A Deep Dive into Testing Linux Mail Servers with OpenSSL: A Comprehensive Guide for Administrators
In the world of Linux server administration, managing a mail server remains one of the most complex and critical tasks. Whether you’re running Postfix on a Debian server, Exim on Rocky Linux, or any other Mail Transfer Agent (MTA) on your favorite distribution, ensuring its reliability, security, and proper configuration is paramount. While modern mail clients and web interfaces provide a user-friendly experience, they often hide the intricate protocol-level conversations that can be a goldmine for troubleshooting. When things go wrong, administrators need a tool that can cut through the layers of abstraction and speak directly to the server.
This is where OpenSSL, the ubiquitous cryptography toolkit found on virtually every Linux system, shines as an unexpected but powerful diagnostic tool. Beyond its primary role in generating certificates and managing encryption, the openssl s_client utility allows you to establish a raw, interactive TLS/SSL connection to any service, including your mail server. This article provides a comprehensive guide for Linux administrators on how to leverage OpenSSL to test, debug, and audit SMTP, IMAP, and POP3 services, offering practical examples and best practices relevant to today’s secure email landscape. These techniques are essential for anyone involved in Linux administration, Linux DevOps, or network security.
Understanding Mail Protocols and the Role of OpenSSL
Before diving into practical commands, it’s crucial to have a solid grasp of the underlying email protocols and why OpenSSL is the perfect tool for interrogating them. A mail server is not a single entity but a collection of services, each speaking a different language.
A Quick Refresher on Core Email Protocols
Modern email infrastructure relies on three primary protocols:
- SMTP (Simple Mail Transfer Protocol): The workhorse for sending email. It’s used for client-to-server submission and server-to-server relaying. Key ports include Port 25 (server-to-server, often blocked by ISPs), Port 587 (client submission with mandatory STARTTLS encryption), and Port 465 (an older, but still common, port for implicit SSL/TLS, often called SMTPS).
- IMAP (Internet Message Access Protocol): Used by clients to retrieve and manage email. Its main advantage is that messages remain on the server, allowing for synchronization across multiple devices. Key ports are Port 143 (unencrypted, upgraded with STARTTLS) and Port 993 (implicit SSL/TLS, known as IMAPS).
- POP3 (Post Office Protocol): An older protocol for retrieving email, where messages are typically downloaded to the client and removed from the server. Key ports are Port 110 (unencrypted, upgraded with STARTTLS) and Port 995 (implicit SSL/TLS, known as POP3S).
The most important trend in Linux mail servers news is the universal push for encryption. Unencrypted connections are now considered a major security risk. STARTTLS provides a mechanism to upgrade a plain-text connection to an encrypted one, while implicit SSL/TLS connections are encrypted from the very beginning.
Why Use OpenSSL for Mail Server Testing?
While tools like telnet or nc (netcat) can connect to unencrypted ports, they are useless for modern, secure mail servers. The openssl s_client command is purpose-built to handle the TLS/SSL handshake, making it the ideal tool for manual testing. Here’s why it’s invaluable:
- Protocol-Level Interaction: You can send raw protocol commands and see the server’s verbatim responses, bypassing any interpretation by a mail client. This is crucial for diagnosing subtle configuration issues in Postfix news or Dovecot news.
