
Mastering Modern Email Delivery: A Deep Dive into Dovecot for Secure Linux Mail Servers
In an era dominated by cloud-based services, the decision to self-host an email server is a powerful statement about data ownership, privacy, and control. For system administrators and DevOps professionals, building a robust, secure, and efficient mail server remains a critical skill. At the heart of nearly every modern open-source email stack lies a powerful duo: Postfix for sending and receiving mail (SMTP) and Dovecot for allowing users to access it. While Postfix handles the mail transport, Dovecot is the sophisticated, secure gatekeeper to the user’s mailbox, providing IMAP and POP3 services. This is a cornerstone of modern Linux mail servers news.
This article will serve as a comprehensive technical guide to Dovecot, moving beyond a simple installation to cover the nuances of secure configuration, integration with Postfix, and performance optimization. We will explore why Dovecot has become the de facto standard for IMAP/POP3 services on everything from Ubuntu news and Debian news servers to enterprise-grade Red Hat news and Rocky Linux news deployments. Whether you are a seasoned administrator looking to refresh your knowledge or a newcomer building your first mail server, this guide will provide the actionable insights and practical code examples needed to master Dovecot in today’s security-conscious landscape.
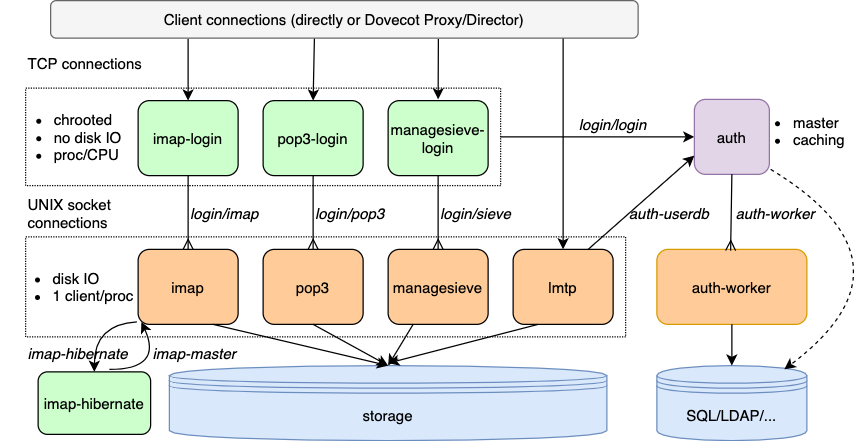
The Heart of Your Mailbox: Understanding Dovecot’s Core Architecture
Before diving into configuration files and commands, it’s essential to understand Dovecot’s role within the email ecosystem. A common misconception is that a single piece of software handles all email functions. In reality, a mail server is a collection of specialized services working in concert. Postfix is the Mail Transfer Agent (MTA), responsible for the SMTP protocol—the internet’s postal service. Dovecot, on the other hand, is the Mail Delivery Agent (MDA) and, more importantly, the Mail Access Agent (MAA), providing the interface for a user’s email client (like Thunderbird, Outlook, or a mobile client) to read, manage, and organize their messages.
IMAP vs. POP3: Choosing the Right Protocol
Dovecot provides access to mailboxes using two primary protocols: POP3 and IMAP. While it supports both excellently, understanding their differences is key to building a modern mail server.
- POP3 (Post Office Protocol 3): This is the older of the two. A client connecting via POP3 typically downloads all new messages from the server to the local machine and then deletes them from the server. It’s a simple, one-way street. Its main drawback is the lack of synchronization; mail read on your desktop won’t appear as read on your phone.
- IMAP (Internet Message Access Protocol): IMAP is the modern standard. It treats the server as the single source of truth. When a client connects, it synchronizes its state with the server. Emails are stored on the server, and actions like reading a message, moving it to a folder, or deleting it are reflected across all connected devices. This multi-device synchronization is why IMAP is the preferred choice for almost all use cases today.
Dovecot is highly optimized for IMAP, offering features like fast indexing and low-latency operations, making it a top performer in the Linux server news community.
