
Critical Linux Bluetooth Flaw: A Deep Dive into Kernel Security and Mitigation
In the world of operating systems, the Linux kernel stands as a titan, powering everything from massive cloud servers and supercomputers to the majority of smartphones and countless Internet of Things (IoT) devices. Its open-source nature fosters rapid innovation and a global community of developers. However, this ubiquity also means that a single, deep-seated vulnerability can have a colossal impact. Recently, a significant security flaw was disclosed in the Linux kernel’s Bluetooth stack, highlighting the critical importance of timely updates and a robust security posture. This remote code execution (RCE) vulnerability has existed in the kernel for nearly a decade, putting a vast number of systems at risk.
This article provides a comprehensive technical analysis of this critical vulnerability. We will dissect the underlying components of the Linux Bluetooth stack, explain the nature of the flaw, and provide actionable steps for system administrators, developers, and end-users to assess their exposure and secure their systems. From immediate patching to long-term hardening strategies, we’ll cover the essential knowledge needed to navigate this latest challenge in Linux security news.
Understanding the Linux Bluetooth Stack and the Vulnerability
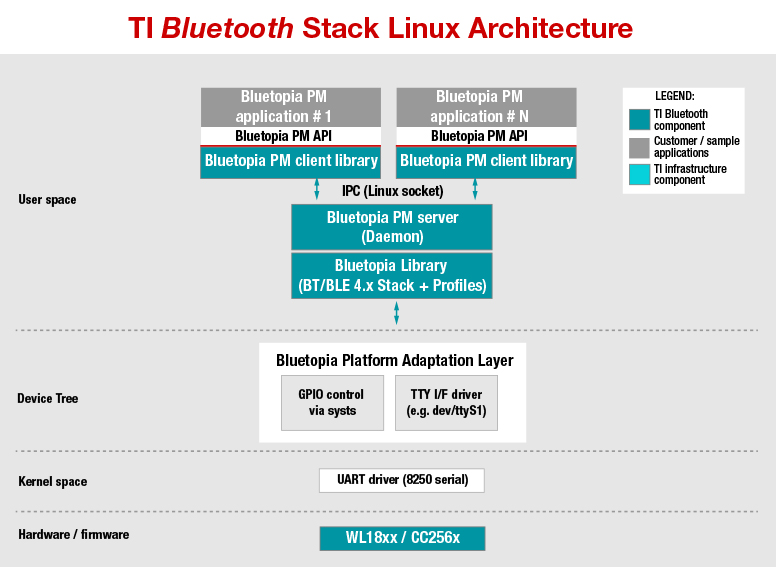
To grasp the severity of this issue, it’s essential to first understand the architecture of Bluetooth on Linux. The official implementation is known as BlueZ, a complex protocol stack that lives directly within the Linux kernel. This deep integration provides high performance and efficiency but also means that a flaw in BlueZ can directly compromise the entire kernel, the most privileged part of the operating system.
A Primer on BlueZ and the L2CAP Layer
BlueZ is responsible for managing Bluetooth hardware and implementing the various protocols that allow devices to communicate. One of the fundamental layers in this stack is the Logical Link Control and Adaptation Protocol (L2CAP). L2CAP acts as a protocol multiplexer, taking data from higher-level applications and protocols and passing it over the baseband connection. It is analogous to TCP or UDP in the internet protocol suite, providing connection-oriented and connectionless data services.
The recently discovered vulnerability is a heap-based type confusion flaw within the L2CAP implementation. In simple terms, an unauthenticated, remote attacker within Bluetooth range can send a specially crafted L2CAP packet to a vulnerable device. This malicious packet tricks the kernel into misinterpreting a block of memory, confusing one type of data structure for another. This confusion can be exploited to overwrite adjacent memory, ultimately leading to kernel panic (a system crash) or, more dangerously, arbitrary code execution with kernel-level privileges.
Identifying Potentially Vulnerable Systems
The vulnerability affects Linux kernel versions from 3.16 up to the patched versions released in late 2023 and early 2024. The first step for any administrator or user is to check their current kernel version. You can do this easily from the terminal.
# Check the running Linux kernel version
uname -rIf the output shows a version between 3.16 and the latest patched releases (e.g., before 6.6.8, 6.5.13, 6.1.68, etc., depending on your long-term support branch), your system is likely vulnerable if it has Bluetooth enabled. This is critical Linux kernel news for anyone managing a fleet of devices, from Debian news and Ubuntu news for servers and desktops to Linux IoT news for embedded systems.
Assessing Your Exposure and Immediate Mitigation
Given the widespread use of Linux, the attack surface for this vulnerability is enormous. It affects a vast range of distributions and devices, including popular desktop environments and server deployments.
Applying Security Patches Across Major Distributions
The open-source community and distribution maintainers have acted swiftly to patch the vulnerability. The most critical action is to update your system’s kernel to a patched version. Below are the commands for updating on several major Linux families. Always ensure you reboot your system after a kernel update for the changes to take effect.
For Debian, Ubuntu, Linux Mint, and derivatives (apt):
# Update package lists
sudo apt update
# Upgrade all packages, including the kernel
sudo apt full-upgrade
# Reboot the system to apply the new kernel
sudo rebootFor Fedora, CentOS, Rocky Linux, AlmaLinux, and RHEL derivatives (dnf/yum):
# Update all packages with dnf
sudo dnf update -y
# Reboot the system
sudo rebootFor Arch Linux, Manjaro, and derivatives (pacman):
# Synchronize package databases and upgrade the system
sudo pacman -Syu
# Reboot the system
sudo rebootTemporary Hardening: Disabling Bluetooth
If you cannot patch your system immediately or if Bluetooth functionality is not required, the most effective mitigation is to disable it entirely. This completely removes the attack surface. You can disable the Bluetooth service using systemd, the standard init system for most modern Linux distributions.
