Securing Your Network with Dnsmasq: A Deep Dive into Configuration, Best Practices, and Security Hardening
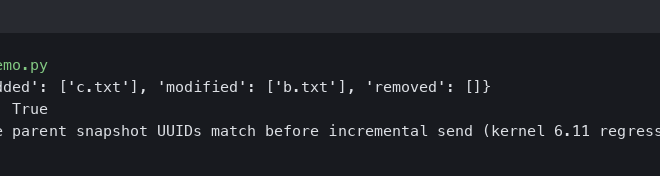
Introduction
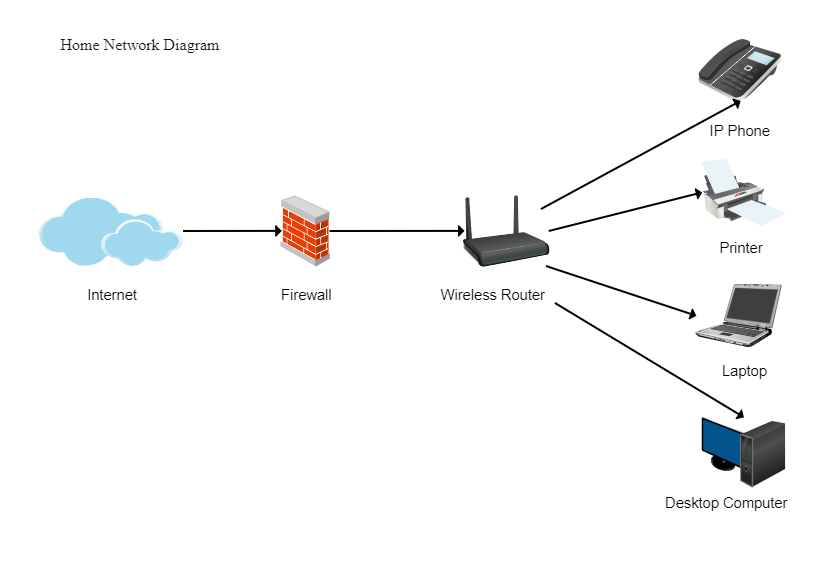
In the vast ecosystem of Linux networking tools, few are as ubiquitous yet as unassuming as Dnsmasq. This lightweight, versatile server provides essential network services—DNS forwarding, DHCP, and router advertisement—making it a cornerstone of countless home networks, small office setups, IoT devices, and even complex development environments. Its small footprint and simple configuration have led to its integration into a wide array of Linux distributions, from server-focused platforms like Ubuntu Server and CentOS to embedded systems powering routers and smart devices.
However, this widespread adoption means that the security and proper configuration of Dnsmasq are of paramount importance. A misconfigured or outdated instance can become a significant vulnerability, exposing a network to threats like DNS spoofing, cache poisoning, and denial-of-service attacks. Recent discussions within the Linux security news community have highlighted the ongoing need for vigilance. This article provides a comprehensive technical guide to understanding, implementing, and hardening Dnsmasq. We will explore its core functions, walk through practical configurations, delve into advanced security features, and establish best practices to ensure your network remains robust and secure.
Understanding Dnsmasq’s Core Functionality
At its heart, Dnsmasq is designed to simplify network management for small-scale LANs. It integrates several key services into a single, cohesive package, eliminating the need to configure and maintain separate, more complex daemons like BIND and ISC DHCPD.
DNS Caching and Forwarding
The primary function of Dnsmasq is to act as a local DNS caching server. When a client on your network requests a domain name (e.g., www.example.com), Dnsmasq intercepts the query. If the answer is already in its cache, it returns it immediately, resulting in a near-instantaneous response. If not, it forwards the query to one or more configured upstream DNS servers (like Google’s 8.8.8.8 or Cloudflare’s 1.1.1.1), caches the result, and then passes it back to the client. This significantly speeds up browsing for frequently visited sites and reduces external bandwidth usage.
A minimal configuration for DNS forwarding looks like this:
# /etc/dnsmasq.conf
# Do not read /etc/resolv.conf. We will specify our own upstream servers.
no-resolv
# Specify upstream DNS servers
server=8.8.8.8
server=1.1.1.1
# Increase the cache size for better performance
# The default is 150.
cache-size=1000Integrated DHCP Server
Dnsmasq also includes a full-featured DHCP server. It can automatically assign IP addresses, subnet masks, default gateways, and DNS server information to clients on the network. A key advantage of Dnsmasq is its tight integration between its DNS and DHCP components.
Seamless DNS and DHCP Integration
When the DHCP server assigns an IP address to a client, it can automatically register the client’s hostname in the local DNS. This allows you to resolve local machine names without any manual configuration. For example, a laptop that receives an IP address and reports its hostname as “my-laptop” can be immediately reached at my-laptop.localnet (assuming your local domain is “localnet”). This is incredibly useful for home and development networks.
