.name proc_name=%proc.name
command=%proc.cmdline terminal=%proc.tty)
priority:
NOTICE
tags: [container, shell]Best Practices for a Secure Linux Ecosystem
Technology alone is not enough. A strong security posture relies on a foundation of disciplined operational practices across your entire infrastructure, whether you’re following Arch Linux news for a custom setup or managing a fleet of Ubuntu news-driven servers.
- Aggressive Patch Management: The vast majority of compromises exploit known, unpatched vulnerabilities. Use automated tools like
unattended-upgradesor enterprise solutions like Red Hat Satellite to ensure systems are always up-to-date. Keep an eye on Linux kernel news for critical security advisories. - Principle of Least Privilege: Run all services with dedicated, unprivileged user accounts. Avoid using the root account for daily tasks. Containerize applications to isolate them from the host system and each other.
- Network Segmentation and Firewalling: Use firewalls like
nftablesto enforce a “default deny” policy for both ingress and egress traffic. Only allow the specific ports and protocols required for an application to function. This can prevent a RAT from “phoning home” to its C2 server. - Secure SSH Configuration: Disable root login, enforce key-based authentication instead of passwords, and use a non-standard port to reduce automated attacks. Keep your OpenSSH news sources bookmarked for updates.
- Regular Backups and Audits: Maintain regular, tested, and offline backups using tools like Borgbackup or Restic. This ensures you can recover from a destructive attack. Periodically audit system configurations and user accounts to look for signs of compromise.
Conclusion: Vigilance is the Best Defense
The threat of sophisticated, stealthy malware like rootkit-based RATs is a persistent reality in the modern IT landscape. As Linux continues to dominate server and embedded markets, these attacks will only become more common and refined. However, the Linux ecosystem also provides a powerful and flexible set of tools to defend against them.
By understanding the dual nature of these threats, security professionals can move beyond reactive, signature-based detection. The key to a resilient infrastructure lies in a multi-layered, proactive strategy: hardening the kernel with LSMs, implementing immutable patterns, monitoring system behavior in real-time, and adhering to strict operational security hygiene. Security is not a destination but a continuous process of adaptation and vigilance. By embracing these principles, you can significantly raise the bar for attackers and ensure your Linux systems remain a secure and reliable foundation for your operations.