Rust on Linux: Crafting the Next Generation of Secure and Performant System Tools
The Linux ecosystem, long the domain of C and C++, is witnessing a significant shift. A new language is rapidly gaining traction, promising to revolutionize how we build everything from command-line utilities to core kernel components. That language is Rust. In recent Rust Linux news, we’ve seen a surge in its adoption for creating robust, high-performance applications that run on everything from massive cloud servers to tiny embedded devices. This isn’t just a fleeting trend; it’s a fundamental change driven by Rust’s unique ability to offer memory safety without sacrificing the low-level control and performance that system programming demands.
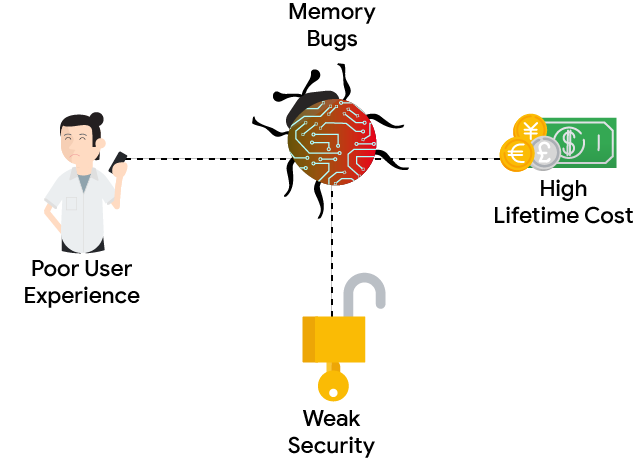
For decades, developers working on Linux have accepted a trade-off: the raw power of C for the price of manual memory management and the constant threat of bugs like buffer overflows and data races. Rust eliminates this trade-off. Its compiler acts as a vigilant partner, enforcing strict rules at compile time to prevent entire classes of common errors. This article dives deep into why Rust is becoming the go-to language for modern Linux development, exploring its core concepts with practical code examples and showcasing its power in building tools for distributions like Ubuntu, Fedora, and Arch Linux.
The Rust Advantage: Safety, Performance, and Concurrency on Linux
Rust’s appeal in the world of Linux programming news stems from a set of core principles that directly address the most persistent challenges in systems development. It provides high-level abstractions without performance penalties, making it both powerful and ergonomic.
Memory Safety by Default: The Ownership Model
The cornerstone of Rust’s safety guarantees is its ownership system. Every value in Rust has a single owner. When the owner goes out of scope, the value is automatically dropped, and its memory is freed. This simple rule, enforced by the compiler, completely eliminates manual memory management and prevents issues like double-free errors and dangling pointers, which are common sources of vulnerabilities discussed in Linux security news.
Let’s illustrate this with a struct representing a system process. The ownership rules ensure that the resource it manages is handled correctly.
// A simple struct to represent a managed system process
struct MonitoredProcess {
pid: u32,
name: String,
}
impl MonitoredProcess {
fn new(pid: u32, name: &str) -> Self {
println!("Process '{}' (PID: {}) is now being monitored.", name, pid);
Self {
pid,
name: String::from(name),
}
}
}
// The Drop trait is like a destructor. Rust calls this automatically
// when the variable goes out of scope.
impl Drop for MonitoredProcess {
fn drop(&mut self) {
// This is where cleanup logic, like closing a file handle
// or sending a termination signal, would go.
println!(
"Stopping monitoring for process '{}' (PID: {}). Resource cleaned up.",
self.name, self.pid
);
}
}
fn main() {
// p1 owns the MonitoredProcess instance.
let p1 = MonitoredProcess::new(1001, "database_worker");
// This line would cause a compile-time error!
// Ownership of p1's data cannot be moved while it's still in use.
// let p2 = p1;
// println!("Trying to access p1's PID: {}", p1.pid); // Error: use of moved value: `p1`
// The scope of main ends here. p1 is "dropped", and its `drop` method
// is called automatically, ensuring cleanup.
}In this example, the Drop trait ensures that when a MonitoredProcess variable is no longer needed, its cleanup logic runs automatically. The compiler’s strict ownership rules prevent you from accidentally creating two variables that think they own and need to clean up the same resource, a classic source of bugs in C/C++.
Fearless Concurrency
Modern Linux servers, from those running on-prem with Red Hat news to cloud instances in AWS Linux news, are built on multi-core processors. Writing correct concurrent code is notoriously difficult. Rust’s ownership model extends to threading, preventing data races at compile time. If your code compiles, you can be confident that it’s free of this insidious type of bug. This “fearless concurrency” allows developers to write multi-threaded applications for tasks like high-performance web servers or data processing pipelines with much greater confidence.

Building Modern Command-Line Interfaces (CLIs) for Linux
One of the most common tasks for a Linux developer or administrator is creating command-line tools. Rust excels here, combining performance with a rich ecosystem of libraries (called “crates”) that simplify development. This is highly relevant for anyone following Linux administration news or Linux DevOps news.
Structuring a CLI Application with `clap`
The clap crate is the gold standard for parsing command-line arguments in Rust. It allows you to define your CLI’s structure declaratively, and it automatically handles argument parsing, validation, and generating help messages.
Let’s build a simple log file search tool, a mini-grep, that demonstrates how to structure a real-world application. This tool will be useful on any system, from a Debian news server to a Pop!_OS news desktop.
use clap::Parser;
use std::fs::File;
use std::io::{self, BufRead, BufReader};
use std::path::PathBuf;
/// A simple tool to search for a pattern in a file, inspired by grep.