# /etc/dnsmasq.conf
# Set the domain for your local network.
# This will be appended to hostnames.
domain=localnet
# Enable the DHCP server. Assign IPs from 192.168.1.50 to 192.168.1.150
# with a 12-hour lease time.
dhcp-range=192.168.1.50,192.168.1.150,12h
# Provide the default gateway option to clients.
dhcp-option=option:router,192.168.1.1
# Provide the DNS server option to clients. Here, we tell them to use dnsmasq itself.
dhcp-option=option:dns-server,192.168.1.1This simple configuration creates a fully functional and integrated DNS and DHCP environment, a task that would be far more complex with separate tools. This ease of use is a major driver of Dnsmasq’s popularity across the entire spectrum of Linux news, from Raspberry Pi Linux news to enterprise Linux server news.
Practical Implementation and Secure Configuration
Deploying Dnsmasq correctly involves more than just enabling its services. A secure setup requires careful attention to which interfaces it listens on and how it interacts with the rest of the system.
Installation on Common Linux Distributions
Dnsmasq is available in the official repositories of nearly all major Linux distributions. Installation is straightforward using standard package managers, a topic frequently covered in Ubuntu news, Debian news, Fedora news, and Arch Linux news.
- Debian / Ubuntu / Linux Mint:
sudo apt update && sudo apt install dnsmasq - Fedora / CentOS / RHEL / Rocky Linux:
sudo dnf install dnsmasq - Arch Linux / Manjaro:
sudo pacman -S dnsmasq
After installation, the service may start automatically. It’s best practice to stop it (sudo systemctl stop dnsmasq) before proceeding with configuration.
Building a Secure Base Configuration
A secure Dnsmasq configuration should explicitly define its operational boundaries. The most critical security measure is to prevent it from listening on public-facing interfaces, which would expose it to the internet and make it a potential vector for DNS amplification attacks.
Here is a well-commented, secure base configuration file suitable for a typical home or small office network.
# /etc/dnsmasq.conf
# ===================================================================
# General Settings
# ===================================================================
# Set the domain for the local network.
domain=lan
# Prevent Dnsmasq from forwarding simple names (without a dot)
domain-needed
# Prevent Dnsmasq from forwarding addresses in the non-routed address spaces.
bogus-priv
# ===================================================================
# Interface and Security Settings
# ===================================================================
# Listen only on the specified interface(s). Replace 'eth1' with your LAN interface.
# This is a CRITICAL security setting.
interface=eth1
# Alternatively, you can specify an IP address to listen on.
# listen-address=127.0.0.1,192.168.1.1
# For an extra layer of security, bind only to the specified interfaces.
# This prevents Dnsmasq from accidentally listening on all interfaces if 'eth1' goes down.
bind-interfaces
# ===================================================================
# DNS Settings
# ===================================================================
# Do not use /etc/resolv.conf
no-resolv
# Specify upstream DNS servers. These are Cloudflare's.
server=1.1.1.1
server=1.0.0.1
# Read host entries from /etc/hosts
no-hosts
# Read custom host entries from another file for easier management.
addn-hosts=/etc/dnsmasq.hosts
# Set the DNS cache size.
cache-size=2048
# ===================================================================
# DHCP Settings
# ===================================================================
# Enable DHCP, set the address range, and lease time.
dhcp-range=192.168.1.100,192.168.1.200,24h
# Set the default gateway for clients.
dhcp-option=option:router,192.168.1.1
# Set the DNS server for clients (itself).
dhcp-option=option:dns-server,192.168.1.1
# Enable logging for DHCP events.
log-dhcpStatic Leases and Local DNS
For servers, printers, or other critical devices, you should assign a static IP address. Dnsmasq makes this easy by mapping a MAC address to a specific IP and hostname.
You can also define custom DNS records for local services, such as a NAS or a web server, directly in the configuration.
# Assign a static IP address to a server using its MAC address.
# The client with MAC aa:bb:cc:dd:ee:ff will always get 192.168.1.10
# and be known as 'fileserver'.
dhcp-host=aa:bb:cc:dd:ee:ff,fileserver,192.168.1.10
# Create a custom DNS record.
# The name 'nas.lan' will resolve to 192.168.1.15.
address=/nas.lan/192.168.1.15
# Create a CNAME (alias) record.
# 'media.lan' will be an alias for 'nas.lan'.
cname=media.lan,nas.lanAdvanced Security Hardening and Features
Beyond the basic setup, Dnsmasq offers several features that can significantly enhance your network’s security posture. Staying current with Linux security news and applying these advanced techniques is crucial for any system administrator.
Mitigating Attacks with DNSSEC
DNS Security Extensions (DNSSEC) is a suite of specifications for securing certain kinds of information provided by DNS. It works by digitally signing DNS records, allowing a client to verify that the information it receives from a DNS server is authentic and has not been tampered with. Dnsmasq can act as a DNSSEC validator.
