
systemd HTTP Boot: Linux Deployment Guide
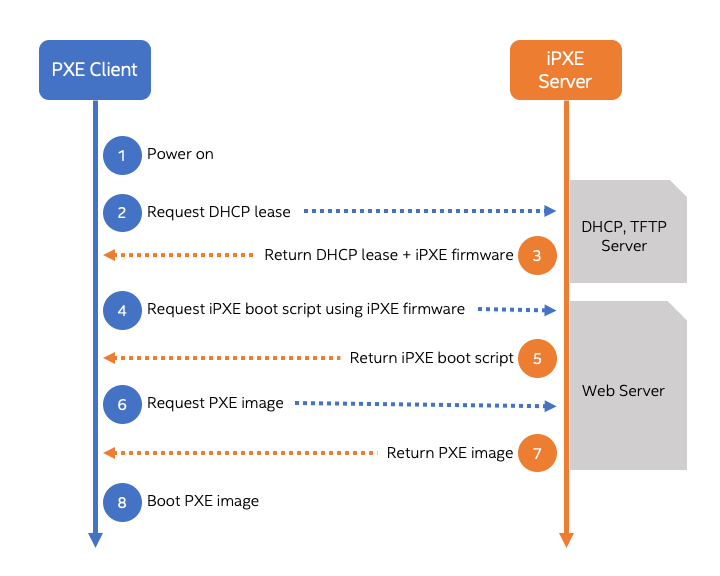
The Linux boot process has been a cornerstone of system administration for decades, evolving from simple BIOS and LILO setups to the sophisticated UEFI and GRUB configurations we use today. While network booting via PXE has long been the standard for large-scale, automated deployments, it often involves a complex stack of TFTP, DHCP, and NFS services. In a significant leap forward, the systemd project is introducing a paradigm-shifting capability: the ability to boot a full Linux system directly from a disk image served over a standard HTTP/HTTPS connection. This development promises to dramatically simplify infrastructure management, enhance security, and unlock new possibilities for stateless, ephemeral, and edge computing environments.
This article provides a comprehensive technical exploration of this groundbreaking feature. We will dissect the underlying components that make it possible, walk through practical implementation steps, explore advanced use cases, and discuss best practices for deploying this technology in the real world. This is a major piece of systemd news that will have a ripple effect across the entire ecosystem, from Fedora news and Arch Linux news, where it will likely land first, to enterprise distributions like those covered in Red Hat news and Ubuntu news.
The Architectural Foundations: UKIs and Dynamic Partitioning
Booting an entire operating system from a single remote file isn’t magic; it’s the culmination of several modern systemd components working in concert. Two technologies are particularly crucial to understanding this new boot method: Unified Kernel Images (UKIs) and the systemd-repart service.
What is a Unified Kernel Image (UKI)?
A Unified Kernel Image is a single, self-contained, and bootable EFI executable file. Instead of having separate files for the Linux kernel, the initramfs (initial RAM filesystem), and the kernel command line, a UKI bundles them all together. This approach offers several key advantages:
- Simplicity: A single file is easier to manage, version, and distribute than a collection of separate components.
- Security: Because it’s a single EFI binary, a UKI can be signed using UEFI Secure Boot keys. This creates a verifiable chain of trust from the firmware to the kernel, a critical aspect of modern Linux security news.
- Portability: The image is self-describing, containing everything needed to start the early boot process, making it highly portable across different machines.
Tools like dracut and mkinitcpio, often discussed in Linux kernel news, are being updated to streamline the creation of these UKIs, which form the initial payload that fetches and boots the main disk image.
The Role of systemd-repart
Once the system boots, how does a generic, small disk image adapt to the underlying storage of the machine? This is where systemd-repart comes in. It’s a powerful service that runs in the early boot phase (within the initrd) and can automatically discover and grow filesystems. It operates based on a declarative model, reading configuration files that define the desired partition layout.
For instance, systemd-repart can be configured to create a root partition, a home partition, and a swap partition, and then automatically grow the root partition to fill all remaining unallocated space on the disk. This is the mechanism that allows a single, compact base image to be deployed across servers with vastly different disk sizes, a common scenario in Linux cloud environments on AWS, Azure, or Google Cloud.
Here is an example of a configuration file for systemd-repart, which would typically be placed in /etc/repart.d/.

