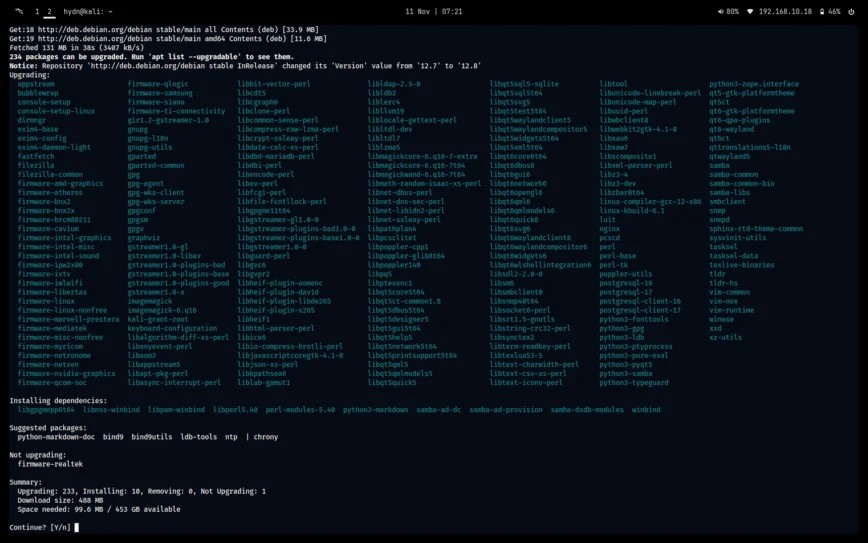
Operating Systems
Pop!_OS Leaps Forward: A Deep Dive into the Linux 6.8 Kernel Upgrade
In the dynamic world of Linux distributions, staying current is not just a feature—it’s a statement of intent.
Mastering Linux File Permissions: A Comprehensive Guide to Securing Your System
The Unsung Hero of System Security: A Deep Dive into Linux File Permissions In the world of Linux, from the sprawling server farms powering cloud.
Beyond systemd: A Technical Deep Dive into OpenRC for Modern Linux Systems
Introduction: The Heart of the Linux Boot Process In the vast and diverse world of the Linux operating system, the init system is the foundational process.
Securing Your Linux Servers: Understanding and Mitigating the OpenSSH ‘regreSSHion’ Vulnerability (CVE-2024-6387)
In the world of Linux administration, few tools are as fundamental and ubiquitous as OpenSSH. It is the bedrock of secure remote management, file.
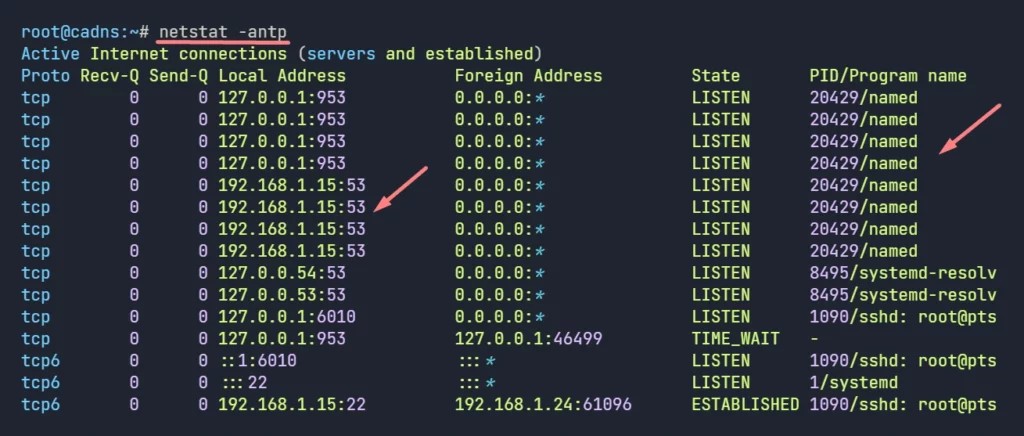
The Evolving Landscape of Linux DNS: Securing Network Communications with DNS-over-HTTPS
The Double-Edged Sword of DNS Encryption on Linux The Domain Name System (DNS) is the foundational directory of the internet, a critical yet historically.
WireGuard Ascendant: From Simple VPN to the Backbone of Zero-Trust Security
WireGuard has rapidly transformed the landscape of virtual private networking. Heralded for its simplicity, state-of-the-art cryptography, and remarkable.
Mastering Remote MariaDB Connections on Linux: A Comprehensive Guide for Developers and Admins
In today’s distributed application architecture, the ability to securely and efficiently connect to a remote database is no longer a niche skill but a.
A Deep Dive into the Recent Linux Kernel SELinux Vulnerability: A Guide for System Administrators
In the ever-evolving landscape of cybersecurity, the Linux kernel remains a central battleground. As the core of countless operating systems, from.
Kubernetes 1.29 Deep Dive: What the Latest Release Means for the Linux Ecosystem
The Symbiotic Relationship: How Kubernetes 1.29 Redefines Linux Container Orchestration The world of cloud-native computing is in a constant state of.
When Security Tools Cause System Instability: A Proactive Guide for Rocky Linux Administrators
The Paradox of Protection: When Security Agents Destabilize Enterprise Linux In the world of enterprise computing, stability is paramount.