To enable DNSSEC, you need to provide it with a set of trust anchors, which are the public keys for the root DNS zone. These are typically provided by your distribution.

# /etc/dnsmasq.conf
# Enable DNSSEC validation.
dnssec
# Specify the location of the trust anchors.
# The path may vary by distribution (e.g., /usr/share/dnsmasq-base/trust-anchors.conf on Debian/Ubuntu).
trust-anchor=.,19036,8,2,49AAC11D7B6F6446702E54A1607371607A1A41855200FD2CE1CDDE32F24E8FB5
trust-anchor=.,20326,8,2,E06D44B80B8F1D39A95C0B0D7C65D08458E880409BBC683457104237C7F8EC8DWith dnssec enabled, Dnsmasq will discard any upstream replies that fail validation, protecting your network from cache poisoning attacks.
Content Filtering and Ad-Blocking
Dnsmasq can be used as a simple yet effective tool for network-wide ad-blocking and filtering of malicious domains. The principle is to redirect queries for unwanted domains to a non-routable address like 0.0.0.0. This is the same technique used by the popular Pi-hole project, which leverages Dnsmasq under the hood.
You can manage a large blocklist by placing it in a separate file and using the addn-hosts directive. Here’s a simple shell script to download a popular blocklist and format it for Dnsmasq.
#!/bin/bash
# A script to download and update a Dnsmasq blocklist
BLOCKLIST_URL="https://raw.githubusercontent.com/StevenBlack/hosts/master/hosts"
DNSMASQ_BLOCKLIST_FILE="/etc/dnsmasq.d/blocklist.conf"
echo "Downloading latest blocklist..."
# Use curl to download the list, grep to filter for entries starting with 0.0.0.0,
# and awk to format them for dnsmasq (address=/domain.com/0.0.0.0)
curl -s "$BLOCKLIST_URL" | grep "^0\.0\.0\.0" | awk '{print "address=/"$2"/0.0.0.0"}' > "$DNSMASQ_BLOCKLIST_FILE"
echo "Restarting dnsmasq to apply changes..."
# Use systemctl to restart the service.
# This command is central to systemd news and modern Linux administration.
systemctl restart dnsmasq
echo "Blocklist updated successfully."Running this script periodically via a cron job or a systemd timer keeps your filtering up-to-date.
Best Practices, Performance, and Maintenance
Properly maintaining your Dnsmasq instance is just as important as the initial configuration. This involves regular updates, performance tuning, and adhering to security principles.
Keep Dnsmasq Updated
This is the single most important security practice. Software vulnerabilities are discovered continuously. The developers of Dnsmasq and the security research community are diligent, but patches are only effective if they are applied. As a critical piece of Linux networking news, security advisories for packages like Dnsmasq are released through official channels for all major distributions. Always keep your system’s packages up-to-date.
- On Debian/Ubuntu:
sudo apt update && sudo apt upgrade - On Fedora/RHEL:
sudo dnf upgrade - On Arch Linux:
sudo pacman -Syu
Principle of Least Privilege
By default, Dnsmasq starts as the root user to bind to privileged ports (port 53 for DNS and 67 for DHCP). However, it is designed to drop root privileges after startup and run as a less privileged user. You should explicitly define this user in your configuration to enhance security. If a vulnerability were ever exploited, the attacker’s capabilities would be severely limited.
# /etc/dnsmasq.conf
# Run as the 'dnsmasq' user and group after startup.
# On some systems, the user might be 'nobody'.
user=dnsmasq
group=dnsmasqLogging and Monitoring
Effective logging is essential for troubleshooting and security analysis. Enable query logging to see what requests are being made on your network. On modern systems using systemd, logs can be easily viewed with journalctl.
# Enable full logging for DNS queries.
# This can be verbose, so use it when troubleshooting.
log-queries
# View dnsmasq logs in real-time.
journalctl -u dnsmasq -fMonitoring these logs can help you spot unusual activity, such as a compromised device making thousands of DNS queries to malicious domains, which is a key topic in Linux forensics news and incident response.
Conclusion
Dnsmasq remains an incredibly powerful and efficient tool for managing local network services on Linux. Its simplicity belies a rich feature set that, when configured correctly, provides a fast, reliable, and secure network foundation. From home users to DevOps professionals managing complex container environments with Docker Linux news and Kubernetes Linux news, Dnsmasq has a valuable role to play.
The key takeaways for any administrator are clear: a secure Dnsmasq implementation rests on a foundation of disciplined configuration, proactive security hardening, and diligent maintenance. By binding Dnsmasq to trusted interfaces, enabling modern protections like DNSSEC, and committing to a regular update schedule, you can harness its full potential while safeguarding your network against emerging threats. As the open-source landscape evolves, staying informed through Linux open source news and applying these best practices will ensure your network infrastructure remains both functional and resilient.