
WireGuard Ascendant: From Simple VPN to the Backbone of Zero-Trust Security
WireGuard has rapidly transformed the landscape of virtual private networking. Heralded for its simplicity, state-of-the-art cryptography, and remarkable performance, it has become a first-class citizen within the Linux kernel. This deep integration, a significant piece of Linux kernel news, has solidified its position as the de facto standard for secure point-to-point connections across nearly every major distribution, from Ubuntu news and Debian news to Fedora news and Arch Linux news. However, the story of WireGuard is evolving. Its minimalist design is now being leveraged as a foundational building block for a far more ambitious paradigm: Zero-Trust Network Access (ZTNA). This article explores WireGuard’s journey beyond a simple VPN, delving into how its core principles are enabling a new generation of dynamic, identity-aware security platforms that are reshaping Linux security news and enterprise networking.
The Core of Simplicity: Why WireGuard Won the VPN Race
Before building complex systems on top of WireGuard, it’s crucial to understand why it became so popular. Its design philosophy centers on a few key concepts that differentiate it from legacy solutions like OpenVPN or IPsec. This simplicity is not just an aesthetic choice; it’s a security feature that has profound implications for performance and auditability.
Cryptokey Routing: The Central Innovation
The most elegant concept in WireGuard is Cryptokey Routing. Instead of managing complex tunnels, states, and sessions, WireGuard simply and securely associates a peer’s public key with a list of allowed IP addresses within the tunnel. If a packet arrives on the WireGuard interface with a source IP that matches an allowed IP for a known public key, and it is correctly authenticated, it is accepted. This maps cryptographic identity directly to network routing, dramatically simplifying the entire process. This approach eliminates the need for complex certificate management and reduces the attack surface, a major topic in Linux security news.
A basic server configuration illustrates this principle perfectly. This setup is typically managed with the wg-quick utility, which seamlessly integrates with systemd news for service management on most modern Linux systems.
[Interface]
# Server's private key
PrivateKey = <SERVER_PRIVATE_KEY>
# Virtual IP address for the server
Address = 10.100.0.1/24
# Port to listen on
ListenPort = 51820
# Add nftables/iptables rules on startup
PostUp = nft add table inet wg; nft add chain inet wg postrouting { type nat hook postrouting priority 100 \; }; nft add rule inet wg postrouting oifname eth0 masquerade
# Remove rules on shutdown
PostDown = nft delete table inet wg
[Peer]
# Client 1's public key
PublicKey = <CLIENT_1_PUBLIC_KEY>
# Assign a specific virtual IP to this client
AllowedIPs = 10.100.0.2/32
[Peer]
# Client 2's public key
PublicKey = <CLIENT_2_PUBLIC_KEY>
# Assign a specific virtual IP to this client
AllowedIPs = 10.100.0.3/32In this example, the server knows it should only accept traffic from 10.100.0.2 if it’s cryptographically signed by Client 1’s private key. This static mapping is powerful but also hints at the next evolutionary step: dynamic management.
Building Dynamic Overlay Networks
The static configuration files that make WireGuard easy for personal use become a bottleneck at scale. In a modern cloud-native environment, where services and users are ephemeral, manually editing configuration files is not feasible. This is where programmatic control becomes essential, turning WireGuard from a static VPN into a dynamic overlay network fabric. This is a hot topic in Linux DevOps news and for platforms like Kubernetes Linux news.
Automating Peer Management
The standard wg command-line tool provides the necessary primitives to manage peers on a live interface without restarting it. We can leverage this with scripting languages like Python or Bash to build a simple control plane. This automation is the first step towards a ZTNA architecture, where access is granted and revoked in real-time based on external triggers.
Here is a Python script that demonstrates how to add a new peer to a running WireGuard interface. This could be part of a larger application that provisions access for a new employee or a new server.
import subprocess
import sys
def add_wireguard_peer(interface, public_key, allowed_ips):
"""
Adds a new peer to a running WireGuard interface.
Args:
interface (str): The name of the WireGuard interface (e.g., 'wg0').
public_key (str): The public key of the peer to add.
allowed_ips (str): The comma-separated list of allowed IPs for the peer.
