
Mastering MariaDB on Linux: A Deep Dive into Root Password Recovery and Security Best Practices
In the world of Linux server administration, managing databases is a core responsibility. MariaDB, a high-performance, open-source relational database, stands as a cornerstone of the LAMP stack and a popular choice across countless distributions, from Debian and Ubuntu to Fedora and Red Hat Enterprise Linux derivatives like Rocky Linux and AlmaLinux. It’s a testament to the vibrant open-source ecosystem celebrated in MariaDB Linux news and Linux databases news. However, even the most seasoned administrator can face a common, heart-stopping problem: a forgotten root password for a critical database instance. This situation can bring operations to a grinding halt, but fortunately, the flexibility of Linux provides a clear path to recovery.
This article provides a comprehensive guide to recovering a lost MariaDB root password on a Linux system. We will walk through the precise steps to regain access, explaining the “why” behind each command. More importantly, we’ll move beyond simple recovery and explore proactive security measures, user management best practices, and authentication mechanisms that can prevent this issue from recurring and harden your database against unauthorized access. This is essential knowledge for anyone involved in Linux administration news and modern DevOps practices.
Understanding MariaDB Authentication and the Root User
Before we dive into the recovery process, it’s crucial to understand how MariaDB handles user authentication and the special role of the root user. This foundational knowledge will clarify why the recovery steps work and how to better manage your database environment moving forward.
The Privileged ‘root’ Account
In MariaDB, the root user is the superuser account. It’s important to distinguish this from the Linux system’s root user. The MariaDB root user has all privileges, including the ability to create and drop databases, create and manage other users, and alter global system variables. By default, this user is often configured to connect only from localhost for security reasons. The ultimate goal of any administrator should be to use this account sparingly, primarily for administrative tasks, and not for application connections.
How MariaDB Authentication Works
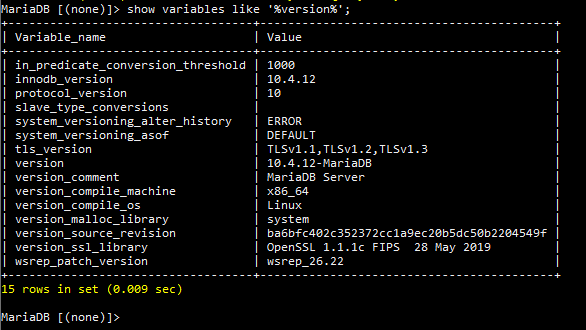
When a client attempts to connect, MariaDB consults its grant tables, which are stored in the special mysql database. The primary table involved is mysql.user (or mysql.global_priv in newer versions). This table contains a list of users, the hosts they can connect from, their encrypted passwords, and the authentication plugin to be used. Common plugins include mysql_native_password for traditional password hashing and unix_socket, which allows users to authenticate using their Linux system credentials. You can inspect your current user configuration with a simple query if you have access.
-- This query shows the user, their allowed host, and the authentication method.
SELECT user, host, plugin FROM mysql.user;
-- Example Output:
-- +-------------+-----------+-----------------------+
-- | user | host | plugin |
-- +-------------+-----------+-----------------------+
-- | root | localhost | unix_socket |
-- | mariadb.sys | localhost | mysql_native_password |
-- | webapp | localhost | mysql_native_password |
-- +-------------+-----------+-----------------------+The recovery process we are about to explore works by temporarily starting the MariaDB server in a special mode that completely bypasses these grant tables, allowing us to connect and make changes without any authentication checks.
The Step-by-Step Password Recovery Process on Linux
This procedure is a powerful administrative tool and should be performed with care on a production server. It requires root-level shell access to the Linux machine hosting the MariaDB instance. The commands shown are based on systems using systemd, which is standard in modern distributions featured in systemd news, including Ubuntu, Debian, Fedora, and CentOS.

Code error message on screen – Scripting tool does not return line error consiten… – Esri Community
Step 1: Stop the MariaDB Service
First, you must stop the running MariaDB service to prevent any conflicts and ensure a clean state before restarting it in safe mode. This is a standard task in Linux server management.
sudo systemctl stop mariadb
# On some systems like Debian/Ubuntu, the service might be named mysql
# sudo systemctl stop mysqlStep 2: Restart MariaDB in Safe Mode
Next, we will manually start the MariaDB server process with two critical flags. The --skip-grant-tables flag tells the server not to load the user privilege tables, effectively disabling all authentication and permission checks. The --skip-networking flag is an essential security precaution that prevents any remote connections while the database is in this vulnerable, unprotected state.
sudo mysqld_safe --skip-grant-tables --skip-networking &The & at the end runs the process in the background, returning your terminal prompt.
Step 3: Connect and Reset the Password
With the server running in safe mode, you can now connect to it as the root user without providing a password.
sudo mysql -u rootOnce inside the MariaDB client, you need to execute a few SQL commands. First, run FLUSH PRIVILEGES;. This command forces the server to reload the grant tables, which is necessary before you can use commands like ALTER USER. Then, use the ALTER USER statement to set a new, strong password. This is the modern and recommended syntax.
-- This command is essential to enable user management commands.
