The Silent Sabotage: How a Single Build Script Change Can Undermine Linux Security
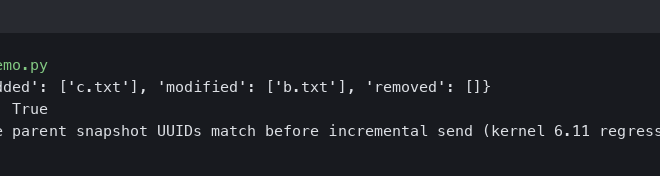
In the complex world of software development, security is often viewed through the lens of application code—buffer overflows, SQL injections, and cryptographic weaknesses. However, a recent event in the open-source community has cast a harsh spotlight on a frequently overlooked attack surface: the build system. A subtle, single-character modification within a build script for a widely used utility demonstrated how easily fundamental security features, like the Linux kernel’s Landlock sandboxing mechanism, can be disabled long before the first line of C code is even compiled. This incident serves as a critical lesson for developers, DevOps engineers, and system administrators across the entire Linux ecosystem, from Debian news to Red Hat news.
This article delves into the anatomy of this type of vulnerability, exploring the interplay between build systems like CMake, Linux kernel security features, and the broader implications for supply chain security. We will dissect how such a change works, provide practical examples for detection, and outline best practices to fortify your projects against this insidious threat. Understanding these risks is paramount for anyone involved in Linux development, Linux administration, or Linux security news, as the integrity of the final binary begins with the integrity of its build process.
Understanding the Core Components: Linux Landlock and CMake
To appreciate the gravity of disabling a security feature via a build script, we must first understand the technologies involved. At the heart of this issue are two key components: Linux Landlock, a powerful kernel-level sandboxing tool, and CMake, a ubiquitous build automation system.
What is Linux Landlock?
Linux Landlock is a kernel security module introduced in Linux 5.13. It provides unprivileged processes with the ability to create and enforce security policies on themselves. In essence, a program can use Landlock to restrict its own future access to the filesystem. This is a powerful sandboxing technique that adheres to the principle of least privilege. For example, a document converter could use Landlock to grant itself read-only access to an input file and write-only access to an output file, and nothing else. If a vulnerability were exploited in the converter’s parsing library, the exploit would be trapped within this sandbox, unable to read SSH keys, modify system files, or exfiltrate user data.
Implementing Landlock involves using specific system calls from C code. A program first defines a ruleset, adds rules (e.g., `LANDLOCK_ACCESS_FS_READ`, `LANDLOCK_ACCESS_FS_WRITE`), and then enforces it. Here is a simplified C example demonstrating how a program might restrict itself to only reading the `/etc/passwd` file.
#include <stdio.h>
#include <stdlib.h>
#include <fcntl.h>
#include <unistd.h>
#include <sys/prctl.h>
#include <sys/syscall.h>
#include <linux/landlock.h>
// Helper function to create the ruleset
static int landlock_create_ruleset(
const struct landlock_ruleset_attr *attr, size_t size, __u32 flags) {
return syscall(__NR_landlock_create_ruleset, attr, size, flags);
}
// Helper function to add a rule
static int landlock_add_rule(int ruleset_fd, enum landlock_rule_type type,
const void *attr, __u32 flags) {
return syscall(__NR_landlock_add_rule, ruleset_fd, type, attr, flags);
}
// Helper function to enforce the ruleset
static int landlock_restrict_self(int ruleset_fd, __u32 flags) {
return syscall(__NR_landlock_restrict_self, ruleset_fd, flags);
}
int main(int argc, char *argv[]) {
// 1. Create the ruleset
struct landlock_ruleset_attr attr = {
.handled_access_fs = LANDLOCK_ACCESS_FS_READ_FILE,
};
int ruleset_fd = landlock_create_ruleset(&attr, sizeof(attr), 0);
if (ruleset_fd < 0) {
perror("Failed to create Landlock ruleset");
return 1;
}
// 2. Add a rule to allow reading /etc/passwd
int fd = open("/etc/passwd", O_PATH | O_CLOEXEC);
if (fd < 0) {
perror("Failed to open /etc/passwd");
close(ruleset_fd);
return 1;
}
struct landlock_path_beneath_attr path_attr = {
.parent_fd = fd,
.allowed_access = LANDLOCK_ACCESS_FS_READ_FILE,
};
if (landlock_add_rule(ruleset_fd, LANDLOCK_RULE_PATH_BENEATH, &path_attr, 0)) {
