
Securing Your CI/CD Pipeline: A Deep Dive into the Critical Jenkins Arbitrary File Read Vulnerability on Linux
Introduction: The Unseen Threat in Your DevOps Workflow
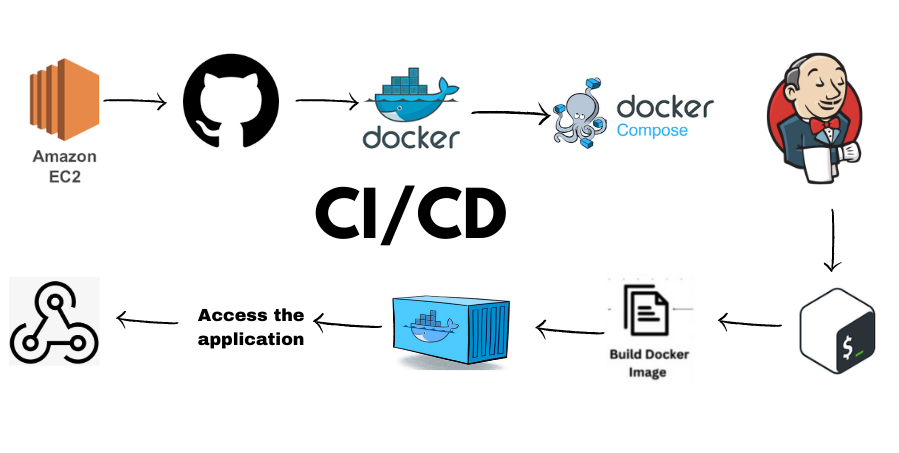
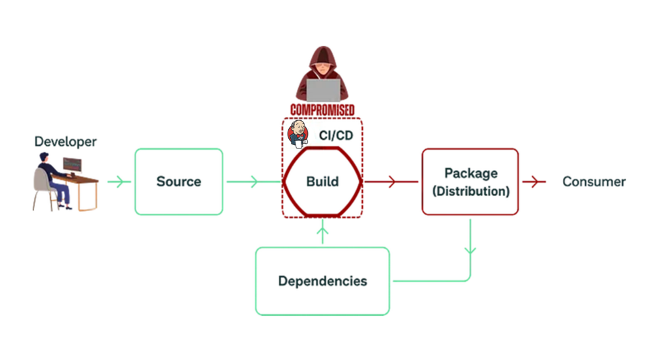
In the world of modern software development, Jenkins stands as a titan of automation. As the leading open-source automation server, it powers countless CI/CD pipelines, enabling teams to build, test, and deploy software with unprecedented speed and efficiency. The vast majority of these powerful servers run on Linux, leveraging the stability and flexibility of distributions like Ubuntu, Debian, Red Hat, and CentOS. This deep integration into the development lifecycle makes Jenkins a high-value target for malicious actors. When a critical vulnerability surfaces, it’s not just a server at risk; it’s the entire software supply chain.
Recently, the cybersecurity community has been buzzing with news of a critical vulnerability affecting the core of Jenkins. This flaw, identified as CVE-2024-23897, allows unauthenticated attackers to read arbitrary files from the Jenkins controller’s filesystem. This is a significant piece of Linux security news, as it can lead to the exposure of sensitive data—from SSH keys and API tokens to proprietary source code. In certain configurations, this file read capability can be chained with other techniques to achieve full Remote Code Execution (RCE), giving an attacker complete control over the CI/CD environment. This article provides a comprehensive technical breakdown of this vulnerability, offering practical steps for detection, mitigation, and long-term hardening of your Jenkins instances on Linux.
Understanding the Threat: The Jenkins Arbitrary File Read Vulnerability
At its core, CVE-2024-23897 is a path traversal vulnerability rooted in the way Jenkins processes command-line interface (CLI) arguments. The flaw exists within the args4j library used by Jenkins to parse command arguments. This issue affects Jenkins versions up to 2.441 and LTS (Long-Term Support) versions up to 2.426.2, making a vast number of deployments across the globe susceptible.
How the Attack Works on a Linux System
The vulnerability is triggered by a feature in the command parser that expands an argument prefixed with the “@” character. Normally, this feature is intended to load arguments from a file, simplifying complex CLI commands. However, the parser fails to properly sanitize the file path, allowing an attacker to specify any file on the Jenkins controller’s filesystem. An unauthenticated attacker can send a crafted request to the Jenkins CLI endpoint, which is often exposed over the internet, and trick the server into returning the contents of a sensitive file.
