
Unlocking Network Automation: A Deep Dive into Red Hat Ansible and Cisco Meraki Integration
The New Imperative: Automating the Modern Network
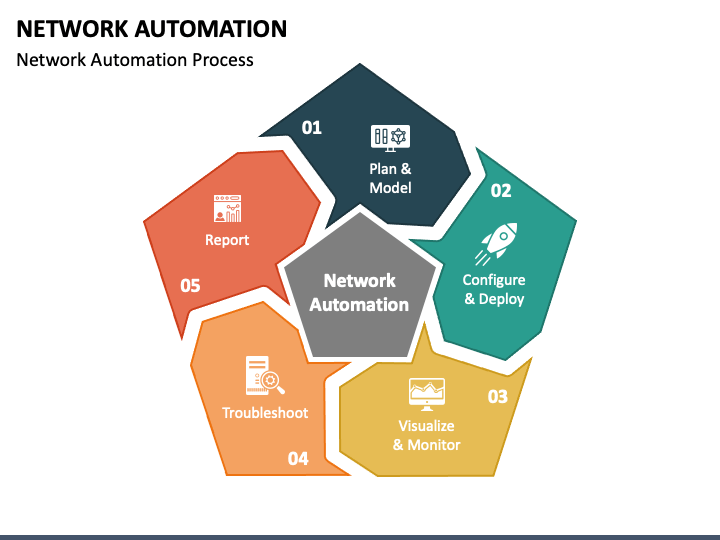
In today’s fast-paced digital landscape, the demands on network infrastructure are more intense than ever. Businesses require agility, scalability, and unwavering reliability, yet traditional network management—characterized by manual command-line interface (CLI) configurations and complex, device-by-device changes—is a significant bottleneck. This manual approach is not only slow and prone to human error but also fails to scale with the dynamic needs of modern applications and cloud environments. The solution lies in embracing Infrastructure as Code (IaC) and automation, a paradigm shift that is dominating recent Red Hat news and the broader Linux DevOps community.
At the forefront of this revolution are two powerful technologies: Red Hat Ansible Automation Platform and Cisco Meraki. Ansible, a cornerstone of modern Linux administration, provides a simple, agentless, and powerful engine for automating everything from servers to cloud services and, crucially, network devices. Cisco Meraki has redefined networking with its cloud-managed, API-first architecture, making complex networks accessible and manageable from a single dashboard. This article explores the powerful synergy between these two platforms, providing a comprehensive guide on how to unify and automate network management for unprecedented efficiency and control.
Understanding the Synergy: Why Ansible and Meraki?
The combination of Ansible and Meraki is a natural fit, bridging the gap between declarative automation and cloud-native networking. By leveraging Ansible’s robust ecosystem with Meraki’s comprehensive API, organizations can transform their network operations from a reactive, manual process into a proactive, automated, and version-controlled system.
Red Hat Ansible: The Automation Engine
Ansible’s power lies in its simplicity and agentless design. It communicates over standard protocols like SSH (for a typical Linux server) or, in this case, HTTPS for API interactions. Its human-readable YAML syntax makes automation accessible to network engineers, system administrators, and developers alike. Key concepts include:
- Playbooks: YAML files that define a set of tasks to be executed in a specific order.
- Modules: Reusable units of code that perform specific tasks, such as creating a VLAN, configuring a firewall rule, or updating an SSID. The `cisco.meraki` collection provides a rich set of modules specifically for this purpose.
- Inventory: A file that defines the hosts and devices Ansible will manage. This can be a static file or, more powerfully, a dynamic script that pulls data directly from a source like the Meraki Dashboard.
This approach is central to the latest trends in Linux configuration management and is a frequent topic in discussions around Ansible news.
Cisco Meraki: Cloud-Managed Networking
Cisco Meraki’s platform abstracts away the complexity of underlying network hardware. Every switch, access point, and security appliance is managed through the central Meraki Dashboard. Crucially, every action available in the dashboard is also exposed via a well-documented RESTful API. This API is the key that unlocks programmatic control, allowing tools like Ansible to perform any management task that a human administrator could.
Setting Up Your Automation Environment
Before you can start automating, you need a control node. This is typically a Linux machine running a distribution like Fedora, Rocky Linux, or Ubuntu. The setup is straightforward:
- Install Ansible: Use Python’s package manager, pip.
python3 -m pip install ansible - Install the Meraki Collection: Ansible Collections are the standard way to distribute content.
ansible-galaxy collection install cisco.meraki - Configure API Access: Generate an API key from the Meraki Dashboard and export it as an environment variable for security. Avoid hardcoding keys in your playbooks.
