Mastering Postfix: A Comprehensive Guide to Building Your Own Mail Server on Linux
Introduction to Building a Modern Mail Server
In an era dominated by cloud-based email providers, the idea of running your own mail server might seem like a relic of a bygone internet age. However, for developers, system administrators, and privacy advocates, managing a personal or business mail server offers unparalleled control, security, and a profound learning experience. At the heart of most self-hosted email solutions on Linux is Postfix, a powerful, secure, and highly flexible Mail Transfer Agent (MTA). This article serves as a comprehensive guide to understanding, installing, and configuring a robust Postfix mail server on modern Linux distributions like Ubuntu, Debian, or those in the Red Hat family, such as Fedora or Rocky Linux. We will explore the core components of the email ecosystem, walk through practical configuration steps, and delve into essential security practices like TLS encryption and SASL authentication. By the end, you’ll have the foundational knowledge to build a reliable mail server, taking a significant step towards digital sovereignty. This journey is a cornerstone of modern Linux administration news, demonstrating how classic tools remain vital in today’s infrastructure.
Section 1: Core Concepts of the Email Ecosystem and Postfix’s Role
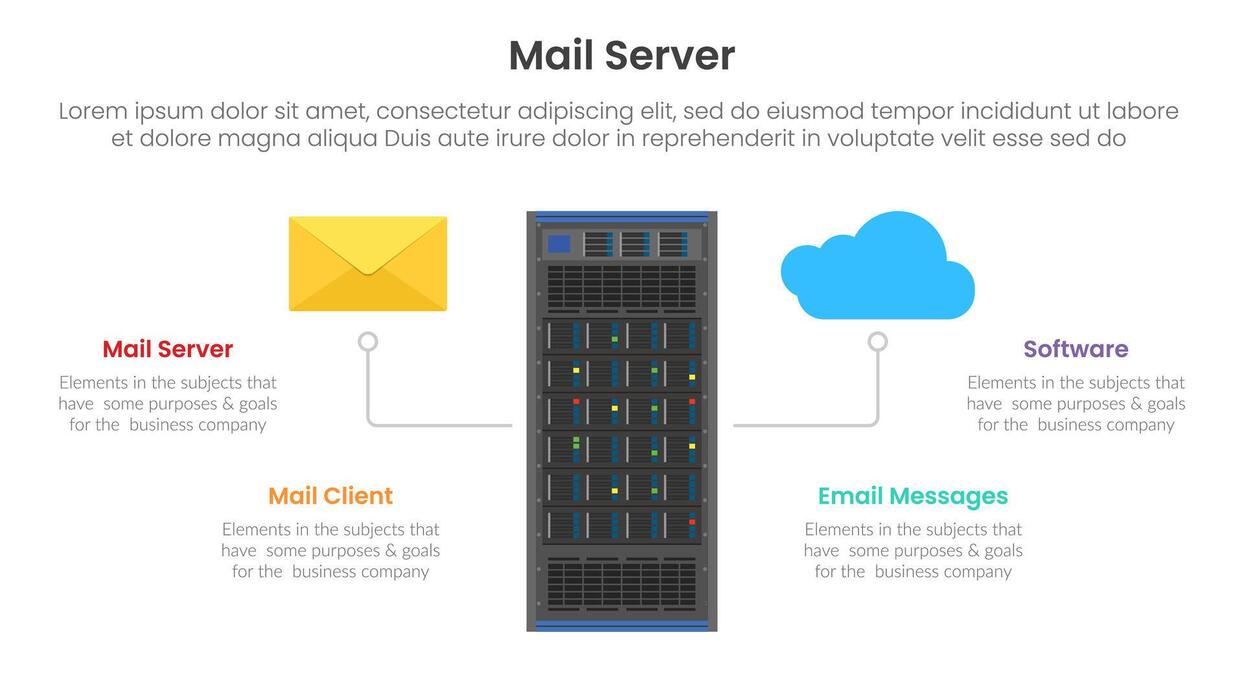
Before diving into configuration files and commands, it’s crucial to understand the architecture of email delivery and where Postfix fits in. A functional mail server is not a single application but a symphony of cooperating services, each with a specific role. Misunderstanding these roles is a common pitfall for newcomers.