# /etc/repart.d/10-basic-layout.conf
#
# Defines a basic partition layout for systemd-repart.
# This will create a 512M EFI partition, a 1G boot partition,
# and a root partition that fills the rest of the disk.
[Partition]
Type=esp
SizeMin=512M
SizeMax=512M
Format=fat32
[Partition]
Type=xbootldr
SizeMin=1G
SizeMax=1G
Format=ext4
[Partition]
Type=root
Format=btrfs
CopyBlocks=/path/to/seed/rootfs.img
Grow=trueIn this configuration, the Grow=true directive on the root partition is the key instruction for systemd-repart to expand the filesystem, making the downloaded image fully utilize the available hardware.
The Core Mechanism: Booting from an HTTP URL
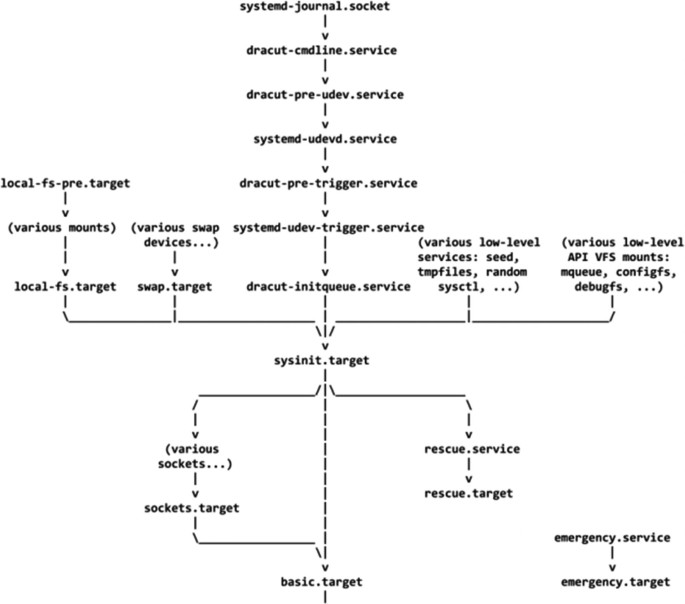
With the foundational components in place, the actual HTTP boot process is a logical sequence of events orchestrated by systemd within the initrd. This process elegantly sidesteps the complexity of traditional PXE environments.
From UEFI to a Running System: The Boot Flow
The journey from powering on the machine to a fully booted OS follows these steps:
- Bootloader Configuration: A UEFI bootloader, such as systemd-boot, is configured with a new entry. This entry points to a specialized UKI designed for network booting.
- Kernel Command Line: The crucial instruction is passed via the kernel command line. A new parameter,
systemd.image_url=, tells the initrd where to find the target disk image. - Network Initialization: The UKI’s initrd contains the necessary userspace tools, like
systemd-networkdandsystemd-resolved, to bring up the network interface, acquire an IP address via DHCP, and resolve DNS. This is a core part of modern Linux networking news. - Image Download and Attachment: The system downloads the disk image specified in the URL. This image can be a raw disk image (`.raw`), a compressed image (`.raw.xz`), or another supported format. It is then attached to a loopback device or, more powerfully, written directly to a target block device like
/dev/sda. - Partitioning and Mounting: If writing to a block device,
systemd-repartmay run to partition the disk as described earlier. The system then identifies and mounts the new root filesystem. - Switching Root: Finally, the boot process executes a
switch_rootoperation, pivoting from the temporary initrd environment into the newly downloaded and mounted root filesystem. The machine now continues its boot process as if it had started from a local disk.
To make this work, you need a simple web server to host the image. Here is a minimal Nginx configuration for this purpose.
server {
listen 80;
server_name images.example.com;
root /srv/www/images;
location / {
autoindex on; # Useful for browsing
try_files $uri $uri/ =404;
}
}On the client side, the systemd-boot entry in /boot/efi/loader/entries/netboot.conf would look something like this:
# /boot/efi/loader/entries/netboot.conf
title Boot Latest Fedora from HTTP
efi /EFI/Linux/netboot-uki.efi
options systemd.image_url=http://images.example.com/fedora-39-server.raw.xz systemd.image_block_device=/dev/sdaThis configuration tells the system to boot using the `netboot-uki.efi` image and instructs it to download the Fedora disk image and write it to the primary disk ` /dev/sda`.
Advanced Use Cases and Security Implications
The ability to boot from an HTTP source opens up a wealth of possibilities beyond simple OS installation, particularly in automated and security-conscious environments.
Dynamic and Stateless Environments
This feature is a game-changer for Linux DevOps and orchestration platforms like Kubernetes or Nomad. You can now treat worker nodes as truly stateless cattle. Every time a node boots, it can pull a pristine, known-good, and immutable OS image. This eliminates configuration drift and simplifies cluster management. If a node becomes compromised or unstable, a simple reboot restores it to a clean state. This is highly relevant for Linux server news, especially in the context of large-scale cloud and edge deployments, from AWS Linux news to Raspberry Pi Linux news for IoT fleets.