Here is a simple shell script snippet for setting up your environment variables. This is a fundamental practice in Linux shell scripting.
#!/bin/bash
# Best practice: Store your Meraki API key securely.
# For this example, we'll export it as an environment variable.
# In production, use a secrets manager like Ansible Vault or HashiCorp Vault.
export MERAKI_DASHBOARD_API_KEY="YOUR_API_KEY_HERE"
echo "Meraki API key has been set as an environment variable for this session."
echo "You can now run your Ansible playbooks."From Manual Clicks to Automated Playbooks
With the environment ready, we can move from theory to practice. The best way to start is with read-only operations to verify connectivity and understand the data structure. This aligns with best practices discussed in Linux security news, emphasizing a cautious, iterative approach.
Gathering Network Information (Read-Only Operations)
A fundamental first step is to query the Meraki API for information about your infrastructure. This playbook uses the `meraki_organization_info` module to fetch details about your organizations and the `debug` module to print the output. It’s a simple, safe way to test your setup.
---
- name: Gather Meraki Organization and Network Information
hosts: localhost
connection: local
gather_facts: no
collections:
- cisco.meraki
tasks:
- name: Get organization information
meraki_organization_info:
state: query
register: my_orgs
- name: Display organization details
ansible.builtin.debug:
msg: "Found Organization '{{ item.name }}' with ID '{{ item.id }}'"
loop: "{{ my_orgs.meraki_payload }}"
- name: Get network information for the first organization
meraki_network_info:
state: query
org_id: "{{ my_orgs.meraki_payload[0].id }}"
register: my_networks
- name: Display network details
ansible.builtin.debug:
msg: "Found Network '{{ item.name }}' with ID '{{ item.id }}'"
loop: "{{ my_networks.meraki_payload }}"Running this playbook provides immediate, structured data about your environment, which can be used for reporting, auditing, or as input for subsequent automation tasks. This simple act of data gathering is a cornerstone of modern Linux monitoring and observability.
Configuring a Wireless SSID
Let’s move to a common write operation: creating or updating a wireless network (SSID). This task is often repetitive and error-prone when done manually across multiple sites. With Ansible, we can define the desired state in a playbook and apply it consistently everywhere. This playbook uses the `meraki_ssid` module to configure an SSID with WPA2-PSK authentication and assign it to a specific VLAN.
---
- name: Configure Corporate Wireless SSID
hosts: localhost
connection: local
gather_facts: no
vars:
meraki_org_name: "Your-Org-Name"
meraki_net_name: "Your-Network-Name"
ssid_name: "Corporate-WiFi"
ssid_psk: "S3cureP@ssw0rd!" # Use Ansible Vault for this in production!
collections:
- cisco.meraki
tasks:
- name: Find the target organization ID
meraki_organization_info:
state: query
name: "{{ meraki_org_name }}"
register: org_info
- name: Find the target network ID
meraki_network_info:
state: query
org_id: "{{ org_info.meraki_payload[0].id }}"
name: "{{ meraki_net_name }}"
register: net_info
- name: Create or Update the Corporate SSID
meraki_ssid:
state: present
net_id: "{{ net_info.meraki_payload[0].id }}"
number: 2 # SSID number (0-14)
name: "{{ ssid_name }}"
enabled: true
auth_mode: psk
psk: "{{ ssid_psk }}"
wpa_encryption_mode: WPA2 only
splash_page: None
ip_assignment_mode: Bridge mode
vlan_id: 100By storing this playbook in a Git repository, you create a version-controlled source of truth for your network configuration. This GitOps approach, a hot topic in Linux CI/CD news, allows for peer review, change tracking, and easy rollbacks, bringing software development best practices to network management.
Beyond Basic Configuration: Advanced Use Cases
The true power of this integration is realized when you move beyond simple tasks and build sophisticated, event-driven workflows that connect your network to the broader IT ecosystem.
Dynamic Inventory Management
Manually maintaining an inventory file is tedious. Ansible’s dynamic inventory feature solves this by using a script to fetch inventory information from an external source—in this case, the Meraki Dashboard. The `cisco.meraki` collection includes an inventory plugin that makes this seamless. You simply create a YAML configuration file to tell Ansible how to connect to Meraki.