"""
try:
# The 'wg set' command is the core of dynamic management
command = [
"sudo", "wg", "set", interface,
"peer", public_key,
"allowed-ips", allowed_ips
]
print(f"Executing: {' '.join(command)}")
result = subprocess.run(command, check=True, capture_output=True, text=True)
print("Successfully added peer:")
print(f" Public Key: {public_key}")
print(f" Allowed IPs: {allowed_ips}")
except subprocess.CalledProcessError as e:
print(f"Error adding WireGuard peer: {e}", file=sys.stderr)
print(f"Stderr: {e.stderr}", file=sys.stderr)
sys.exit(1)
except FileNotFoundError:
print("Error: 'wg' command not found. Is WireGuard installed?", file=sys.stderr)
sys.exit(1)
if __name__ == "__main__":
if len(sys.argv) != 4:
print(f"Usage: {sys.argv[0]} <interface> <public_key> <allowed_ips>")
print("Example: python3 manage_peer.py wg0 abc...= 10.100.0.4/32")
sys.exit(1)
wg_interface = sys.argv[1]
peer_public_key = sys.argv[2]
peer_allowed_ips = sys.argv[3]
add_wireguard_peer(wg_interface, peer_public_key, peer_allowed_ips)This script uses Python’s subprocess module to call the wg utility, abstracting away the manual command-line work. This is a fundamental pattern used by tools discussed in Ansible news and Terraform Linux news to manage network configurations.
From Overlay Network to Zero-Trust Architecture
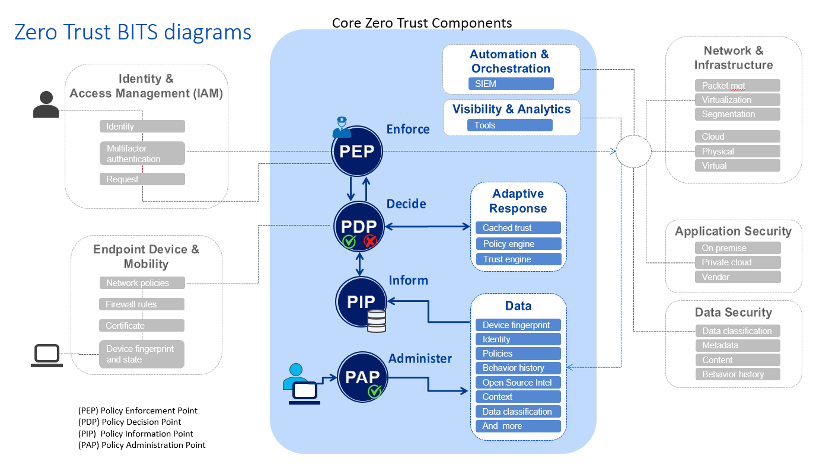
A Zero-Trust Network (ZTNA) operates on the principle of “never trust, always verify.” It assumes no user or device is trusted by default, regardless of its physical or network location. Access is granted on a per-session basis, authenticated and authorized dynamically. WireGuard, with its strong identity-based tunneling, provides the perfect secure transport layer (the “data plane”) for a ZTNA solution. The “control plane” is the intelligence that sits on top, making decisions and configuring the WireGuard data plane.
The Components of a WireGuard-Based ZTNA
- Data Plane (WireGuard): Provides the encrypted, point-to-point tunnels between users, devices, and resources. Its kernel-level performance is critical here.
- Control Plane: A centralized service that manages the entire network. It authenticates users (often via an Identity Provider like Okta or an open-source solution like Keycloak), checks device posture, and dynamically configures the WireGuard peers and their associated firewall rules.
- Identity Provider (IdP): The source of truth for user identity. Integration with an IdP allows the ZTNA to enforce access policies based on user roles and groups.
- Policy Engine: Defines the rules for access. For example, “Users in the ‘developers’ group can access the staging database server on port 5432 from a corporate-managed laptop.”
When a user wants to access a resource, they first authenticate with the control plane via the IdP. The control plane checks their identity, device health, and the relevant policies. If approved, it generates ephemeral WireGuard configurations for both the user’s device and the destination resource’s gateway, allowing a temporary, direct, and encrypted tunnel. This is a major advancement in Linux server news and secure access patterns.
Enforcing Policy with Dynamic Firewalls
A crucial part of ZTNA is enforcing the principle of least privilege. Even after a user is on the VPN, they should only be able to access specifically authorized resources. This is where dynamic firewalling comes in. The control plane must not only configure WireGuard’s AllowedIPs but also push precise firewall rules to the gateway or server. Modern tools like nftables are ideal for this due to their atomic ruleset updates and superior performance, a frequent topic in Linux firewall news.
Here’s an example of how nftables could be used to grant a specific WireGuard peer access to a PostgreSQL database server.