Integrating with Verity and `systemd-homed`
Security is paramount, and downloading an OS over the network raises valid concerns. This is where integration with other systemd and Linux kernel features becomes critical.
- dm-verity: The disk image on the server can be cryptographically signed. The hash of the image can be embedded within the UKI. The initrd can then use the `dm-verity` kernel target to verify the integrity of every single block read from the disk image as it’s being used. Any tampering with the image on the server or in transit will cause the verification to fail, halting the boot process. This provides a powerful defense against supply chain attacks.
- systemd-homed: By booting a stateless base OS, user data can be kept entirely separate.
systemd-homedallows portable, encrypted home directories to be stored on a central NFS or iSCSI server and mounted on demand at login. This combination creates a secure system where the OS is immutable and verifiable, while user data remains persistent and protected. This is a significant update for anyone following Linux encryption news and tools like LUKS.
For automated provisioning, the image URL doesn’t have to be static. It can be provided dynamically by a DHCP server, allowing different machines to boot different images based on their network segment or MAC address.
# Example dnsmasq.conf snippet for dynamic image URLs
#
# This uses a custom DHCP option (224) to pass the URL.
# The client's initrd must be configured to read this option.
dhcp-option=224, "http://images.example.com/stable/workstation.raw"
# Assign a different image based on MAC address
dhcp-host=11:22:33:44:55:66, set:k8s-node
dhcp-option-force=tag:k8s-node, 224, "http://images.example.com/k8s/v1.28.raw"Best Practices and Performance Considerations
While this technology is powerful, deploying it effectively requires careful planning. Here are some key considerations and best practices.
Managing Network Dependency and Image Lifecycles
The most significant pitfall is the hard dependency on the network. If the HTTP server is unreachable, the machine will not boot. For critical systems, consider implementing redundant web servers with a load balancer like HAProxy or using a local caching proxy. Furthermore, image management is crucial. Adopt a strict versioning scheme for your images (e.g., `image-v1.2.3.raw`) and use a CI/CD pipeline (GitLab CI, GitHub Actions) to build, test, and sign them automatically. This creates a repeatable and auditable process for OS updates.
Performance Tuning and Image Optimization
Boot time will be directly affected by the image size and network speed. To optimize performance:
- Keep Images Small: Build minimal base images containing only the necessary services. Avoid including large development tools or GUI components (like GNOME or KDE Plasma) in server images.
- Use Compression: Serving a compressed image (e.g., with `xz` or `zstd`) significantly reduces transfer time. The initrd can decompress it on the fly.
- Create Sparse Images: A sparse image only stores allocated blocks, making the file much smaller if the filesystem is mostly empty. This is ideal for base images that will be expanded by
systemd-repart.
Here’s a simple shell script demonstrating how to create a sparse image, a common task in Linux administration.
#!/bin/bash
set -euo pipefail
IMAGE_FILE="sparse-root.raw"
IMAGE_SIZE="10G"
MOUNT_POINT="/mnt/tmp_root"
# Create a sparse file of 10GB
fallocate -l ${IMAGE_SIZE} ${IMAGE_FILE}
# Create an ext4 filesystem on it
mkfs.ext4 -F ${IMAGE_FILE}
# Mount, populate, and unmount
mkdir -p ${MOUNT_POINT}
mount -o loop ${IMAGE_FILE} ${MOUNT_POINT}
# ... copy your root filesystem contents here ...
# For example, using dnf/debootstrap or an existing tarball
umount ${MOUNT_POINT}
rmdir ${MOUNT_POINT}
echo "Sparse image created at ${IMAGE_FILE}"
ls -lh ${IMAGE_FILE}Conclusion: A New Era for Linux System Management
Systemd’s introduction of booting from HTTP-served disk images is more than just an incremental improvement; it represents a fundamental shift in how we can provision and manage Linux systems. By leveraging the simplicity and ubiquity of HTTP and combining it with powerful, modern components like UKIs, systemd-repart, and `dm-verity`, this feature streamlines deployments, enhances security, and enables truly immutable infrastructure.
The implications are vast, touching everything from large-scale Linux server farms and Kubernetes clusters to embedded IoT devices and even dynamic desktop environments. As this feature matures and finds its way into major distributions from Debian to openSUSE, system administrators and DevOps engineers will gain a powerful new tool in their arsenal. The future of Linux deployment is looking simpler, more secure, and incredibly flexible.