The Symbiotic Relationship with Postfix
The real power of this stack comes from the tight integration between Postfix and Dovecot. The typical mail flow looks like this: An incoming email arrives at your server via SMTP and is accepted by Postfix. Postfix then passes the email to a local delivery agent (often provided by Dovecot itself, called Dovecot LDA) which places it into the user’s mailbox on the server’s filesystem. When the user opens their email client, Dovecot reads from that mailbox and serves the content via IMAP.
A critical integration point is SASL (Simple Authentication and Security Layer). Instead of managing separate user databases for sending mail (SMTP) and reading mail (IMAP), you can configure Postfix to delegate authentication requests to Dovecot. This means Dovecot becomes the sole authority for user credentials, simplifying user management and enhancing security. This unified authentication model is a best practice in Linux administration news.
From Zero to Hero: Installing and Configuring Dovecot
Getting Dovecot up and running is straightforward on most Linux distributions. The real work lies in crafting a secure and efficient configuration tailored to your needs.
Installation on Popular Linux Distributions
Installation is handled by the system’s native package manager. For Debian-based systems like Ubuntu or Linux Mint, you’ll use apt. For RHEL-family systems like Fedora, CentOS Stream, or Rocky Linux, you’ll use dnf.
# For Debian/Ubuntu systems
sudo apt update
sudo apt install dovecot-core dovecot-imapd dovecot-pop3d
# For RHEL/Fedora/Rocky Linux systems
sudo dnf install dovecot
# Enable and start the service using systemd
sudo systemctl enable dovecot
sudo systemctl start dovecotUsing systemctl to manage the service is standard practice on any modern distribution that follows systemd news.
The First Configuration Steps
Dovecot’s configuration is typically located in /etc/dovecot/, with a main dovecot.conf file that includes smaller, more manageable files from the conf.d/ directory. It’s best practice to modify the specific files in conf.d/ rather than the main file.
The first and most important setting is defining the mail storage format and location. This is done in /etc/dovecot/conf.d/10-mail.conf. The industry standard is the Maildir format, which stores each email in a separate file. This is far more robust and performant than the older mbox format, which stores all emails in a single large file, making it prone to corruption.
# File: /etc/dovecot/conf.d/10-mail.conf
# mail_location specifies the mailbox location and format.
# maildir format is highly recommended.
# ~/Maildir tells Dovecot to create a Maildir directory in each user's home directory.
mail_location = maildir:~/Maildir
# Also, ensure the mail_privileged_group is set to 'mail' to allow
# Dovecot's delivery agent to write to user mailboxes.
mail_privileged_group = mailThis configuration tells Dovecot to look for a directory named Maildir inside the home directory of the authenticating user. This is a simple and effective setup for servers where email users correspond directly to system users.
Fortifying the Gates: SSL/TLS and Advanced Authentication
An unconfigured mail server is a security liability. The most critical steps after initial setup involve encrypting communications and creating a secure authentication pathway with Postfix. This is non-negotiable in modern Linux security news.
Implementing Encryption with SSL/TLS
Transmitting login credentials and email content over an unencrypted connection is unacceptable. Dovecot must be configured to use SSL/TLS encryption. The best way to obtain free, trusted SSL certificates is through Let’s Encrypt using the certbot tool.
Once you have your certificates (typically in /etc/letsencrypt/live/yourdomain.com/), you need to tell Dovecot where to find them in /etc/dovecot/conf.d/10-ssl.conf.
# File: /etc/dovecot/conf.d/10-ssl.conf
# Enable SSL/TLS. 'required' forces clients to use encryption.
ssl = required
# Path to your Let's Encrypt certificate and private key.
# Make sure the user dovecot can read these files.
ssl_cert = </etc/letsencrypt/live/mail.yourdomain.com/fullchain.pem
ssl_key = </etc/letsencrypt/live/mail.yourdomain.com/privkey.pem
# Set a minimum protocol version to avoid old, insecure protocols.
ssl_min_protocol = TLSv1.2
# A strong cipher list is also recommended for enhanced security.
ssl_cipher_list = EECDH+AESGCM:EDH+AESGCM:AES256+EECDH:AES256+EDHAfter applying these settings and restarting Dovecot, all IMAP/POP3 connections will be required to use TLS encryption, protecting user data in transit. This is a fundamental aspect of secure Linux networking news.
