
Fortifying Your Network: A Deep Dive into Modern IPsec VPN Security on Linux
Introduction: The Renewed Imperative for Secure IPsec VPNs
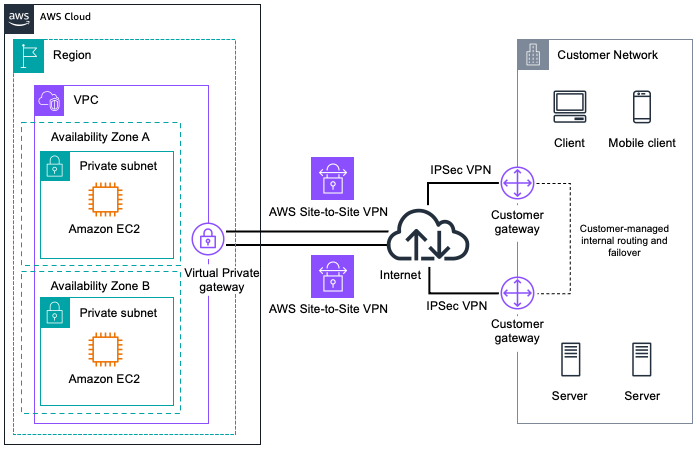
In an era where remote work has transitioned from a perk to a necessity, the Virtual Private Network (VPN) has become the bedrock of corporate network security. Among the most robust and widely adopted protocols for this purpose is Internet Protocol Security (IPsec). As a mature, standards-based framework, IPsec operates at the network layer, providing comprehensive security for all IP traffic without requiring application-specific modifications. However, its power and flexibility come with a corresponding complexity. Recent security advisories have highlighted that many legacy IPsec deployments are vulnerable due to outdated cryptographic algorithms and misconfigurations. This article serves as a comprehensive technical guide for Linux administrators and security professionals, offering the latest insights and practical steps to harden IPsec VPNs. We will explore core concepts, provide hands-on implementation examples using strongSwan on popular distributions like Debian and Red Hat, and delve into advanced hardening techniques, ensuring your network remains a secure fortress in the face of evolving threats. This is critical Linux security news for any organization relying on this foundational technology.
Deconstructing the IPsec Framework: Core Components and Modes
Before diving into configuration, it’s essential to understand the building blocks of IPsec. It isn’t a single protocol but a suite of protocols designed to provide security services for IP packets. This includes confidentiality, integrity, authentication, and anti-replay protection. Understanding these components is the first step toward a secure implementation.
Key Protocols: AH, ESP, and IKE
The IPsec suite primarily consists of three main protocols:
- Authentication Header (AH): Provides connectionless integrity, data origin authentication, and anti-replay protection for IP packets. It achieves this by adding a header to the IP packet. Importantly, AH does not provide confidentiality, meaning the data is not encrypted. It’s less common today, as ESP can provide both authentication and encryption.
- Encapsulating Security Payload (ESP): This is the workhorse of modern IPsec. ESP provides confidentiality (encryption), data origin authentication, connectionless integrity, and anti-replay protection. It can be used to encrypt the entire original IP packet (Tunnel Mode) or just the payload (Transport Mode).
- Internet Key Exchange (IKE): IPsec requires cryptographic keys and security parameters to be established between two endpoints. IKE (currently at version 2, or IKEv2) is the protocol used to negotiate these Security Associations (SAs) automatically. It handles the authentication of peers and the generation of shared keys, typically using the Diffie-Hellman (DH) key exchange algorithm. IKEv2 is a significant improvement over the older IKEv1, offering better performance, reliability, and security.
Tunnel Mode vs. Transport Mode
IPsec can operate in two distinct modes, which dictate how the original IP packet is protected:
- Transport Mode: In this mode, only the payload of the IP packet is encrypted and/or authenticated. The original IP header is left intact. This is typically used for end-to-end communication between two hosts.
- Tunnel Mode: In this mode, the entire original IP packet (including its header) is encapsulated within a new IP packet. This new packet has its own header. Tunnel mode is the standard for creating site-to-site and remote-access VPNs, as it effectively hides the internal network topology from the public internet.
For most Linux VPN news and server-to-server setups, you will almost always use ESP in Tunnel Mode with IKEv2 for key negotiation.