#[derive(Parser, Debug)]
#[command(author, version, about, long_about = None)]
struct CliArgs {
/// The pattern to search for
#[arg(short, long)]
pattern: String,
/// The path to the file to search in
#[arg(short, long)]
path: PathBuf,
/// Optional: Perform a case-insensitive search
#[arg(short = 'i', long, default_value_t = false)]
case_insensitive: bool,
}
fn main() -> io::Result<()> {
let args = CliArgs::parse();
// Open the file specified by the user
let file = File::open(&args.path)?;
let reader = BufReader::new(file);
let pattern_to_search = if args.case_insensitive {
args.pattern.to_lowercase()
} else {
args.pattern
};
println!(
"Searching for '{}' in '{}'...",
&pattern_to_search,
args.path.display()
);
// Iterate over each line in the file
for (line_number, line_result) in reader.lines().enumerate() {
let line = line_result?; // Propagate IO errors
let line_to_check = if args.case_insensitive {
line.to_lowercase()
} else {
line.clone() // We need to own the string to pass to `contains`
};
if line_to_check.contains(&pattern_to_search) {
// Print the original line, not the lowercased one
println!("{}: {}", line_number + 1, line);
}
}
Ok(())
}This example showcases several key concepts:
- Structs and Traits: The
CliArgsstruct models our application’s configuration. The#[derive(Parser)]attribute is a procedural macro fromclapthat automatically implements the argument parsing logic. - Error Handling: The
mainfunction returns aio::Result<()>. The?operator provides a clean way to propagate errors, making the code robust and easy to read. - File I/O: Using
std::fs::Fileandstd::io::BufReaderprovides an efficient way to read large files line by line, a common task in Linux server news and log analysis.
Bridging Worlds: Interfacing with C and the Linux System
Despite Rust’s modern features, the Linux ecosystem is built on a foundation of C. The kernel, system libraries (`glibc`), and countless drivers are all written in C. To be a first-class citizen, Rust must be able to interoperate seamlessly with this existing code. This is achieved through its Foreign Function Interface (FFI).
The Power and Peril of `unsafe` Rust
Rust provides an unsafe keyword that allows you to bypass some of its compile-time safety checks. This is an explicit admission that the compiler cannot verify the safety of certain operations, primarily when calling C code, dereferencing raw pointers, or manipulating memory directly. Using unsafe is a contract: you, the programmer, are telling the compiler, “I have read the documentation and I guarantee this code is safe.” This capability is essential for deep system integration, a topic often covered in Linux kernel news and Linux drivers news.
Let’s see how to use FFI to call a function from the standard C library, libc, to get the current process ID.
// Import the `c_int` type from the libc crate.
// You would add `libc = "0.2"` to your Cargo.toml file.
extern crate libc;
fn main() {
// This is the function signature from the C library.
// We declare it in an `extern "C"` block to tell Rust
// to use the C Application Binary Interface (ABI).
extern "C" {
fn getpid() -> libc::c_int;
}
// Calling an external, non-Rust function is an unsafe operation.
// The Rust compiler cannot guarantee its safety (e.g., it might have
// side effects or not be thread-safe).
let pid = unsafe {
getpid()
};
println!("The current process ID is: {}", pid);
}This simple example opens up a world of possibilities. You can use this same mechanism to interact with any C library on a Linux system, from networking stacks (relevant to Linux networking news) to graphics libraries like those discussed in Mesa news and Vulkan Linux news.
Best Practices and the Growing Ecosystem
As you dive deeper into Rust development on Linux, adopting best practices will ensure your projects are maintainable, performant, and robust. This is crucial whether you’re managing containers with Docker (Docker Linux news) or automating infrastructure with Ansible (Ansible news).
Effective Error Handling
Rely on Rust’s Result<T, E> and Option<T> enums for handling operations that can fail or return no value. Avoid using .unwrap() or .expect() in production code, as they will cause your program to panic and exit. For more complex applications, consider using crates like anyhow for simple, flexible error handling, or thiserror for creating custom, structured error types.
Performance Tuning

Always compile your release builds with the --release flag (e.g., cargo build --release). This enables a host of compiler optimizations that dramatically increase performance. For identifying bottlenecks, standard Linux tools like perf work wonderfully with Rust binaries. You can generate flamegraphs to visualize where your application is spending its time, a critical practice for optimizing high-load services discussed in Linux performance news.
Cross-Compilation and Deployment
Rust’s tooling makes cross-compilation straightforward. With a single command like rustup target add aarch64-unknown-linux-gnu, you can set up your development machine to build binaries for different architectures, such as ARM for a Raspberry Pi (Raspberry Pi Linux news). For deployment, containerizing your application is a best practice. A multi-stage Dockerfile can produce a minimal, statically-linked container image, perfect for cloud environments and a hot topic in Kubernetes Linux news.
Conclusion: The Future is Written in Rust
Rust represents a monumental step forward for systems programming on Linux. It delivers on the promise of C-level performance while providing compile-time guarantees against the most common and dangerous types of bugs. Its modern tooling, with Cargo for package management and a powerful compiler, creates a development experience that is both productive and enjoyable.
The evidence of its impact is everywhere, from new command-line tools that are faster and safer than their predecessors to the ongoing, historic effort to integrate Rust directly into the Linux kernel. Whether you’re a DevOps engineer automating tasks on a CentOS news server, a desktop enthusiast on Manjaro news, or a cloud architect deploying on Azure Linux news, Rust offers a compelling set of tools to build the next generation of software. The time to start learning and building with Rust on Linux is now. Your journey begins with a simple command: rustup-init.sh.