# Stop the Bluetooth service immediately
sudo systemctl stop bluetooth.service
# Prevent the Bluetooth service from starting on boot
sudo systemctl disable bluetooth.service
# (Optional) Check the status to confirm it's inactive
sudo systemctl status bluetooth.serviceThis is a crucial step in Linux server news, as many servers may have Bluetooth hardware that is unused but still enabled by default, posing an unnecessary risk.
Deeper Dive: Interacting with and Monitoring Bluetooth on Linux
Beyond patching, understanding how to manage and monitor Bluetooth devices from the command line is a valuable skill for both Linux administration and security analysis. These tools can help you verify your system’s state and investigate suspicious activity.
Command-Line Management with bluetoothctl
The bluetoothctl utility provides a powerful interactive shell for pairing, connecting, and managing Bluetooth devices. It’s an excellent tool for everyday use and for scripting Bluetooth interactions.
Here is an example of an interactive session to scan for and trust a device:

# Launch the interactive bluetoothctl shell
bluetoothctl
# Inside the shell, start a scan for new devices
[bluetooth]# scan on
Discovery started
[CHG] Controller AA:BB:CC:DD:EE:FF Discovering: yes
[NEW] Device 12:34:56:78:9A:BC My Bluetooth Keyboard
# Stop scanning once the device is found
[bluetooth]# scan off
# Pair with the device using its MAC address
[bluetooth]# pair 12:34:56:78:9A:BC
# Trust the device for future automatic connections
[bluetooth]# trust 12:34:56:78:9A:BC
# Exit the shell
[bluetooth]# exitMonitoring Low-Level Traffic with btmon
For more advanced diagnostics and security analysis, btmon is an indispensable tool. It captures and displays low-level Host Controller Interface (HCI) events and data in real-time. This allows you to see the raw communication between your system’s Bluetooth controller and other devices, which is invaluable for debugging or identifying anomalous packets.
Running btmon as root will immediately start dumping all Bluetooth management and monitoring events to your terminal. This can be very verbose but is excellent for seeing exactly what the stack is doing.
# Run btmon with root privileges to monitor all HCI traffic
sudo btmonMonitoring this output during connection attempts can reveal issues or provide insight into the types of L2CAP connections being established, which is directly relevant to the recent vulnerability. This is a key practice for anyone following Linux forensics or incident response news.
Best Practices for a Secure Linux Environment
Responding to this specific vulnerability is important, but it also serves as a reminder of the need for a comprehensive, long-term security strategy. A hardened system is more resilient to both known and future unknown threats.
The Principle of Least Functionality
One of the core tenets of security is to minimize the attack surface. This means disabling any hardware, services, or software that are not absolutely necessary for the system’s function. As we demonstrated with disabling the Bluetooth service, this principle is highly effective. Regularly audit your systems, whether they are Linux desktop machines running GNOME or KDE Plasma, or headless servers. If a service like Bluetooth, WiFi, or even a specific network port isn’t needed, turn it off. This philosophy is central to robust Linux firewall and Linux SELinux policies.

Automated Patch Management and Staying Informed
Manually updating a single machine is simple, but managing a fleet requires automation. Tools like unattended-upgrades on Debian/Ubuntu systems or custom Ansible playbooks can ensure that critical security patches are applied automatically and promptly. Furthermore, staying informed is key. Subscribe to the security advisory mailing lists for your specific distribution (e.g., Ubuntu Security Notices, Debian Security Announce, Red Hat Security Advisories). This ensures you are among the first to know when critical Linux security news breaks.
Leveraging Linux Security Modules (LSM)
Frameworks like SELinux (used in Fedora, RHEL) and AppArmor (used in Debian, Ubuntu, openSUSE) are powerful tools for mandatory access control. While they might not have prevented the initial exploitation of this specific kernel bug, a well-configured LSM policy can significantly contain the post-exploitation impact. By strictly defining what a compromised process is allowed to do—which files it can access, which network connections it can make, which other processes it can interact with—LSMs can prevent an attacker from moving laterally and achieving their ultimate objectives. This adds a critical layer of defense-in-depth to your Linux server or desktop.
Conclusion: A Call for Vigilance
The discovery of a decade-old remote code execution vulnerability in the Linux kernel’s Bluetooth stack is a sobering event. It underscores the fact that even mature, widely-used code can harbor critical flaws. The impact spans nearly the entire Linux ecosystem, from Android phones and IoT devices to powerful servers and everyday desktops running distributions like Fedora, Ubuntu, and Arch Linux.
The key takeaways for every Linux user and administrator are clear. First, immediate action is required: check your kernel version and apply the latest security patches provided by your distribution. Second, if Bluetooth is not a required function for your device, disable it to eliminate the risk entirely. Finally, this incident should serve as a catalyst to adopt a more proactive and layered security posture. By embracing principles like least functionality, automated patch management, and mandatory access control systems, you can build a more resilient environment capable of withstanding not just this threat, but the next one as well. The strength of the Linux community lies in its ability to identify, patch, and deploy fixes rapidly. Now is the time to leverage that strength by updating your systems.