The Key Components of a Mail Server
The email journey involves several distinct agents:
- Mail User Agent (MUA): This is the email client you interact with, such as Thunderbird, Microsoft Outlook, or a webmail interface. Its job is to compose, send, and display emails for the user.
- Mail Submission Agent (MSA): When you hit “send” in your MUA, the email is first sent to an MSA. The MSA, typically running on port 587, requires authentication and is the designated entry point for outgoing mail from authorized users.
- Mail Transfer Agent (MTA): This is the workhorse of the system. The MTA, like Postfix, receives email from an MSA or another MTA and is responsible for routing it across the internet to the recipient’s mail server. This process relies heavily on DNS MX (Mail Exchange) records.
- Mail Delivery Agent (MDA): Once an email arrives at its destination MTA, it’s handed off to an MDA. The MDA is responsible for placing the email into the correct user’s mailbox. Dovecot is a popular application that serves as both an MDA and an IMAP/POP3 server.
Postfix is a versatile tool that excels as an MTA and can also be configured to act as an MSA. For a complete solution, it’s almost always paired with an IMAP/POP3 server and MDA like Dovecot, a topic we’ll cover later. This modularity is a key feature discussed in Postfix news and is central to its secure design.
Initial Server Preparation and Firewall Configuration
A successful mail server deployment starts with a solid foundation. Your server must have a static IP address and a Fully Qualified Domain Name (FQDN). The server’s hostname should match the FQDN you will use for your email domain (e.g., mail.example.com). Furthermore, you must configure your firewall to allow traffic on the essential email ports. According to the latest Linux firewall news, using tools like ufw on Ubuntu/Debian or firewalld on Red Hat-based systems is standard practice. The key ports are 25 (SMTP for server-to-server transfer), 587 (SMTP submission with authentication), and 993 (IMAPS for retrieving mail).
# Set the hostname (replace mail.example.com with your FQDN)
sudo hostnamectl set-hostname mail.example.com
# On Ubuntu/Debian, open necessary ports with UFW
sudo ufw allow 25/tcp # SMTP
sudo ufw allow 587/tcp # Submission
sudo ufw allow 993/tcp # IMAPS
sudo ufw enable
sudo ufw status
# On CentOS/Rocky Linux, open ports with firewalld
sudo firewall-cmd --permanent --add-service=smtp
sudo firewall-cmd --permanent --add-port=587/tcp
sudo firewall-cmd --permanent --add-port=993/tcp
sudo firewall-cmd --reloadSection 2: Postfix Installation and Core Configuration
With the server prepared, we can proceed with installing and configuring Postfix. The installation process is straightforward across most Linux distributions, thanks to robust package managers, a constant highlight in Linux package managers news.
Installing Postfix on Major Linux Distributions
You can install Postfix using your distribution’s native package manager. During installation on Debian-based systems, you may be prompted with a configuration screen; select “Internet Site” and enter your FQDN when asked.
# On Debian, Ubuntu, Linux Mint, or Pop!_OS
sudo apt update
sudo apt install postfix
# On Fedora, CentOS, Rocky Linux, or AlmaLinux
sudo dnf install postfix
# On Arch Linux or Manjaro
sudo pacman -S postfixAfter installation, the primary configuration file you will work with is /etc/postfix/main.cf. This file contains hundreds of directives, but for a basic setup, you only need to focus on a few key parameters.
Understanding the `main.cf` Configuration File
The main.cf file is the nerve center of your Postfix installation. It’s crucial to understand the most important parameters to get your server running correctly. A misconfiguration here can lead to an open relay (a major security risk) or delivery failures.
myhostname: The FQDN of your mail server (e.g.,mail.example.com).mydomain: Your primary domain name (e.g.,example.com).myorigin: The domain name that locally posted mail appears to come from. By default, it’s set to$myhostname, but it’s often better to set it to$mydomain.mydestination: A list of domains that this server considers itself the final destination for. This is critical for telling Postfix which emails to accept and deliver locally.mynetworks: A list of trusted IP addresses or networks that are allowed to relay mail through your server without authentication. For a public-facing server, this should typically be restricted to localhost.inet_interfaces: Specifies the network interfaces on which Postfix should listen for incoming mail. Setting it toallis common for a public server.