On a typical Linux server, the impact is immediate and severe. Attackers can target well-known file locations to gather critical information. For example, they could read /etc/passwd to enumerate users, /var/lib/jenkins/secrets/initialAdminPassword to gain administrative access, or even attempt to read private SSH keys from /var/lib/jenkins/.ssh/id_rsa. This makes it a critical piece of Linux server news for any administrator.
Here is a conceptual example of what an attack might look like using a simple curl command. This command sends a request to the Jenkins CLI endpoint, asking for help on a command, but injects the malicious file read argument.
# Conceptual attack to read the /etc/passwd file from a vulnerable Jenkins server
# This sends a POST request to the CLI endpoint with a crafted argument.
# The "@" symbol followed by the file path triggers the vulnerability.
curl -s -X POST "https://your-jenkins-instance.com/cli?remoting=false" \
-H "Content-Type: application/x-www-form-urlencoded" \
-H "Session: jenkins=none" \
-H "Side: download" \
-d "script=connect-node '@/etc/passwd'"If the server is vulnerable, the response will not be the help text for the `connect-node` command but will instead contain the full contents of the /etc/passwd file from the underlying Linux host.
Are You Vulnerable? Detection and First-Response Mitigation
The first step in securing your infrastructure is to determine if you are affected. This involves checking your Jenkins version and scanning for any signs that the vulnerability may have already been exploited.
Identifying Vulnerable Jenkins Versions
The most direct way to check for vulnerability is to identify your Jenkins version. You can find this information in the bottom-right corner of the Jenkins web UI. For administrators working in a terminal, a simple command can retrieve the version from the Jenkins WAR file or environment variables, a crucial skill in Linux administration.
# Check the Jenkins version from the command line on a Debian/Ubuntu system
# This command unzips the manifest from the WAR file and greps for the version number.
JENKINS_WAR="/usr/share/java/jenkins.war"
if [ -f "$JENKINS_WAR" ]; then
unzip -p "$JENKINS_WAR" META-INF/MANIFEST.MF | grep "Jenkins-Version"
else
echo "Jenkins WAR file not found at $JENKINS_WAR. Please check your installation path."
fi
# Alternatively, for RPM-based systems like CentOS or Fedora:
# rpm -q jenkinsIf your version is 2.441 or earlier, or 2.426.2 or earlier for LTS, you are vulnerable and must take immediate action.
Scanning Logs for Indicators of Compromise (IoC)
Before patching, it’s wise to check if you’ve already been targeted. Attackers often leave traces in server access logs. You should search your web server logs (e.g., Nginx, Apache) or Jenkins’ own logs for requests to the /cli endpoint that contain suspicious patterns, particularly the @ character. This is where knowledge of Linux commands news and tools like grep and journalctl becomes invaluable.
# Search Nginx access logs for suspicious CLI requests
# This command looks for POST requests to the /cli endpoint containing the "@" character.
sudo grep "POST /cli" /var/log/nginx/access.log | grep "@"
# For systems using systemd, you can search the Jenkins journal
# This requires Jenkins to be configured to log to journald.
sudo journalctl -u jenkins.service | grep "/cli" | grep "@"Immediate Mitigation: Disable the CLI
If you cannot upgrade immediately, the most effective short-term mitigation is to disable the Jenkins CLI HTTP endpoint. This completely closes the attack vector. This can be done in the Jenkins UI under Manage Jenkins → Security. Uncheck the box for “CLI over HTTP / Remoting”. While this is a powerful temporary fix, the ultimate solution is to upgrade the Jenkins instance.
Beyond the Patch: Hardening Your Linux-Based Jenkins Environment
Patching is essential, but true security comes from a defense-in-depth strategy. Use this vulnerability as an opportunity to harden your entire CI/CD infrastructure, a core principle of modern Linux DevOps.
The Primary Solution: Upgrading Jenkins
The definitive fix is to upgrade to a patched version: Jenkins 2.442 or LTS 2.426.3 and later. These versions contain a backported fix to the args4j library that disables the problematic “@” expansion feature by default. The upgrade process on Linux is typically straightforward using the system’s package manager.
