
From Containerfile to Bootable OS: The Next Evolution in Linux System Deployment with Podman
Introduction: A Paradigm Shift in Operating System Management
For decades, the world of Linux server administration has followed a well-trodden path: provision a machine, install a base operating system from an ISO, and then layer on configuration using shell scripts or sophisticated configuration management tools like Ansible, Puppet, or Chef. This mutable approach, while powerful, often leads to configuration drift, complex state management, and challenges in creating truly reproducible environments. The latest Podman news signals a dramatic shift in this paradigm, borrowing battle-tested principles from the world of application containerization to revolutionize how we build, deploy, and manage entire operating systems.
Imagine defining your entire server—from the kernel and systemd services to user-space applications—in a single, version-controlled `Containerfile`. Imagine building this definition into an OCI-compliant image, pushing it to a registry, and then booting bare-metal machines or virtual machines directly from it. This is not science fiction; it’s the reality of bootable container images. This article explores this groundbreaking technology, detailing how you can leverage tools within the Podman ecosystem to transform a simple `Containerfile` into a fully bootable, immutable, and atomically updatable Linux OS. This evolution represents a significant milestone in Linux DevOps news, promising unprecedented consistency from development to production across any infrastructure.
The Core Concept: What Are Bootable Container Images?
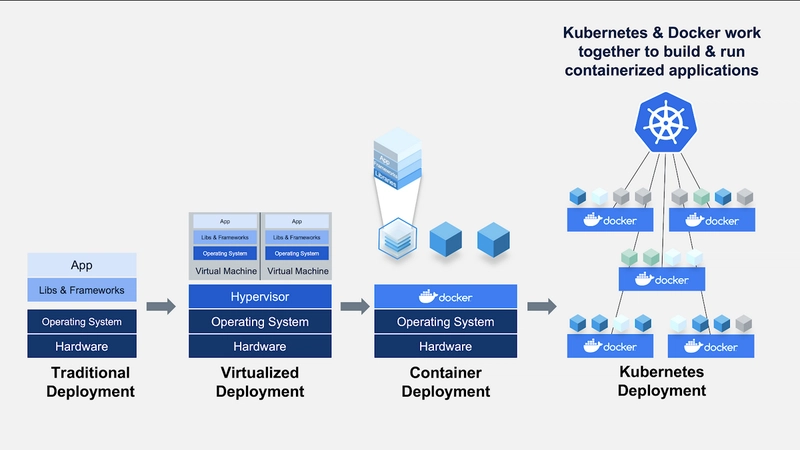
At its heart, the concept is about extending the container model to encompass the entire operating system. Instead of just packaging an application and its dependencies, we are packaging the full user space of a host OS. This creates a powerful link between the mature tooling of Linux containers news and the foundational layer of system administration.
From Application Containers to OS Containers
An application container, managed by tools like Podman or Docker, is designed to run a single process or service in an isolated environment. A bootable OS container, by contrast, is designed to be the environment. It contains a complete OS tree, including an init system like `systemd`, essential system services, drivers, and the necessary tooling to manage the host. The key distinction is the “payload.” Instead of an Nginx binary or a Python application, the payload is `systemd` and the entire collection of services it manages. This approach is gaining traction in distributions central to Red Hat news and Fedora news, which are pioneering these immutable, container-native operating systems.
The Technology Stack: OCI, systemd, and Bootloaders
This innovation stands on the shoulders of giants. Several key technologies make bootable OS images possible:
- OCI (Open Container Initiative) Images: The standardized image format is the cornerstone. It provides a universal, portable, and content-addressable way to package the OS filesystem layers. This means an OS built on a developer’s laptop is bit-for-bit identical to the one deployed in the cloud.
- systemd: As the de facto init system for most major Linux distributions (from Debian news to Arch Linux news), `systemd` is crucial. It’s responsible for bootstrapping the user space, managing services, and handling system state once the Linux kernel has finished its initialization. The latest systemd news often includes features that better support containerized and immutable environments.
