Clang and LLVM’s Latest Evolution: Enhanced Code Safety, Performance Analysis, and the Future of C++ Compilation
The LLVM compiler infrastructure, including its flagship C++ front-end Clang, is a cornerstone of modern software development. Its relentless pace of innovation continues to provide developers with powerful tools to write safer, faster, and more robust code. For professionals across the entire spectrum of Linux development, from embedded systems on a Raspberry Pi to massive server deployments on Red Hat or Debian, staying abreast of these changes is crucial. Recent advancements in the ecosystem are not just incremental; they represent significant leaps in static analysis, micro-architectural performance tuning, and the very foundations of C++ compilation. These updates are vital Clang news and LLVM news for anyone serious about high-performance software engineering.
This article delves into several groundbreaking features that are shaping the future of development on Linux. We will explore a new attribute that brings printf-style type safety to custom functions, examine how performance analysis is becoming more precise with expanded RISC-V support, and look ahead to a new Clang Intermediate Representation (CIR) that promises more powerful optimizations. Finally, we’ll cover tooling that automates the tedious process of compiler bug reporting, strengthening the entire open-source ecosystem. These developments are not just theoretical; they have practical implications for developers using any major Linux distribution, from Ubuntu news and Fedora news to Arch Linux news and SUSE Linux news.
Enhancing Code Safety with __attribute__((format_matches))
One of the oldest and most persistent sources of bugs and security vulnerabilities in C and C++ programs is the misuse of variadic functions like printf and scanf. A mismatch between the format string specifiers (e.g., %d, %s) and the actual types of the arguments passed can lead to undefined behavior, crashes, and critical security flaws. While compilers have long been able to check the standard library functions, this protection didn’t automatically extend to custom wrappers, a common pattern in logging libraries and other utilities.
The Problem with Custom Logging Wrappers
Consider a common scenario: a developer creates a custom logging function to prefix messages with a timestamp or severity level. This function often takes a format string and a variable number of arguments, passing them internally to vfprintf. Without specific compiler guidance, any type mismatches in the calling code would go completely undetected, creating a latent bug that might only surface in production. This is a recurring theme in Linux security news and a constant concern for system administrators managing Linux server news.
Compile-Time Validation with a New Attribute
The newly introduced __attribute__((format_matches("checker_name"))) solves this problem elegantly. It allows a developer to “tag” their own variadic function, telling Clang that its arguments should be validated according to the rules of a known format checker, such as printf, scanf, or strftime. This delegates the complex task of format string parsing and type checking to the compiler’s battle-tested internal logic.
Let’s look at a practical example. Here is a simple, unsafe logging function:
#include <stdio.h>
#include <stdarg.h>
// Unsafe wrapper: The compiler does not check the format string against arguments.
void log_message_unsafe(const char* format, ...) {
va_list args;
va_start(args, format);
printf("[LOG]: ");
vprintf(format, args);
va_end(args);
}
void run_unsafe_example() {
// This is a bug! %s expects a 'const char*', but gets an 'int'.
// This will likely crash, but compiles without a warning.
log_message_unsafe("User ID %s logged in.\n", 12345);
}Now, let’s apply the new attribute to create a safe version. We tell Clang that our function’s format string (the 1st argument) and variadic arguments (starting from the 2nd argument) should match the rules of printf.
#include <stdio.h>
#include <stdarg.h>
// Safe wrapper: Clang will now validate this function's arguments like printf.
// The attribute tells the compiler to use the "printf" checker.
// The first '1' refers to the format string argument index (1-based).
// The second '2' refers to the start of the variadic arguments index.
__attribute__((format_matches("printf", 1, 2)))
void log_message_safe(const char* format, ...);
void log_message_safe(const char* format, ...) {
va_list args;
va_start(args, format);
printf("[LOG]: ");
vprintf(format, args);
va_end(args);
}
void run_safe_example() {
// With the attribute, Clang now issues a warning:
// warning: format '%s' expects argument of type 'char *', but argument 2 has type 'int'
log_message_safe("User ID %s logged in.\n", 12345);
}This simple addition transforms a runtime error into a compile-time warning, dramatically improving code quality and security. For any project that uses custom logging or printing abstractions, from desktop applications on GNOME news or KDE Plasma news to system services managed by systemd news, adopting this feature is a significant win.