# /etc/ipsec.conf - A Basic Structural Example
# Global configuration settings
config setup
# strictcrlpolicy=yes # Example of a global setting
# uniqueids = no
# "conn" sections define connections (tunnels)
# The %default section sets defaults for all connections
conn %default
ikelifetime=60m
keylife=20m
rekeymargin=3m
keyingtries=1
keyexchange=ikev2
authby=secret # Using Pre-Shared Keys
# Definition for a specific site-to-site connection
conn site-to-site-vpn
left=%defaultroute
leftsubnet=192.168.1.0/24
right=203.0.113.50
rightsubnet=192.168.2.0/24
auto=start # Automatically start the connection on service startPractical IPsec Implementation with strongSwan on Linux
strongSwan is a popular, modern, and feature-rich open-source IPsec implementation available on most Linux distributions. Whether you’re following Ubuntu news, Fedora news, or managing an enterprise server with Red Hat news, the process is similar. Let’s walk through setting up a basic site-to-site VPN.
Installation and Initial Setup
First, install the necessary packages using your distribution’s package manager. This is a common task in Linux administration news.

# For Debian/Ubuntu systems (apt news)
sudo apt update
sudo apt install strongswan -y
# For RHEL/CentOS/Fedora systems (dnf news)
sudo dnf install strongswan -yNext, enable IP forwarding in the kernel. This allows the server to route packets between its interfaces, which is essential for the VPN tunnel. Edit /etc/sysctl.conf and add or uncomment the following lines:
net.ipv4.ip_forward = 1
net.ipv4.conf.all.accept_redirects = 0
net.ipv4.conf.all.send_redirects = 0
Apply the changes without rebooting by running sudo sysctl -p.
Configuring the Connection
Configuration is handled primarily in two files: /etc/ipsec.conf for connection parameters and /etc/ipsec.secrets for authentication credentials like Pre-Shared Keys (PSKs).
Here is a complete example for a site-to-site tunnel between two offices. Let’s call them “HQ” and “Branch”.
On the HQ Server (Public IP: 198.51.100.10, Local Subnet: 10.10.1.0/24):
# /etc/ipsec.conf on HQ Server
config setup
charondebug="ike 2, knl 2, cfg 2"
conn %default
# Modern defaults for Phase 1 (IKE SA)
ike=aes256gcm16-sha2_256-modp2048!
# Modern defaults for Phase 2 (IPsec SA)
esp=aes256gcm16-sha2_256!
keyexchange=ikev2
ikelifetime=8h
lifetime=1h
dpdaction=restart
dpddelay=30s
dpdtimeout=120s
authby=secret
auto=start
type=tunnel
conn to-branch
left=198.51.100.10
leftsubnet=10.10.1.0/24
right=203.0.113.50
rightsubnet=10.20.1.0/24On the Branch Server (Public IP: 203.0.113.50, Local Subnet: 10.20.1.0/24): The configuration is nearly identical, just with the left and right parameters swapped.
Configuring the Pre-Shared Key (PSK)
The PSK must be identical on both servers. This file is highly sensitive and should have strict permissions (600). A strong, randomly generated key is crucial for security.
# /etc/ipsec.secrets on BOTH servers
# Format: {left-id} {right-id} : PSK "YourSuperLongAndRandomSecretKeyGoesHere"
198.51.100.10 203.0.113.50 : PSK "a9$Vb#zL8*k!pQ@wE7fG2^hN"After configuring, restart the strongSwan service (sudo systemctl restart strongswan) and check the status with sudo ipsec statusall. You should see the tunnel established. This process is a cornerstone of Linux server news for network administrators.
Advanced IPsec Hardening and Modern Cryptography
A default configuration is a starting point, not a destination. The real work in securing IPsec lies in hardening the cryptographic parameters. The latest Linux security news emphasizes moving away from legacy algorithms.
Choosing Strong Cipher Suites
The security of your VPN tunnel is only as strong as the ciphers you use. Many older tutorials and default configurations still include weak or broken algorithms. Here’s what to avoid and what to use:
- Avoid: MD5, SHA1 (for hashing/integrity), 3DES, AES-CBC (vulnerable to padding oracle attacks if not implemented perfectly), and Diffie-Hellman groups below 2048 bits (e.g., modp1024, modp1536).
- Recommended:
- Encryption: AES-GCM (e.g.,
aes256gcm16). GCM mode provides both encryption and authentication in a single, highly efficient operation. - Integrity/Hashing: SHA-2 family (
sha256,sha384,sha512). - Diffie-Hellman Group: Use strong groups for Perfect Forward Secrecy (PFS).
modp2048(DH Group 14) is a good baseline. For higher security, use Elliptic Curve groups likeecp384(Group 20) ormodp3072(Group 15).