Configuring SASL for Postfix Integration
To achieve a single sign-on experience for users, we’ll configure Dovecot to provide a SASL authentication socket for Postfix. This allows a user to authenticate with their IMAP credentials when sending mail via SMTP.
First, we configure the authentication service listener in Dovecot’s /etc/dovecot/conf.d/10-master.conf.
# File: /etc/dovecot/conf.d/10-master.conf
# The 'auth' service is responsible for all authentication.
service auth {
# ... other settings
# Add a listener for Postfix's smtpd service.
# This path is inside Postfix's chroot jail.
unix_listener /var/spool/postfix/private/auth {
mode = 0660
# The user/group must match Postfix's user.
user = postfix
group = postfix
}
}Next, you would configure Postfix’s main.cf to use this socket. While this article focuses on Dovecot, the corresponding Postfix configuration would look like this:
smtpd_sasl_type = dovecot
smtpd_sasl_path = private/auth
smtpd_sasl_auth_enable = yes
This seamless integration is a prime example of the powerful modularity found in the Linux open source ecosystem.
Optimizing for Success: Best Practices and Performance
A running server is good, but a hardened, monitored, and optimized server is better. Following best practices ensures long-term stability and security.
Hardening Dovecot Security
Beyond SSL/TLS, several other settings contribute to a secure Dovecot instance:
- Disable Plaintext Authentication: In
/etc/dovecot/conf.d/10-auth.conf, setdisable_plaintext_auth = yes. This prevents passwords from ever being sent in clear text, even over an unencrypted connection (which should already be blocked byssl = required). - Use AppArmor or SELinux: Distributions like Ubuntu and Fedora ship with Mandatory Access Control systems. Using the default profiles for Dovecot adds a significant layer of defense, containing the process in case of a vulnerability. This is a key topic in Linux SELinux news.
- Keep Systems Updated: Regularly run system updates using
aptordnfto receive the latest security patches for Dovecot, the Linux kernel news, and all other system components.
Performance and Monitoring
Dovecot is highly performant out of the box, but for high-traffic servers, you can tune process limits in 10-master.conf. More importantly, effective monitoring is crucial for troubleshooting. On modern systems, logs are managed by journald, and the journalctl command is your best friend for Linux troubleshooting news.
# View the live, scrolling log for the dovecot service
sudo journalctl -u dovecot -f
# Show all dovecot logs from the current boot
sudo journalctl -u dovecot -b
# Filter logs for authentication failures
sudo journalctl -u dovecot | grep "auth: Error"Regularly checking these Linux logs news can help you spot brute-force attempts, configuration errors, and other potential issues before they become critical problems.
Virtual Users vs. System Users
Our guide has focused on using system users (accounts in /etc/passwd) for email. This is simple and effective for personal or small business servers. However, for hosting multiple domains or a large number of users, this becomes unmanageable and less secure. The advanced solution is to use “virtual users,” where user accounts are stored in a database like PostgreSQL Linux news or MySQL Linux news, completely separate from the underlying operating system. This is a more complex setup but offers far greater scalability and flexibility, making it a staple of professional Linux cloud news deployments.
Conclusion: Your Path to Email Sovereignty
We’ve journeyed through the core principles, installation, and secure configuration of Dovecot, the premier open-source IMAP and POP3 server. The key takeaways are clear: Dovecot is a powerful, flexible, and secure component of any modern email stack. Its strength lies not only in its own performance but in its seamless integration with Postfix for unified authentication. Prioritizing security through mandatory SSL/TLS encryption and following hardening best practices is not just recommended—it is essential.
By mastering Dovecot, you reclaim control over your digital communications, stepping away from third-party providers and building a mail service tailored to your needs. Your journey doesn’t end here. The next steps often involve integrating anti-spam and anti-virus solutions (like Rspamd or SpamAssassin), deploying a webmail client (like Roundcube), and exploring advanced topics like virtual user databases and high-availability clustering. The foundation you’ve built with a secure Postfix and Dovecot setup is the perfect launchpad for these future enhancements, solidifying your expertise in modern Linux administration news.