Deep Performance Analysis with llvm-exegesis and RISC-V
Optimizing code for modern CPUs requires a deep understanding of their micro-architectural behavior. It’s often not enough to know the algorithm’s complexity; you need to know how a specific sequence of instructions will perform on a given processor pipeline. The llvm-exegesis tool is designed for exactly this kind of micro-benchmarking, and its capabilities are continually expanding.
Probing CPU Performance at the Instruction Level
Unlike traditional benchmarks that measure the performance of an entire application, llvm-exegesis focuses on small, isolated code snippets. It can measure key performance characteristics like instruction latency (how long an instruction takes to complete), inverse throughput (how often an instruction can be issued), and port pressure (which execution units are being used). This level of detail is invaluable for performance-sensitive domains like scientific computing, game development (a hot topic in Linux gaming news), and signal processing. This tool is a boon for anyone tracking Linux performance metrics.
Embracing the Future with RISC-V Vector Support
A major recent development is the addition of robust support for the RISC-V Vector (RVV) extension in llvm-exegesis. RISC-V is an open-standard instruction set architecture gaining tremendous traction in both embedded systems and high-performance computing. The RVV extension provides powerful SIMD (Single Instruction, Multiple Data) capabilities, crucial for tasks involving large datasets. With this new support, developers can now:
- Analyze the performance of hand-written RISC-V vector assembly.
- Validate the code generation quality of the compiler for vectorized C/C++ code.
- Compare the performance of different instruction sequences to find the optimal solution for a specific RISC-V core.
Here is a conceptual example of how one might use llvm-exegesis with a YAML configuration to measure the throughput of a RISC-V vector addition instruction.
# To run: llvm-exegesis -mode=inverse_throughput -mcpu=sifive-u74 -snippets-file=rvv_test.yaml
---
triple: 'riscv64-unknown-linux-gnu'
arch: riscv64
# We need to enable the vector extension ('v') and standard extensions.
cpu_features: '+m,+a,+f,+d,+c,+v'
# The code snippet to be benchmarked.
# This performs a vector addition on 32-bit integer elements.
instructions: |
# Set vector length (vl) and element width (vsew)
vsetvli a0, zero, e32, m1, ta, ma
# Vector add v2 and v3, storing the result in v1
vadd.vv v1, v2, v3
...This capability is critical for the growing ecosystem around RISC-V hardware. As more devices, from IoT sensors to HPC clusters, adopt this architecture, tools like llvm-exegesis become essential for extracting maximum performance. This is directly relevant to Linux hardware news and the broader Linux open source movement pushing for open standards.
The Future of C++ Compilation: Clang IR (CIR)
For years, the Clang compilation pipeline has followed a traditional path: source code is parsed into an Abstract Syntax Tree (AST), which is then “lowered” directly into LLVM Intermediate Representation (IR). While effective, this lowering process loses a significant amount of high-level, source-specific information. The Clang IR (CIR) project, built upon the Multi-Level Intermediate Representation (MLIR) framework, aims to revolutionize this process.
A Higher-Level Intermediate Representation
CIR is a new IR that sits between the AST and LLVM IR. Its primary goal is to preserve much more of the C++ source code’s structure and semantics. For example, where LLVM IR only has basic blocks and terminators, CIR has explicit representations for loops (cir.for, cir.while), conditional statements (cir.if), and C++ scopes. This retention of high-level information opens the door for a new class of powerful analyses and transformations that are difficult or impossible to perform on the lower-level LLVM IR.

The Power of `cir-opt`
Accompanying CIR is the cir-opt tool, a dedicated optimizer that operates on this new representation. Because cir-opt understands concepts like loops and object lifetimes directly, it can perform more intelligent transformations. Potential applications include:
- Smarter Optimizations: More aggressive loop transformations, better analysis of object lifetimes for memory optimization, and improved inlining decisions.