#!/bin/bash
# This script would be run by the control plane on the gateway server
# Peer's assigned IP within the WireGuard tunnel
PEER_IP="10.100.0.4"
# The internal IP of the database server
DB_SERVER_IP="192.168.1.50"
DB_PORT="5432"
WG_INTERFACE="wg0"
# Create a dedicated chain for WireGuard forwarding rules if it doesn't exist
nft list chain inet filter FORWARD &> /dev/null || nft add chain inet filter FORWARD
# Add a specific rule to allow this peer to access the database
# The rule is inserted at the top of the chain for quick matching
nft insert rule inet filter FORWARD iifname "$WG_INTERFACE" ip saddr "$PEER_IP" ip daddr "$DB_SERVER_IP" tcp dport "$DB_PORT" accept
echo "Granted access for $PEER_IP to $DB_SERVER_IP:$DB_PORT"
# To revoke access, the control plane would simply run:
# nft delete rule inet filter FORWARD iifname "$WG_INTERFACE" ip saddr "$PEER_IP" ip daddr "$DB_SERVER_IP" tcp dport "$DB_PORT" acceptThis level of granular, dynamic control is the essence of a ZTNA implementation. It moves security from static IP whitelists to an identity-aware, policy-driven model.
Best Practices and Ecosystem Tooling
As WireGuard’s role expands, so does the ecosystem around it. Implementing a robust solution requires attention to key management, monitoring, and choosing the right tools for the job.
Key Management is Paramount
In any cryptographic system, key management is the hardest part. Relying on long-lived, manually distributed static keys is a significant security risk. A proper ZTNA control plane must handle key generation and rotation automatically. Keys should be ephemeral, generated on-demand for each session and discarded afterward, minimizing the window of opportunity for an attacker if a key is compromised.
Monitoring and Observability
You can’t secure what you can’t see. Monitoring the health and status of a WireGuard-based network is critical. The wg show command provides a wealth of information, including the latest handshake time for each peer, which is a great indicator of connectivity. This output can be parsed and fed into modern observability stacks like Prometheus and Grafana, which are staples in Linux monitoring news.
This simple bash script can be run by a cron job or a systemd timer to expose WireGuard metrics for Prometheus’s node exporter textfile collector.
#!/bin/bash
# Path for Prometheus textfile collector
OUTPUT_FILE="/var/lib/node_exporter/textfile_collector/wireguard.prom"
TMP_FILE="$(mktemp)"
# Get a list of all WireGuard interfaces
INTERFACES=$(wg show | grep 'interface:' | awk '{print $2}')
# Header for the Prometheus metrics
echo '# HELP wireguard_peer_latest_handshake_seconds The timestamp of the latest handshake for a peer.' > "$TMP_FILE"
echo '# TYPE wireguard_peer_latest_handshake_seconds gauge' >> "$TMP_FILE"
echo '# HELP wireguard_peer_transfer_rx_bytes Bytes received from a peer.' >> "$TMP_FILE"
echo '# TYPE wireguard_peer_transfer_rx_bytes counter' >> "$TMP_FILE"
echo '# HELP wireguard_peer_transfer_tx_bytes Bytes transmitted to a peer.' >> "$TMP_FILE"
echo '# TYPE wireguard_peer_transfer_tx_bytes counter' >> "$TMP_FILE"
for iface in $INTERFACES; do
# Use 'wg showconf' for a more stable parsing format if available,
# but 'wg show' is universal. We'll parse 'wg show' output here.
wg show "$iface" | grep 'peer:' | while read -r line; do
pub_key=$(echo "$line" | awk '{print $2}')
# Get the block of data for this specific peer
peer_data=$(wg show "$iface" dump | grep "^${pub_key}")
latest_handshake=$(echo "$peer_data" | awk '{print $5}')
rx_bytes=$(echo "$peer_data" | awk '{print $6}')
tx_bytes=$(echo "$peer_data" | awk '{print $7}')
echo "wireguard_peer_latest_handshake_seconds{interface=\"$iface\", public_key=\"$pub_key\"} $latest_handshake" >> "$TMP_FILE"
echo "wireguard_peer_transfer_rx_bytes{interface=\"$iface\", public_key=\"$pub_key\"} $rx_bytes" >> "$TMP_FILE"
echo "wireguard_peer_transfer_tx_bytes{interface=\"$iface\", public_key=\"$pub_key\"} $tx_bytes" >> "$TMP_FILE"
done
done
# Atomically replace the old metrics file
mv "$TMP_FILE" "$OUTPUT_FILE"Conclusion: The Future is Built on WireGuard
WireGuard’s journey is a testament to the power of elegant design. Its inclusion in the Linux kernel was just the beginning. By providing a simple, secure, and high-performance primitive for encrypted communication, it has unlocked a new wave of innovation in network security. The shift towards using WireGuard as the data plane for sophisticated Zero-Trust platforms demonstrates its maturity and flexibility. For developers and administrators in the Linux ecosystem, from those managing Proxmox clusters to those orchestrating containers with Podman, WireGuard is no longer just a VPN replacement. It is a fundamental networking and security building block, poised to become the ubiquitous transport layer for secure access in the modern enterprise. As this trend continues, we can expect to see even tighter integration with the entire Linux stack, from systemd-networkd to advanced eBPF-based policy enforcement, further cementing its role as the backbone of next-generation secure networking.