- Bootloaders (GRUB, systemd-boot): Specialized tooling is required to unpack the OCI image and pivot the system’s root filesystem into it during the boot process. This is where projects like `bootc` come in, acting as the bridge between the container image and the machine’s boot process, often integrating with bootloaders like GRUB.
Key Benefits: Immutability, Atomicity, and Verifiability
Adopting this model offers three transformative advantages:
- Immutability: The running OS filesystem (`/usr`) is treated as read-only. This prevents ad-hoc changes and configuration drift, ensuring the system remains in its intended state. All changes are made by building a new image and deploying it.
- Atomicity: Updates are atomic. When a new version of the OS image is deployed, the system downloads it and stages it. The switch to the new version happens on the next reboot. If the boot fails, the system can automatically roll back to the previous, known-good version. This eliminates broken states from partially failed updates, a common pain point in Linux administration news.
- Verifiability: Since the OS is just an OCI image, it can be signed and verified using tools like `cosign`. This provides a strong cryptographic guarantee that the OS running on a server is exactly the one built and approved in your CI/CD pipeline, a massive win for Linux security news.
Building Your First Bootable OS from a Containerfile
Let’s move from theory to practice. Creating a bootable OS starts with a familiar tool: the `Containerfile`. The process leverages standard Podman commands, making it accessible to anyone already working with containers.
Crafting the `Containerfile`
A `Containerfile` for a bootable OS looks similar to one for an application, but with a focus on system-level packages. Instead of installing a single application, you install the tools needed for a functioning server. This example uses a Fedora base to create a minimal OS with a web server and SSH access.
# Use a base image that is suitable for a bootable system.
# Fedora, CentOS Stream, and others are excellent choices.
FROM fedora:latest
# Install essential packages for a bootable system and our payload.
# dnf is the package manager here, relevant to dnf news.
RUN dnf -y install nginx openssh-server policycoreutils-python-utils && \
dnf -y clean all && \
# Enable core services via systemd presets
systemctl enable sshd.service && \
systemctl enable nginx.service
# Set a root password (INSECURE: for demo purposes only).
# In a real scenario, use SSH keys or an Ignition/Kickstart configuration.
RUN echo "root:podman" | chpasswd
# Expose ports for our services
EXPOSE 80 22
# The CMD/ENTRYPOINT are typically not used for bootc, as systemd is the entrypoint.
# This file defines the OS content, not the runtime process.In this file, we install `nginx` and `openssh-server`. Crucially, we use `systemctl enable` to ensure these services are started by `systemd` on boot. This is a key step that differentiates an OS container from a simple application container.
Building and Storing the Image with Podman
Once the `Containerfile` is ready, you use standard `podman` commands to build and push it to a container registry. This could be Quay.io, Docker Hub, or your own private registry.
# Define a name for our bootable OS image
IMAGE_NAME="quay.io/my-org/my-bootable-nginx-os:latest"
# Build the image using Podman
# This is a standard process covered in Linux containers news
podman build -t ${IMAGE_NAME} .
# Log in to your container registry
podman login quay.io
# Push the image to the registry
podman push ${IMAGE_NAME}At this point, your entire operating system is packaged and stored as a versioned artifact in a registry. This workflow is instantly familiar to any developer or DevOps engineer and integrates seamlessly with existing Linux CI/CD news tools like GitLab CI or GitHub Actions.
Deployment and Lifecycle Management
With the image built and pushed, the next step is to deploy it to a target—be it a virtual machine, a cloud instance, or a bare-metal server. This is where specialized tools come into play to handle the “boot from container image” process.
From Image to Running System: The `bootc` Tool
The `bootc` project is an emerging standard for managing bootable container image deployments. It’s a set of tools and specifications designed to install, update, and manage systems running from OCI images. To deploy our image to a disk (e.g., `/dev/vda` in a VM), you would boot a live environment (like a Fedora ISO) and run a command to install the image to the disk.