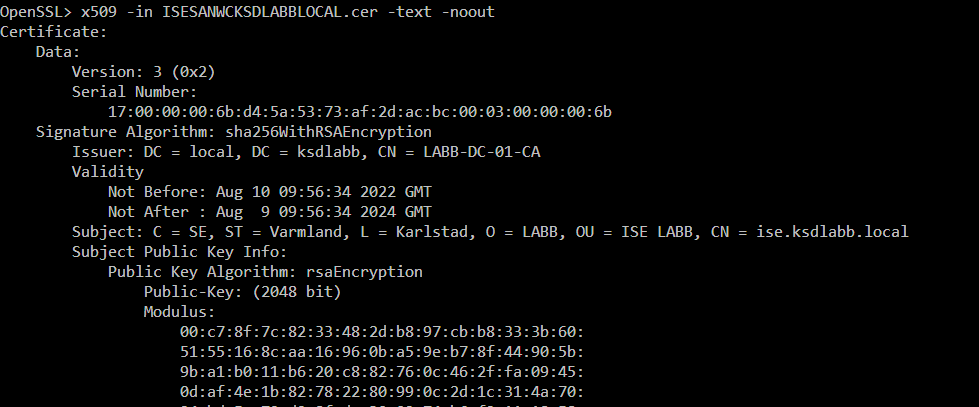
- Certificate Verification: It allows you to inspect the server’s SSL certificate, check its expiry date, and verify the certificate chain, which is a cornerstone of Linux security news.
- Cipher Suite Auditing: You can see which encryption algorithms and TLS versions the server supports, helping you enforce strong security policies and disable weak ciphers.
- Universal Availability: OpenSSL is pre-installed on nearly every Linux distribution, from Ubuntu news and Fedora news to enterprise systems like those covered in Red Hat news. No extra software is needed.
Hands-On SMTP Testing with OpenSSL
Let’s get practical. The most common task is to verify that the SMTP service is accepting connections, authenticating users, and sending mail correctly. These tests are vital after a configuration change or during a system outage.
Initiating a Secure SMTP Connection
Most modern mail clients submit email over port 587 using the STARTTLS command. This upgrades the connection from plaintext to TLS after the initial handshake. You can simulate this exact process with OpenSSL.
To connect to your server’s submission port, use the -starttls smtp flag:
openssl s_client -connect mail.example.com:587 -starttls smtpUpon a successful connection, the server will greet you with a “220” welcome banner, and OpenSSL will display a wealth of information about the TLS session, including the server certificate, the protocol version (e.g., TLSv1.3), and the negotiated cipher suite. If the connection fails, the error message will often point directly to the problem, such as a firewall block or a service not running.
Sending a Test Email Manually
Once connected, you can have a complete SMTP conversation to send an email. This is the ultimate test of your MTA’s configuration. After establishing the connection as shown above, you will type commands directly into your terminal.
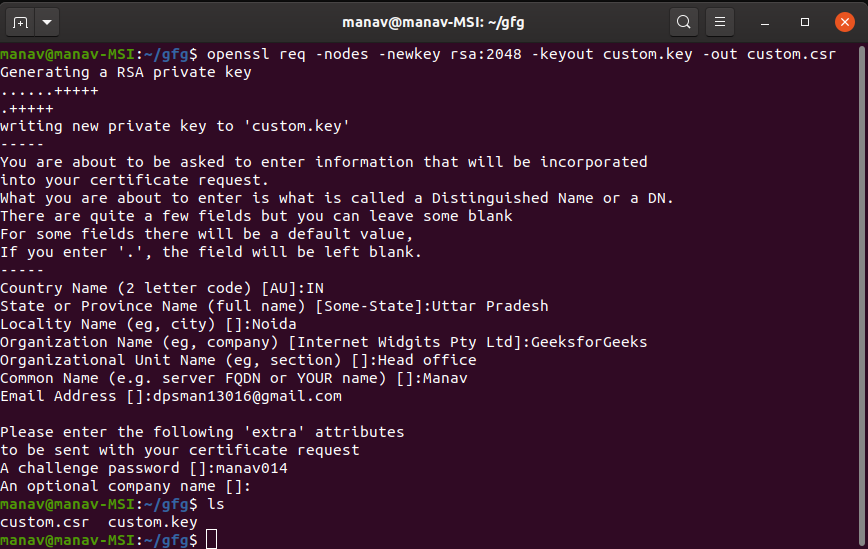
First, you need to authenticate. The common AUTH LOGIN mechanism requires your username and password to be encoded in Base64. You can generate these on the command line:
# To encode your username (e.g., '[email protected]')
$ echo -ne '[email protected]' | base64
dXNlckBleGFtcGxlLmNvbQ==
# To encode your password (e.g., 'SuperSecretPa$$w0rd')
$ echo -ne 'SuperSecretPa$$w0rd' | base64
U3VwZXJTZWNyZXRQYSQkdDByZA==Now, let’s put it all together in an interactive session. The lines you type are prefixed with `(you)` for clarity.