Here is a practical example of a basic main.cf configuration. You can use a text editor like Vim news favorite, vim, or a more user-friendly one like nano to edit the file. Always back up the original file before making changes.
# /etc/postfix/main.cf - Basic Configuration Example
# See /usr/share/postfix/main.cf.dist for a full list of parameters
# The FQDN of your mail server
myhostname = mail.example.com
# The domain name
mydomain = example.com
# The domain for outgoing mail from local users
myorigin = $mydomain
# The domains this server will receive mail for
mydestination = $myhostname, localhost.$mydomain, localhost, $mydomain
# Networks allowed to relay mail (restrict to localhost for security)
mynetworks = 127.0.0.0/8 [::ffff:127.0.0.0]/104 [::1]/128
# The network interfaces Postfix will listen on
inet_interfaces = all
# Use maildir format for storing mail (recommended)
home_mailbox = Maildir/
# Set a mailbox size limit (0 = unlimited)
mailbox_size_limit = 0
# Set a message size limit (e.g., 25MB)
message_size_limit = 26214400
# After editing, always restart Postfix to apply changes
# sudo systemctl restart postfixSection 3: Securing Your Postfix Server with TLS and SASL
An unencrypted and unauthenticated mail server is a liability. In today’s internet landscape, encryption is not optional. This section covers enabling TLS for secure connections and SASL for user authentication, two pillars of modern Linux security news.
Implementing TLS for Encrypted Communication
Transport Layer Security (TLS) encrypts the communication between mail servers and between email clients and your server, preventing eavesdropping. The first step is to obtain an SSL/TLS certificate. The most popular and free method is using Let’s Encrypt with the Certbot client. Once you have your certificate files (typically fullchain.pem and privkey.pem), you can configure Postfix to use them.
The following directives in main.cf enable STARTTLS on port 587, which allows clients to upgrade a plain-text connection to an encrypted one, and enforce TLS for the submission port.
# /etc/postfix/main.cf - TLS Configuration
# Enable TLS for incoming connections (smtpd)
smtpd_use_tls = yes
smtpd_tls_cert_file = /etc/letsencrypt/live/mail.example.com/fullchain.pem
smtpd_tls_key_file = /etc/letsencrypt/live/mail.example.com/privkey.pem
smtpd_tls_security_level = may
smtpd_tls_protocols = !SSLv2, !SSLv3, !TLSv1, !TLSv1.1
smtpd_tls_loglevel = 1
# Enable TLS for outgoing connections (smtp)
smtp_use_tls = yes
smtp_tls_security_level = may
smtp_tls_loglevel = 1
# For the submission port (587), enforce TLS and authentication
# This requires editing the master.cf file as well.
# In /etc/postfix/master.cf, uncomment the submission inet service and add:
# -o smtpd_tls_security_level=encrypt
# -o smtpd_sasl_auth_enable=yesSetting Up SASL Authentication with Dovecot
To allow your users to send email from anywhere in the world, you must implement authentication. Sending email through a server you’re not the final destination for is called “relaying,” and it must be restricted to authenticated users only. Postfix can handle authentication itself, but the modern, recommended approach is to delegate it to Dovecot. This integration is a frequent topic in Dovecot news and creates a cleaner separation of concerns.
First, ensure Dovecot is installed (sudo apt install dovecot-core dovecot-imapd). Then, configure Dovecot to provide an authentication socket that Postfix can use. Finally, tell Postfix where to find this socket in main.cf.
# /etc/postfix/main.cf - SASL Authentication via Dovecot
# Enable SASL authentication for the SMTP daemon
smtpd_sasl_auth_enable = yes
# Specify the SASL implementation type
smtpd_sasl_type = dovecot
# Path to the Dovecot authentication socket
# This path must match what is configured in Dovecot's 10-master.conf
smtpd_sasl_path = private/auth
# Optional: Disallow anonymous logins
smtpd_sasl_security_options = noanonymous
# Reject mail from unauthenticated clients to domains we don't own
smtpd_relay_restrictions = permit_mynetworks, permit_sasl_authenticated, reject_unauth_destinationThis configuration tells Postfix to use Dovecot for all SASL authentication checks. When a user connects to port 587 and provides a username and password, Postfix will pass those credentials to Dovecot for verification. If successful, the user is allowed to relay mail.