# --- Upgrade Jenkins on Debian/Ubuntu ---
# First, update the package list
sudo apt-get update
# Then, install the latest version of Jenkins
sudo apt-get install --only-upgrade jenkins
# --- Upgrade Jenkins on Red Hat/CentOS/Fedora ---
# First, update the repository information
sudo dnf check-update || sudo yum check-update
# Then, upgrade the jenkins package
sudo dnf upgrade jenkins || sudo yum upgrade jenkinsThis simple act of keeping software updated is one of the most effective security measures an administrator can take, reflecting the latest in apt news and dnf news.
Automating Security with Ansible
Manual updates can be forgotten. To ensure consistent security posture across multiple servers, use a configuration management tool like Ansible. An Ansible playbook can enforce that all your Jenkins instances are running a patched version and that insecure configurations are disabled. This is a prime example of leveraging Linux automation for enhanced security.
---
- name: Harden Jenkins Server
hosts: jenkins_servers
become: yes
tasks:
- name: Ensure Jenkins is updated to the latest version (Debian/Ubuntu)
apt:
name: jenkins
state: latest
update_cache: yes
when: ansible_os_family == "Debian"
- name: Ensure Jenkins is updated to the latest version (RedHat/CentOS)
dnf:
name: jenkins
state: latest
update_cache: yes
when: ansible_os_family == "RedHat"
- name: Ensure Jenkins CLI over HTTP is disabled as a precaution
# This task would typically involve modifying Jenkins' config.xml
# or using the Jenkins API/CLI to apply the change.
# For simplicity, we'll represent it with a shell command.
# NOTE: A more robust solution would use the Jenkins API.
shell: |
# This is a conceptual command. Actual implementation may vary.
java -jar /var/cache/jenkins/war/WEB-INF/jenkins-cli.jar -s http://localhost:8080/ groovy = <<'EOF'
import jenkins.model.Jenkins
def jenkins = Jenkins.get()
if (jenkins.getMarkupFormatter() != null) {
jenkins.getSecurityRealm().setAllowsCli(false)
jenkins.save()
}
EOF
notify: Restart JenkinsThis playbook, a key part of Ansible news and best practices, ensures your infrastructure remains compliant and secure automatically.
Building a Resilient CI/CD Pipeline: Best Practices
A single vulnerability should prompt a broader review of your security practices. To build a truly resilient system, consider the following measures.
Network Segmentation and Firewalls
Your Jenkins controller should not be openly exposed to the internet. Place it behind a reverse proxy like Nginx and a properly configured firewall. Use tools like nftables or iptables to restrict access to the Jenkins ports, allowing traffic only from trusted IP ranges, such as a corporate VPN. This is fundamental Linux networking news and a critical security layer.

Principle of Least Privilege and Containerization
Run the Jenkins process as a dedicated, non-privileged user (e.g., `jenkins`). This user should have minimal permissions on the filesystem, limiting the blast radius of a file read vulnerability. For even greater isolation, run Jenkins inside a container using Docker or Podman. This is a major trend in Docker Linux news. Containerization abstracts the host filesystem and allows you to define strict resource limits, making it much harder for an attacker to break out and compromise the host system.
Secure Secrets Management
Avoid storing secrets directly on the Jenkins controller's filesystem. A file read vulnerability could expose them all. Instead, integrate Jenkins with a dedicated secrets management solution like HashiCorp Vault, AWS Secrets Manager, or Azure Key Vault. The Jenkins Credentials plugin has excellent support for these tools, allowing you to fetch secrets dynamically at build time without ever storing them on disk.
Conclusion: From Reactive Patching to Proactive Security
The Jenkins arbitrary file read vulnerability (CVE-2024-23897) serves as a powerful reminder that no component in the software supply chain is immune to threats. For organizations relying on Linux to power their CI/CD pipelines, this event underscores the need for constant vigilance and a multi-layered security approach. The key takeaways are clear: immediate patching is non-negotiable, but it is only the first step.
True resilience is built on a foundation of proactive security practices. This includes automating updates with tools like Ansible, leveraging containerization for isolation, implementing strict network controls, and managing secrets securely. By adopting a defense-in-depth strategy, you transform your response from a reactive scramble to a robust, ongoing process. Audit your Jenkins instances today, apply the necessary patches, and use this opportunity to fortify your entire DevOps infrastructure for the challenges of tomorrow.