# 1. Connect to the server
openssl s_client -connect mail.example.com:587 -starttls smtp
# Server responds with connection details and a 220 banner...
# 220 mail.example.com ESMTP Postfix
# 2. Now, you start typing the SMTP commands
(you) EHLO client.domain.com
# Server responds with its capabilities, including AUTH LOGIN
# 250-mail.example.com
# 250-PIPELINING
# 250-SIZE 10240000
# 250-VRFY
# 250-ETRN
# 250-AUTH PLAIN LOGIN
# 250-ENHANCEDSTATUSCODES
# 250-8BITMIME
# 250 DSN
(you) AUTH LOGIN
# Server responds with 334 VXNlcm5hbWU6 (prompt for username)
# 334 VXNlcm5hbWU6
(you) dXNlckBleGFtcGxlLmNvbQ==
# Server responds with 334 UGFzc3dvcmQ6 (prompt for password)
# 334 UGFzc3dvcmQ6
(you) U3VwZXJTZWNyZXRQYSQkdDByZA==
# Server responds with 235 Authentication successful
# 235 2.7.0 Authentication successful
(you) MAIL FROM:<[email protected]>
# 250 2.1.0 Ok
(you) RCPT TO:<[email protected]>
# 250 2.1.5 Ok
(you) DATA
# 354 End data with <CR><LF>.<CR><LF>
(you) From: Test Sender <[email protected]>
(you) To: Test Recipient <[email protected]>
(you) Subject: Manual OpenSSL SMTP Test
(you) This is a test message sent directly via OpenSSL.
(you) If you are reading this, the test was successful.
(you) .
# 250 2.0.0 Ok: queued as 1A2B3C4D5E
(you) QUIT
# 221 2.0.0 ByeThis detailed interaction allows you to pinpoint failures at any stage—authentication, sender/recipient validation, or data submission. A “535 Authentication failed” error, for example, tells you the credentials are wrong, while a “550 Relay access denied” points to a misconfiguration in your MTA’s relay policies.
Testing IMAP and POP3 Services
Verifying mail retrieval is just as important as testing submission. OpenSSL can connect to secure IMAP (port 993) and POP3 (port 995) services to ensure your Mail Delivery Agent (MDA), such as Dovecot, is functioning correctly.
Verifying IMAP Connectivity and Authentication
IMAP allows for more complex interactions, like listing mailboxes and checking messages. Here’s a simple test to log in and list mailboxes. Unlike SMTP’s conversational style, IMAP commands are tagged (e.g., `a01`, `a02`) so the client can match responses to requests.
# Connect to the secure IMAP port
openssl s_client -connect mail.example.com:993
# After connection, type the following commands.
# Note: Unlike SMTP, you send the password in plaintext here.
(you) a01 LOGIN [email protected] SuperSecretPa$$w0rd
# * OK [CAPABILITY IMAP4rev1 LITERAL+ SASL-IR LOGIN-REFERRALS ID ENABLE IDLE] Logged in
# a01 OK Logged in.
(you) a02 LIST "" "*"
# * LIST (\HasNoChildren) "." "INBOX"
# * LIST (\HasChildren \Noselect) "." "Archive"
# * LIST (\HasNoChildren) "." "Sent"
# * LIST (\HasNoChildren) "." "Trash"
# a02 OK List completed.
(you) a03 SELECT INBOX
# * FLAGS (\Answered \Flagged \Deleted \Seen \Draft)
# * OK [PERMANENTFLAGS (\Answered \Flagged \Deleted \Seen \Draft \*)] Flags permitted.
# * 4 EXISTS
# * 0 RECENT
# * OK [UNSEEN 1] First unseen.
# * OK [UIDVALIDITY 1609459200] UIDs valid
# * OK [UIDNEXT 5] Predicted next UID
# a03 OK [READ-WRITE] Select completed.
(you) a04 LOGOUT
# * BYE Logging out
# a04 OK Logout completed.This test confirms that authentication is working and that the user’s mailboxes are accessible. Errors here often relate to incorrect authentication backends or file permission issues in the user’s mail storage directory, a common topic in Linux filesystems discussions.