FLUSH PRIVILEGES;
-- Use this command for modern MariaDB versions (10.4+) to set a new password.
ALTER USER 'root'@'localhost' IDENTIFIED BY 'YourNewStrong!Password123';
-- After the command succeeds, exit the client.
EXIT;Step 4: Clean Up and Restart Normally
Now you must stop the manually started, insecure MariaDB process. The process ID (PID) is typically stored in a file. You can use the kill command to terminate it gracefully. After that, restart the service normally using systemctl.
# Find the PID and stop the manually started process
sudo kill `cat /var/run/mariadb/mariadb.pid`
# Wait a few seconds for the process to terminate completely
sleep 5
# Restart the service the proper way
sudo systemctl start mariadbStep 5: Verify the New Password
Finally, test your new password to confirm that the recovery was successful.
Code error message on screen – Using AutoItLibrary or FLAui of Robot Framework Libraries with …
mysql -u root -p
# You will be prompted to enter your new password.If you can log in, you have successfully recovered your MariaDB root account. This process is a powerful example of the control offered by the Linux environment, a frequent topic in Linux troubleshooting news.
Beyond Recovery: Proactive Security and Administration
Recovering a password is a reactive measure. A truly robust strategy involves proactive security practices to minimize risks and improve manageability. This aligns with the broader themes of Linux security news and building resilient systems.
The Principle of Least Privilege
Never use the MariaDB root user for your applications. Instead, create dedicated users for each application with the minimum set of privileges they need to function. This limits the potential damage if an application’s credentials are compromised. For example, a web application that only reads and writes to a specific database doesn’t need permissions to create new users or drop other databases. Wrapping user creation and grant statements in a transaction ensures that all changes are applied atomically.
START TRANSACTION;
-- Create a dedicated user for a blog application, restricted to localhost.
CREATE USER 'blog_app'@'localhost' IDENTIFIED BY 'AnotherSecureP@ssw0rd!';
-- Grant only the necessary DML privileges on the 'blog_db' database.
-- This schema should already be designed with appropriate indexes for performance.
GRANT SELECT, INSERT, UPDATE, DELETE ON `blog_db`.* TO 'blog_app'@'localhost';
-- Reload privileges to apply the changes immediately.
FLUSH PRIVILEGES;
COMMIT;Leveraging Socket Authentication for Local Administration
Many modern Linux distributions, including those featured in recent Debian news and Fedora news, configure MariaDB’s root user to authenticate via the unix_socket plugin by default. This plugin allows the Linux system’s root user to log into the MariaDB root account without a password by simply running sudo mysql. Authentication is handled by the operating system, verifying that the user running the command is indeed root. This is both highly secure (as it requires root shell access) and convenient for administrative tasks, eliminating the need to store or remember a separate database root password.
Code error message on screen – Official | Search by keyword
-- Switch the 'root'@'localhost' user to use socket authentication.
-- Run this query as the MariaDB root user.
ALTER USER 'root'@'localhost' IDENTIFIED VIA unix_socket;
-- After this, you can log in from the Linux shell using:
-- sudo mysqlBest Practices and Common Pitfalls
To round out your MariaDB management skills, it’s vital to internalize best practices and be aware of common mistakes that can lead to security vulnerabilities or operational headaches.
Security and Maintenance Best Practices
- Use Strong Passwords: For any user not using socket authentication, enforce strong, unique passwords.Run `mysql_secure_installation`: After any new MariaDB installation, run this interactive script to remove anonymous users, disallow remote root login, and remove the test database.Audit Regularly: Periodically run
SELECT user, host FROM mysql.user; to review who has access to your database server and remove any unnecessary accounts.Keep Systems Updated: Regularly update your MariaDB packages and the underlying Linux operating system. Following Linux kernel news and your distribution’s security advisories (e.g., from apt news or dnf news) is crucial for patching vulnerabilities.Backup Your Data: Implement a robust backup strategy using tools like mariadb-dump or filesystem-level tools like Btrfs snapshots.Common Pitfalls to Avoid
- Forgetting `FLUSH PRIVILEGES`: When you modify grant tables with
GRANT, REVOKE, or ALTER USER, the changes are not always applied to currently active sessions until you flush the privileges. It’s a critical step.Leaving the Server in Safe Mode: The biggest mistake is forgetting to kill the insecure mysqld_safe process and restart the service normally. An exposed server with no authentication is a major security risk.Editing User Tables Directly: Avoid using UPDATE or DELETE directly on the mysql.user table. This can lead to corrupted grant tables. Always use the designated SQL commands like CREATE USER, DROP USER, and ALTER USER.Conclusion
Losing access to your MariaDB root account on a Linux server can be a stressful event, but it is far from a catastrophe. By leveraging root shell access and understanding how to start the server in a safe mode, you can reliably and securely regain control. This process underscores the power and transparency of the open-source tools that dominate the Linux server news landscape.
However, the true lesson is in proactive administration. By embracing the principle of least privilege, creating dedicated application users, utilizing secure authentication methods like unix_socket, and performing regular security audits, you can build a more resilient and secure database infrastructure. These practices not only prevent lockouts but also form the bedrock of professional database management, ensuring the integrity and availability of your critical data on any Linux platform.