# Filename: meraki.yml
# This file tells the Ansible inventory plugin how to connect to Meraki
plugin: cisco.meraki.meraki
# Use environment variables for authentication
auth:
api_key: "{{ lookup('env', 'MERAKI_DASHBOARD_API_KEY') }}"
# Create groups based on network tags, product types, etc.
group_by:
- key: network_tags
prefix: tag
- key: product_type
prefix: productWith this file, running `ansible-inventory -i meraki.yml –graph` will output a real-time, structured inventory of all your Meraki networks, automatically grouped by tags or device types. This is essential for targeting playbooks at scale and is a core practice for advanced Linux orchestration.

While Ansible modules cover most use cases, sometimes you need custom logic that is better suited for a full-fledged programming language. The official `meraki-sdk` for Python allows for intricate scripting. For example, you could write a script that scans for all connected clients, identifies those running a specific operating system, and applies a Meraki policy to them. This integrates network management with endpoint management, a concept relevant to Linux desktop news and enterprise security.
import os
import meraki
# Initialize the Meraki Dashboard API
# The SDK automatically uses the environment variable for the API key
dashboard = meraki.DashboardAPI(suppress_logging=True)
ORGANIZATION_ID = "YOUR_ORG_ID"
TARGET_OS = "Android"
POLICY_TO_APPLY = "Block" # Can be 'Normal', 'Blocked', 'Group policy', etc.
GROUP_POLICY_ID = "101" # Only if applying a group policy
try:
# Get all devices in the organization
devices = dashboard.organizations.getOrganizationDevices(ORGANIZATION_ID)
for device in devices:
if 'networkId' in device:
# Get clients for each network
clients = dashboard.networks.getNetworkClients(device['networkId'])
for client in clients:
if client.get('os') == TARGET_OS:
print(f"Found {TARGET_OS} client: {client['description']} ({client['mac']})")
# Apply a policy to the client
dashboard.networks.provisionNetworkClients(
device['networkId'],
clients=[{'mac': client['mac'], 'devicePolicy': POLICY_TO_APPLY}],
policiesBySecurityAppliance=None,
policiesBySsid=None
)
print(f"Applied '{POLICY_TO_APPLY}' policy to {client['mac']}.")
except meraki.APIError as e:
print(f"Meraki API error: {e}")
This type of custom script, perhaps triggered by a webhook or a systemd timer, enables highly responsive and intelligent network automation that goes far beyond static configuration.
Best Practices for Robust Network Automation
As you adopt network automation, adhering to best practices is critical for maintaining stability, security, and scalability. This is a recurring theme in all major Linux open source project discussions.
Security First: Managing Secrets
Never store API keys, passwords, or other sensitive data in plain text within your playbooks or source code. Use Ansible Vault to encrypt these secrets. It integrates seamlessly with Ansible, decrypting data at runtime.
ansible-vault encrypt_string 'YOUR_API_KEY_HERE' --name 'meraki_api_key'
This command encrypts your key, which you can then safely commit to your Git repository inside a `vars` file.
Idempotency and Control
Ansible modules are designed to be idempotent, meaning you can run a playbook multiple times, and it will only make a change if the current state does not match the desired state. Always leverage this feature. Before applying changes to a production environment, use Ansible’s `check_mode` (or `–check` flag) to perform a dry run. This will report what changes *would* be made without actually making them, preventing costly mistakes.
Structure and Scalability
For anything beyond a few simple playbooks, organize your code using Ansible Roles. A role is a standardized, reusable way to bundle tasks, variables, templates, and handlers. For example, you could create a `meraki_site_onboarding` role that contains all the necessary tasks to bring a new branch office online, from creating the network to deploying standardized firewall rules and SSIDs.
The Future is Automated
The integration of Red Hat Ansible and Cisco Meraki represents a significant leap forward in network management. By adopting an Infrastructure as Code approach, network teams can dramatically increase their speed and agility, reduce the risk of configuration errors, and enforce consistency and security standards across their entire infrastructure. This shift transforms the role of a network engineer from a manual operator to a strategic automator, focusing on designing and optimizing systems rather than performing repetitive tasks.
As covered in recent Linux Foundation news, automation is no longer a luxury but a necessity for modern IT operations. The journey starts with small, incremental steps: automate a single, repetitive task. Version control your playbooks. Use Ansible Vault for your secrets. By building on these foundations, you can create a robust, scalable, and fully automated network that is ready to meet the challenges of tomorrow.