Advanced Security Checks and Best Practices
Beyond basic connectivity tests, OpenSSL is a powerful tool for security auditing. Ensuring your server uses strong encryption is non-negotiable in today’s threat landscape.
Auditing TLS/SSL Ciphers and Protocols
You should disable outdated protocols like SSLv3, TLS 1.0, and TLS 1.1. You can use OpenSSL to check if your server correctly rejects connections using these weak protocols.
# This command should FAIL on a securely configured server
openssl s_client -connect mail.example.com:465 -tls1_1A properly configured server will result in a handshake failure. If it connects, you need to adjust your mail server’s TLS configuration (e.g., `smtpd_tls_mandatory_protocols` in Postfix) to exclude outdated versions. This is a critical aspect of Linux firewall news and hardening guides for distributions like Kali Linux news or Parrot OS news.
Automating Health Checks with Shell Scripting
Manually typing commands is great for debugging, but for regular health checks, automation is key. You can create a simple bash script to perform a non-interactive SMTP authentication test. This is a perfect addition to a monitoring system or a CI/CD pipeline, reflecting trends in Linux CI/CD news.
This script uses a “here document” to pipe commands to `openssl` and checks the server’s response for the authentication success code.
#!/bin/bash
SERVER="mail.example.com"
PORT="587"
USERNAME="[email protected]"
PASSWORD="YourMonitoringPassword"
# Base64 encode credentials for the AUTH LOGIN method
USER_B64=$(echo -ne "$USERNAME" | base64)
PASS_B64=$(echo -ne "$PASSWORD" | base64)
# Use process substitution and a timeout to run the check
# The -quiet flag suppresses certificate and session output
RESPONSE=$(timeout 15 openssl s_client -connect $SERVER:$PORT -quiet -starttls smtp 2>/dev/null <<EOF
EHLO monitor.local
AUTH LOGIN
$USER_B64
$PASS_B64
QUIT
EOF
)
# Check for the SMTP success code "235"
if echo "$RESPONSE" | grep -q "235"; then
echo "SUCCESS: SMTP authentication for $USERNAME on $SERVER:$PORT is working."
exit 0
else
echo "FAILURE: SMTP authentication failed on $SERVER:$PORT."
echo "--- Last few lines of Server Response ---"
echo "$RESPONSE" | tail -n 5
exit 1
fiThis script can be integrated with monitoring tools like Nagios or Prometheus (via the Blackbox Exporter), providing automated alerts and aligning with modern Linux observability news and practices.
Conclusion and Next Steps
Mastering the use of openssl s_client is a significant step toward becoming a more effective Linux mail server administrator. It demystifies the complex interactions happening under the hood, providing a direct line to your SMTP, IMAP, and POP3 services for unparalleled troubleshooting and security validation. By understanding how to manually negotiate a TLS session, authenticate, and send protocol commands, you can diagnose issues that are often obscured by high-level tools and client applications.
The key takeaways are clear: OpenSSL is an essential, built-in utility for verifying certificate configurations, testing authentication mechanisms, auditing TLS protocol and cipher strength, and performing end-to-end mail flow tests. We encourage you to incorporate these manual checks into your routine maintenance and to leverage the scripting examples to build automated health checks for your infrastructure.
As a next step, consider integrating these scripted checks into a broader monitoring framework like Prometheus or Zabbix. By doing so, you transform a powerful manual diagnostic technique into a proactive, automated system that ensures the health and security of your mail services, keeping you ahead of potential issues and ensuring your communication platform remains robust and reliable.