Section 4: Anti-Spam Measures and Final Integrations
A mail server without anti-spam measures will quickly become overwhelmed and potentially blacklisted. Postfix provides a powerful framework of restrictions to filter out a significant amount of illegitimate traffic before it even enters your system.
Basic Anti-Spam and Security Hardening
Postfix processes incoming connections through a series of restriction classes. The most important one is smtpd_recipient_restrictions. By carefully ordering rules in this list, you can block a large percentage of spam and malicious connection attempts. A good starting point is to reject mail based on common misconfigurations and protocol violations that are hallmarks of spam bots.
The following example demonstrates a robust set of restrictions. The rules are processed in order, and the first one that matches (with a `permit` or `reject`) terminates the evaluation.
# /etc/postfix/main.cf - Anti-Spam Restrictions
smtpd_helo_required = yes
# A more robust restriction chain
smtpd_recipient_restrictions =
permit_mynetworks,
permit_sasl_authenticated,
reject_unauth_destination,
reject_invalid_helo_hostname,
reject_non_fqdn_helo_hostname,
reject_non_fqdn_sender,
reject_non_fqdn_recipient,
reject_unknown_sender_domain,
reject_unknown_recipient_domain,
reject_rbl_client zen.spamhaus.org,
reject_rbl_client bl.spamcop.net
# Optional: Enable Postscreen for pre-emptive spam blocking
# postscreen_dnsbl_threshold = 2
# postscreen_dnsbl_sites = zen.spamhaus.org*2 bl.spamcop.net*1
# postscreen_greet_action = enforceThis configuration first permits legitimate, authenticated users and local traffic. Then, it rejects connections based on a series of checks: invalid HELO/EHLO commands, non-fully-qualified hostnames, and finally, it checks the connecting IP against well-known Real-time Blackhole Lists (RBLs) like Spamhaus. For more advanced filtering, many administrators integrate tools like SpamAssassin. It is also critical to set up SPF, DKIM, and DMARC DNS records, which are essential for email authentication and improving your server’s deliverability, a constant theme in Linux DNS news.
Section 5: Best Practices, Monitoring, and Maintenance
Running a mail server is an ongoing responsibility. Proper monitoring and maintenance are key to ensuring reliability and security. This is a core tenet of any topic covered in Linux server news.
Logging and Monitoring
Postfix provides excellent logging. On systemd-based systems, you can monitor logs in real-time using `journalctl`.
- Check Logs:
sudo journalctl -u postfix -f - View the Mail Queue: The command
mailq(orpostqueue -p) shows all messages currently in the queue waiting for delivery. A large, stagnant queue is a sign of a problem. - Advanced Monitoring: For production environments, integrating with a monitoring stack like Prometheus and Grafana provides invaluable insight into mail volume, queue size, and server performance. This is a key aspect of modern Linux observability news.
Regular Maintenance and Automation
Keep your entire system, including Postfix and all related packages, up to date with your package manager (e.g., sudo apt upgrade). Regularly check your server’s IP address against public blacklists to ensure your reputation remains clean. For configuration, consider using automation tools. As highlighted in Ansible news, using a configuration management tool like Ansible, Puppet, or SaltStack allows you to define your Postfix setup in code, making it repeatable, version-controlled, and less prone to manual error. Finally, implement a robust backup strategy for /etc/postfix and your mail storage directory using tools like rsync news favorite, `rsync`, or more advanced solutions like BorgBackup.
Conclusion: Taking Control of Your Email Infrastructure
We have journeyed from the fundamental concepts of email delivery to the practical implementation of a secure and functional Postfix mail server. You have learned how to install Postfix, perform the initial critical configuration, secure communications with TLS, enforce user authentication with SASL, and implement foundational anti-spam measures. Building your own mail server is a challenging but immensely rewarding project that puts you in complete control of one of your most critical communication channels.
This guide provides a strong foundation, but the world of email administration is deep. From here, you can explore advanced topics such as setting up high-availability clusters with Pacemaker news, implementing DANE for enhanced TLS security, or fine-tuning performance for high-volume environments. By embracing the power and flexibility of open-source tools like Postfix on Linux, you gain not just a service, but a deep understanding of the internet’s essential infrastructure.



