Critical Linux Bluetooth Flaw: A Deep Dive into Kernel Security and Mitigation
In the world of operating systems, the Linux kernel stands as a titan, powering everything from massive cloud servers Learn about Linux Bluetooth news.
Revolutionizing Linux Deployments: A Deep Dive into Systemd’s HTTP Boot Feature
The Linux boot process has been a cornerstone of system administration for decades, evolving from simple BIOS and LILO setups to Learn about systemd news.
Rsync Security Deep Dive: Hardening Your File Transfers in 2025
rsync news: Rsync Security Deep Dive: Hardening Your File Transfers in 2025 In the vast ecosystem of Linux administration and DevOps, few tools are as u…
Hardening Your GitLab Instance on Linux: A Proactive Defense Strategy for Modern DevOps
In the fast-paced world of software development, Continuous Integration and Continuous Deployment (CI/CD) pipelines are the Learn about Red Hat news.
Fortifying Your Network: A Deep Dive into Modern IPsec VPN Security on Linux
IPsec news: Introduction: The Renewed Imperative for Secure IPsec VPNs In an era where remote work has transitioned from a perk to a necessity, the Virt…
Securing Your Observability Stack: A Deep Dive into Grafana Security and Plugin Management on Linux
In the world of modern IT infrastructure and DevOps, Grafana stands as a cornerstone of observability, providing powerful Learn about Grafana news.
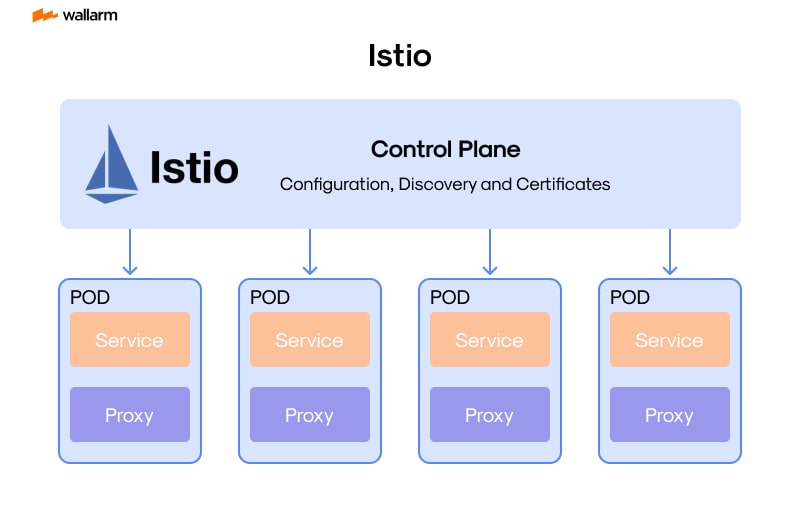
Istio’s Latest Evolution: Embracing Gateway API, Ambient Mesh, and Simplified Multi-Cluster Management
Istio news: In the dynamic world of cloud-native computing and microservices, Istio has long stood as a cornerstone technology, providing a robust and f…
Mastering Linux File Permissions: The Unsung Guardian of System Security
The Foundation of a Secure System: Why Linux File Permissions Matter In the vast and dynamic world of Linux, from Learn about Linux file permissions news.