
The New Frontier: How the Linux Foundation is Championing Decentralized Trust and Open-Source Smart Contracts
For decades, the Linux Foundation has served as the bedrock of the open-source world, stewarding the Linux kernel and fostering collaborative development for critical technologies like Kubernetes, Node.js, and Let’s Encrypt. Now, this pivotal organization is expanding its focus to a new and transformative frontier: decentralized trust. By embracing privacy-centric technologies and fostering the open-sourcing of next-generation smart contract languages, the Linux Foundation is signaling a major shift in how we approach digital identity, data privacy, and secure transactions. This initiative isn’t just about adopting new technologies; it’s about applying the proven principles of open-source collaboration to solve some of the most pressing challenges of our digital age.
The convergence of the robust, battle-tested Linux ecosystem with the innovative world of decentralized systems creates a powerful synergy. The same tools and practices that power the world’s cloud infrastructure—from containerization and orchestration to automated configuration management—are now being leveraged to build a more secure, transparent, and user-centric internet. This article explores this exciting development, diving into the core concepts of decentralized trust, demonstrating how to build and manage these systems on a Linux foundation, and outlining the best practices for security and performance in this new paradigm.
Understanding Decentralized Trust and Privacy-Centric Smart Contracts
Smart contract code on screen – Fake VS Code Extension on npm Uses Altered ScreenConnect Utility …
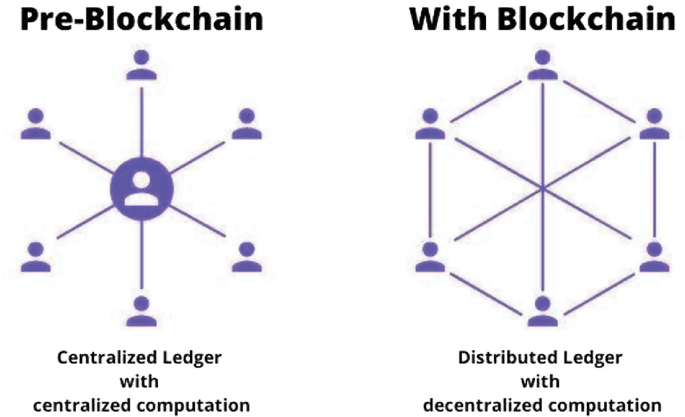
At its core, the push towards decentralized trust is about shifting control of data and identity away from centralized silos and back to the individual. It’s a movement built on open standards and cryptographic proof rather than blind faith in a single corporate entity. This philosophy aligns perfectly with the ethos of the open-source community and the technical foundation provided by Linux distributions like Debian, Fedora, and Ubuntu.
The Role of Smart Contracts in a Trustless World
Smart contracts are self-executing contracts with the terms of the agreement directly written into code. They run on decentralized networks, and their execution is automated and typically irreversible. While they form the backbone of many decentralized applications, traditional smart contracts on public blockchains often suffer from a major drawback: a lack of privacy. All data and transaction logic are public, which is unsuitable for countless real-world applications, from corporate finance to personal healthcare.

Introducing Privacy-Preserving Languages
To address this privacy gap, a new generation of smart contract languages is emerging. These languages are designed from the ground up with privacy, security, and performance in mind. They often incorporate advanced cryptographic techniques like Zero-Knowledge Proofs (ZKPs), allowing a transaction to be verified without revealing the underlying data. Languages like Rust are becoming increasingly popular for building these systems due to their strong safety guarantees.
Rust’s focus on memory safety (preventing entire classes of bugs like buffer overflows) and its powerful type system make it an ideal choice for writing the kind of mission-critical code required for smart contracts. Its ownership model ensures at compile time that there are no data races, which is crucial in concurrent environments. This focus on compile-time verification significantly reduces the risk of runtime errors that could be catastrophic in a financial system.
Here’s a conceptual example in Rust showing how one might define a shielded transaction, emphasizing the use of strong types for security.
// A conceptual example of a shielded transaction struct in Rust.
// This demonstrates Rust's strong typing and data ownership principles.
// Represents an encrypted note or amount. In a real system, this would
// be a complex cryptographic object.
pub struct ShieldedData(Vec<u8>);
// Represents a cryptographic commitment to a transaction's validity.
pub struct ZeroKnowledgeProof(Vec<u8>);
// The main transaction structure.
// All sensitive data is encrypted or represented by a proof.
pub struct ShieldedTransaction {
source_commitment: ShieldedData,
destination_note: ShieldedData,
fee: u64, // The fee can be public
proof: ZeroKnowledgeProof,
}
impl ShieldedTransaction {
// A constructor function to create a new shielded transaction.
// The actual logic would involve complex cryptographic operations.
pub fn new(
source: ShieldedData,
destination: ShieldedData,
fee: u64,
proof: ZeroKnowledgeProof,
) -> Self {
println!("Creating a new shielded transaction...");
ShieldedTransaction {
source_commitment: source,
destination_note: destination,
fee,
proof,
}
}
// A method to verify the transaction using its proof.
// This would be called by nodes on the network.
pub fn verify(&self) -> bool {
// In a real implementation, this would involve verifying the
// ZeroKnowledgeProof against the public parts of the transaction.
println!("Verifying transaction proof...");
// For demonstration, we'll assume the proof is valid if it's not empty.
!self.proof.0.is_empty()
}
}
fn main() {
// This is a mock-up of creating and verifying a transaction.
let tx = ShieldedTransaction::new(
ShieldedData(vec