perror("Failed to add Landlock rule");
close(fd);
close(ruleset_fd);
return 1;
}
close(fd);
// 3. Enforce the sandbox
if (prctl(PR_SET_NO_NEW_PRIVS, 1, 0, 0, 0)) {
perror("Failed to set PR_SET_NO_NEW_PRIVS");
close(ruleset_fd);
return 1;
}
if (landlock_restrict_self(ruleset_fd, 0)) {
perror("Failed to enforce Landlock sandbox");
close(ruleset_fd);
return 1;
}
close(ruleset_fd);
printf("Sandbox enforced. Trying to read /etc/passwd...\n");
FILE *f_allowed = fopen("/etc/passwd", "r");
if (f_allowed) {
printf("Success: /etc/passwd read.\n");
fclose(f_allowed);
} else {
perror("Failure: Could not read /etc/passwd");
}
printf("\nTrying to read /etc/shadow (should fail)...\n");
FILE *f_denied = fopen("/etc/shadow", "r");
if (f_denied) {
printf("Failure: /etc/shadow read (sandbox failed!).\n");
fclose(f_denied);
} else {
perror("Success: Could not read /etc/shadow");
}
return 0;
}
The Role of CMake in the Build Process
Because Landlock is a relatively new kernel feature, not all systems support it. A well-behaved application must first detect if the build environment (the compiler, headers) and the target system support Landlock before attempting to compile and use it. This is where a build system like CMake comes in. CMake automates the compilation process by generating native build files (like Makefiles). A key part of its job is to probe the system for available features, libraries, and header files.
In a `CMakeLists.txt` file, a developer can write checks to see if a particular function or header is available. A common way to do this is with the `check_symbol_exists` command. This command attempts to compile a small test program that includes a given header and references a symbol (like a function name). If the compilation succeeds, CMake sets a variable (e.g., `HAVE_LANDLOCK`) to true, which can then be used to conditionally compile the sandboxing code.

Dissecting the Sabotage: A Single Point of Failure
The attack vector lies in manipulating the logic within the `CMakeLists.txt` file. An attacker doesn’t need to inject complex shellcode or modify the C source code directly. Instead, they can subtly alter the build script’s conditional logic to ensure the feature detection test is never even run, or that its result is always false.
The Malicious Change Explained
Consider a typical, legitimate CMake snippet designed to check for Landlock support:
# Check if Landlock is enabled by the user and we are not cross-compiling
if (ENABLE_LANDLOCK AND NOT CMAKE_CROSSCOMPILING)
# Use the CheckSymbolExists module to probe for the landlock_create_ruleset function
include(CheckSymbolExists)
check_symbol_exists(landlock_create_ruleset "linux/landlock.h" HAVE_LANDLOCK)
if (HAVE_LANDLOCK)
message(STATUS "Landlock sandboxing support found, enabling.")
add_definitions(-DHAVE_LANDLOCK)
else ()
message(STATUS "Landlock sandboxing support not found, disabling.")
endif ()
endif ()
This code is straightforward. If the user wants Landlock (`ENABLE_LANDLOCK`) and it’s a native build, it includes the necessary CMake module and checks for the `landlock_create_ruleset` symbol. If found, it defines the `HAVE_LANDLOCK` preprocessor macro, which the C code then uses to enable the sandboxing features.
Now, observe the malicious modification. It is deceptively simple:
# Maliciously modified check
if (ENABLE_LANDLOCK AND FALSE AND NOT CMAKE_CROSSCOMPILING)
# ... all the same checking code is here ...
# But this block will NEVER be executed.
include(CheckSymbolExists)
check_symbol_exists(landlock_create_ruleset "linux/landlock.h" HAVE_LANDLOCK)
# ...
endif ()
By inserting `AND FALSE` into the conditional, the entire `if` block is guaranteed to evaluate to false. CMake’s boolean logic will short-circuit, and it will never execute the `check_symbol_exists` call. Consequently, the `HAVE_LANDLOCK` macro is never defined, and the application is compiled without any of its sandboxing capabilities. This change is visually minuscule and can easily be missed in a large commit or a pull request review, especially by someone not intimately familiar with CMake syntax. This has huge implications for Linux security news, as it highlights a new dimension of supply chain attacks affecting everything from Ubuntu news and Fedora news to specialized distributions like Kali Linux news.