# In a live environment with bootc installed...
# Install the bootable image from our registry to the target disk
# This will partition the disk, format filesystems, and set up the bootloader.
bootc install to-disk \
--image quay.io/my-org/my-bootable-nginx-os:latest \
/dev/vda
# After this command completes, you can reboot the machine.
# It will boot directly into the OS defined in your container image.
rebootThis command handles the complex low-level tasks: creating partitions, setting up filesystems like Btrfs or LVM for atomic snapshots (relevant to Btrfs news), installing the bootloader (GRUB), and pulling the container image layers onto the disk. Upon reboot, the machine will be running your custom-built Nginx server OS.
Atomic Updates and Rollbacks
The real power of this model shines during updates. Let’s say you’ve pushed a new version of your image with an updated Nginx configuration (`quay.io/my-org/my-bootable-nginx-os:v2`). Updating the running server is a single command.
# SSH into the running server
# Check the current status
bootc status
# Pull the new image version and stage it for the next boot
bootc upgrade
# Reboot to apply the update
# The system will atomically switch to the new image.
# If the boot fails, it will automatically roll back to the previous version.
systemctl rebootThis `bootc upgrade` command pulls the latest tag from the original image source, stages it, and modifies the bootloader configuration. The next boot will load the new OS. This process is incredibly robust and is a game-changer for managing fleets of servers, especially in edge computing and IoT scenarios, a hot topic in Linux embedded news.
Best Practices and Advanced Considerations
While powerful, this approach requires a shift in thinking. Here are some best practices and potential pitfalls to consider.
Managing Persistent State and Configuration
Since `/usr` is immutable, how do you manage data and configuration? The answer is to strictly separate the OS from its state.
- Persistent Data: Applications should write their data to `/var`, which is a separate, persistent partition. For example, PostgreSQL Linux news or MySQL Linux news would have their data directories located in `/var/lib/pgsql`.
- Configuration: Machine-specific configuration (like hostnames or network settings) should be stored in `/etc`. This directory is typically managed as a writable overlay, but best practice is to inject configuration at first boot using tools like Ignition or cloud-init, rather than modifying it on a live system.
Security Implications: SELinux, AppArmor, and Image Signing
Security is paramount. An immutable OS provides a strong security posture out of the box.
- SELinux/AppArmor: Ensure your base image is configured with strong security policies. Because the OS doesn’t change, these policies are more reliable and easier to maintain. This is a core component of Linux SELinux news.
- Image Signing: Always sign your images using tools like `cosign`. The `bootc` tool can be configured to verify these signatures before an upgrade, preventing the deployment of tampered or unauthorized OS images.
- Minimalism: Keep your base images as small as possible. Don’t include debugging tools, compilers (`GCC news`), or unnecessary services in your production images. Build separate, dedicated images for different environments.
Pitfalls to Avoid: Image Bloat and Secret Management
Common container pitfalls also apply here. Avoid creating massive, bloated images by combining too many concerns. Instead, create specialized OS images for different roles (e.g., a web server OS, a database OS). Furthermore, never bake secrets like passwords or API keys directly into your `Containerfile`. Use a proper secrets management solution to inject them at runtime or via an initial configuration tool.
Conclusion: The Future of OS Deployment is Declarative
The move towards bootable container images represents a major leap forward in the field of Linux system administration and DevOps. By applying the declarative, immutable, and version-controlled principles of containerization to the entire operating system, we can achieve an unprecedented level of consistency, reliability, and security. Tools like Podman and `bootc` are at the forefront of this movement, making it easier than ever to define an entire OS in a `Containerfile`, build it with a single command, and deploy it atomically across any environment.
As this technology matures, it will likely become the standard for deploying everything from edge devices and IoT fleets to massive cloud server farms. For anyone involved in Linux server news or managing infrastructure, now is the time to start experimenting. Convert a simple server setup into a `Containerfile`, build it with Podman, and explore the future of truly reproducible, bootable systems.