- Enhanced Tooling: Richer static analysis and more accurate refactoring tools within IDEs like VS Code Linux news. The preserved structure makes it easier to map diagnostics back to the original source code.
- Interoperability: MLIR’s design facilitates the creation of “dialects” for different languages and domains, potentially simplifying interoperability between C++ and other languages like Fortran or specialized hardware accelerators.
This is a forward-looking initiative, but it represents a fundamental shift in compiler architecture. As this work matures, it will have a profound impact on the C++ Linux news landscape, enabling developers on all platforms, from Debian news to CentOS news, to benefit from a more intelligent and capable compiler.
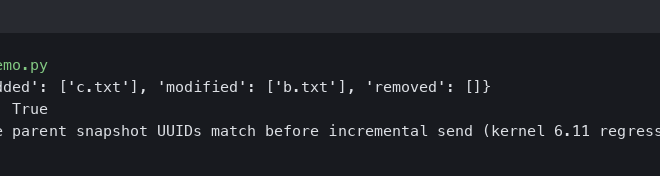
Streamlining Bug Reduction with C-Vise
Anyone who has reported a compiler bug knows the challenge: you have a large, complex project that fails to compile or produces incorrect code, but the bug report is only useful if it includes a minimal, self-contained example that reproduces the problem. Manually reducing a multi-thousand-line source file into a ten-line snippet is a tedious and time-consuming process.
Automating Test Case Reduction
C-Vise is a powerful tool designed to automate this process. It’s a test-case reducer for C and C++ that takes a source file and a script that checks for the bug (e.g., a script that runs the compiler and checks for a crash). It then intelligently and repeatedly applies various reduction techniques—removing functions, simplifying expressions, deleting lines of code—until it arrives at the smallest possible version that still triggers the bug.
Using C-Vise is typically done from the command line. A developer provides the tool with the initial failing code and a test script.
#!/bin/bash
# test_script.sh: A script to check for the compiler crash.
# Compile the input file (passed as $1 by cvise).
# We redirect stderr to check for the crash message.
clang -c "$1" -o /dev/null &> compiler_output.txt
# Check if the output contains the specific error message or backtrace.
# Exit with 0 if the bug is present (interesting case for cvise).
# Exit with 1 if the bug is NOT present (uninteresting case).
if grep -q "LLVM ERROR: Ran out of registers" compiler_output.txt; then
exit 0
else
exit 1
fiWith this script, a developer can invoke C-Vise on their large, problematic source file:
$ cvise ./test_script.sh my_large_crashing_file.cpp
The tool will then work its magic, ultimately producing a much smaller my_large_crashing_file.cpp.reduced file. This greatly accelerates the bug-fixing process for compiler developers, which in turn leads to a more stable toolchain for the entire community. This is fantastic Linux DevOps news, as it improves the stability of CI/CD pipelines (e.g., GitLab CI news, GitHub Actions Linux news) that rely on the latest compilers.
Conclusion and Next Steps
The LLVM and Clang ecosystem is more vibrant and innovative than ever. The recent advancements we’ve explored highlight a clear focus on the complete developer experience: from writing safer code with compile-time checks like format_matches, to achieving peak performance with micro-architectural analysis via llvm-exegesis, to building a foundation for future optimizations with CIR. Paired with practical tooling like C-Vise that strengthens the feedback loop between users and developers, the trajectory is clear: Clang is evolving into a comprehensive suite for building the next generation of software.
For developers and system administrators in the Linux world, the key takeaway is to embrace these new capabilities. As new versions of Clang become available through your distribution’s package manager—whether it’s apt on Debian, dnf on Fedora, or pacman on Arch—take the time to explore the release notes and integrate these features into your workflow. By leveraging these powerful tools, you can improve your code’s quality, performance, and security, contributing to a stronger and more reliable open-source landscape.