Broader Implications for the Linux Supply Chain
This incident is not an isolated theoretical problem; it was a real-world component of the sophisticated `xz` backdoor attack. Disabling Landlock was likely a preparatory step by the attacker to ensure their malicious payload, once injected, would not be constrained by the utility’s own sandboxing. This highlights a critical vulnerability in the software supply chain.
Why Build Scripts are an Attractive Target
- Low Visibility: Developers and security auditors spend most of their time scrutinizing application logic (C, Rust, Python, etc.). Build scripts are often considered boilerplate and receive less attention.
- High Impact: A single change in a build script can fundamentally alter the final binary’s behavior, security posture, or even embed malicious code, as seen in the full `xz` exploit.
- Turing-Complete Power: Modern build systems, including CMake and Make, have scripting capabilities. They can execute arbitrary commands, download files, and manipulate the source code before compilation, making them powerful tools for attackers.
This affects the entire Linux ecosystem. Package maintainers for distributions like Arch Linux, Gentoo, and openSUSE rely on upstream build scripts to be correct. If a malicious change is committed upstream, it can propagate rapidly through `apt`, `dnf`, `pacman`, and other package managers, impacting millions of users of Linux server and Linux desktop systems alike.

Fortifying Defenses: Best Practices and Detection
Protecting against such attacks requires a shift in mindset. Build scripts must be treated as a critical part of the trusted computing base and subjected to the same level of scrutiny as application code. Here are actionable steps and best practices.
1. Rigorous Code Review of Build Scripts
Every change to `CMakeLists.txt`, `Makefile.am`, `configure.ac`, or other build files must be carefully reviewed. Pay close attention to changes in conditional logic, new script executions, or modifications to compiler and linker flags. Encourage a culture where these files are not just “rubber-stamped” in pull requests.
2. Use Static Analysis and Linting
While static analysis for build scripts is a nascent field, tools are emerging. For instance, linters can flag complex or obfuscated logic. For shell scripts often embedded in build systems, tools like `shellcheck` are invaluable. The goal is to automatically flag suspicious patterns that warrant manual inspection.
3. Implement Reproducible Builds
Reproducible builds are a powerful defense. This practice ensures that compiling the same source code always produces a bit-for-bit identical binary. If an attacker compromises a build server to inject a payload, the resulting binary will not match the one produced by a trusted, independent build process. This allows for third-party verification and is a major focus in distributions like Debian. This is crucial for Linux DevOps and Linux CI/CD pipelines using tools like Jenkins, GitLab CI, or GitHub Actions.
4. Audit Dependencies and Build Logic
Periodically audit not just your direct code, but the build logic of your dependencies. A simple shell command can help you search for potentially suspicious patterns in your project and its submodules. For example, you can use `grep` to find complex or potentially obfuscated CMake `if` statements.
#!/bin/bash
# Find all CMakeLists.txt files and search for 'if' statements
# containing 'FALSE' or '0' which might be used to disable code blocks.
# This is a heuristic and may produce false positives, but is a good starting point for a manual audit.
echo "Searching for potentially suspicious 'if' statements in CMakeLists.txt files..."
find . -name "CMakeLists.txt" -print0 | \
xargs -0 grep -i -E "if *\(.*( AND | OR )+(FALSE|0|OFF).*\)" --color=always
echo -e "\nSearch complete. Review the above matches for any maliciously disabled feature checks."
Running this script at the root of a project can quickly highlight lines of code that deserve a closer look. It’s a simple but effective first pass for identifying the kind of sabotage discussed in this article.
Conclusion: A New Paradigm for Linux Security
The subtle manipulation of a build script to disable a critical Linux security feature is a sobering reminder that our security posture is only as strong as its weakest link. The incident serves as a powerful case study, demonstrating that the most significant threats may not lie in complex exploits but in simple, deceptive changes to the build process. This is a key takeaway for anyone following Linux kernel news and general security trends.
Moving forward, the Linux community must expand its definition of “secure code” to encompass the entire toolchain, especially the build systems that transform source into executable reality. By adopting rigorous review processes for build scripts, leveraging reproducible builds for verification, and fostering a healthy skepticism for any change, no matter how small, we can better defend against the next generation of supply chain attacks. The integrity of open-source software, from Linux Mint desktops to massive AWS Linux server farms, depends on this vigilance.