- Encryption: AES-GCM (e.g.,
The ike and esp lines in the ipsec.conf example above reflect a modern, secure cipher suite. The exclamation mark (!) at the end tells strongSwan that the proposal is mandatory, preventing negotiation down to weaker algorithms.
Enforcing Perfect Forward Secrecy (PFS)
PFS ensures that if a long-term key (like your PSK) is ever compromised, an attacker cannot decrypt past captured traffic. It achieves this by generating a new, ephemeral session key for each IPsec SA rekeying event using a new Diffie-Hellman exchange. In strongSwan, you enable PFS by specifying a DH group in your esp proposal. Our recommended cipher suite (esp=aes256gcm16-sha2_256!) does not explicitly list a DH group, so strongSwan will default to using the same group as the IKE SA. For explicit control, you could use esp=aes256gcm16-sha2_256-modp2048!.
Monitoring and Auditing Your VPN
Continuous monitoring is key. Use journalctl to inspect logs from the strongSwan daemon (charon).
# View live logs for strongSwan
sudo journalctl -u strongswan -f
# Check the status of all connections and SAs
sudo ipsec statusallFor external auditing, you can use tools like ike-scan to probe your VPN gateway from the outside and see which cryptographic proposals it offers. This can help you identify weak ciphers you might be inadvertently advertising.

Best Practices, Firewalling, and Common Pitfalls
Securing IPsec extends beyond the daemon’s configuration. System-level settings and operational practices are equally important. This is a recurring theme in Linux networking news.
Firewall Configuration with nftables
Your firewall must permit IPsec traffic. This includes UDP ports 500 (for IKE) and 4500 (for NAT Traversal), as well as the ESP protocol (protocol number 50) and AH protocol (protocol number 51), if used. Here’s a basic ruleset for nftables, a topic of frequent nftables news.
#!/usr/sbin/nft -f
flush ruleset
table inet filter {
chain input {
type filter hook input priority 0; policy drop;
# Allow established and related traffic
ct state established,related accept
# Allow loopback
iifname "lo" accept
# Allow ICMP
ip protocol icmp accept
ip6 nexthdr ipv6-icmp accept
# Allow SSH
tcp dport 22 accept
# --- IPsec Rules ---
# Allow IKE and NAT-T
udp dport { 500, 4500 } accept
# Allow ESP protocol
ip protocol esp accept
}
chain forward {
type filter hook forward priority 0; policy drop;
# --- IPsec Forwarding Rules ---
# Allow traffic from our local LAN to the remote VPN subnet
ip saddr 10.10.1.0/24 ip daddr 10.20.1.0/24 accept
# Allow return traffic from the remote VPN subnet to our LAN
ip saddr 10.20.1.0/24 ip daddr 10.10.1.0/24 accept
}
chain output {
type filter hook output priority 0; policy accept;
}
}Common Pitfalls to Avoid
- Weak Pre-Shared Keys: A PSK is often the weakest link. Avoid dictionary words or simple phrases. Use a password manager to generate a long, random string of at least 20 characters. For higher security, migrate to certificate-based authentication.
- Overly Permissive Traffic Selectors: Be specific with your
leftsubnetandrightsubnetdefinitions. Using0.0.0.0/0(any) can inadvertently route all traffic over the VPN and create security holes. - Not Enabling DPD: Dead Peer Detection (DPD) is crucial for cleaning up stale connections when a peer goes offline ungracefully. Without it, you can be left with a non-functional tunnel until it times out naturally.
- Ignoring Logs: The strongSwan logs are verbose but invaluable for troubleshooting and security monitoring. Regularly check for authentication failures or unexpected connection drops. Keeping up with Linux logs news and tools like
journalctlis essential.
Conclusion: The Path to a Resilient IPsec Deployment
IPsec remains a powerful and relevant technology for securing network communications, especially for the Linux servers that form the backbone of the internet. However, the “set it and forget it” mentality is a significant risk. As this deep dive has shown, a secure IPsec deployment requires a deliberate and modern approach. The key takeaways are clear: always use IKEv2, enforce strong, modern cryptographic suites like AES-GCM and SHA-2, enable Perfect Forward Secrecy, and use robust authentication methods. Regularly audit your configurations and stay informed about the latest Linux VPN news and security guidance. By treating your IPsec VPN as a critical, dynamic piece of your security infrastructure—much like you would a web server or database—you can ensure it provides the robust protection your organization needs in a constantly evolving threat landscape. The next step for any serious deployment should be to move beyond PSKs and implement a Public Key Infrastructure (PKI) for certificate-based authentication, offering superior scalability and security.



