
Securing Your Observability Stack: A Deep Dive into Grafana Security and Plugin Management on Linux
In the world of modern IT infrastructure and DevOps, Grafana stands as a cornerstone of observability, providing powerful visualization for metrics, logs, and traces. Deployed across countless Linux servers, from on-premise data centers running Red Hat Enterprise Linux or Debian to cloud instances on AWS and Google Cloud, Grafana empowers teams to understand their systems’ performance. However, with great power comes great responsibility. The extensibility that makes Grafana so versatile—its vast ecosystem of plugins—can also introduce security risks. A recent critical vulnerability in a popular plugin serves as a stark reminder that securing our monitoring stack is just as crucial as securing the applications it observes. This is a major topic in Linux security news and for anyone involved in Linux administration.
This article moves beyond the headlines to provide a comprehensive technical guide for Linux administrators and DevOps professionals. We will dissect the nature of such vulnerabilities, provide actionable steps for mitigation and patching on various Linux distributions, and explore a defense-in-depth strategy for hardening your entire Grafana instance. We’ll cover everything from command-line verification and automated patching with Ansible to advanced configuration and best practices for supply chain security in a containerized world, ensuring your observability platform remains a trusted asset, not a security liability.
Understanding the Threat: The Role and Risks of Grafana Plugins
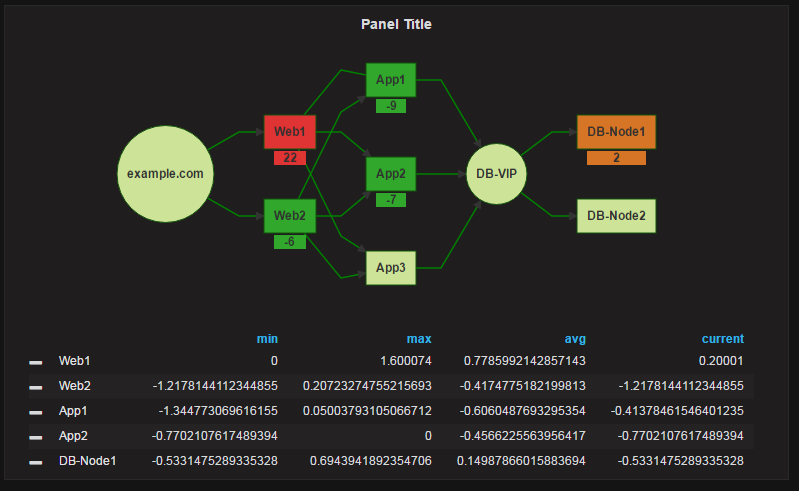
Grafana’s power is significantly enhanced by its plugins, which extend its functionality to connect to various data sources, add new panel types, and integrate with other systems. The Image Renderer plugin is a prime example of a critical utility. It runs as a separate backend service, often using a headless browser, to render Grafana panels and dashboards into PNG images. This functionality is essential for features like PDF reporting and including dashboard snapshots in alert notifications sent to services like Slack or email.
The security risk in such plugins often stems from how they handle input and interact with other services. A common vulnerability class is Server-Side Request Forgery (SSRF). In an SSRF attack, an unauthenticated attacker could potentially trick the Image Renderer service into making HTTP requests to arbitrary internal or external URLs. The impact of a successful SSRF attack can be severe:
- Internal Network Scanning: An attacker could use the Grafana server as a pivot point to scan your internal network, discovering open ports on other servers and services that are not exposed to the internet.
- Data Exfiltration: It could be used to access internal, unauthenticated endpoints, such as cloud provider metadata services (e.g., the AWS EC2 metadata endpoint at
169.254.169.254), potentially leaking sensitive credentials. - Interaction with Internal Services: The vulnerability might allow an attacker to send requests to internal APIs, databases like PostgreSQL Linux news or Redis Linux news, or other backend systems, potentially leading to further compromise.
For any system administrator, the first step is always assessment. You need to know what you have installed. The grafana-cli tool is the standard way to manage plugins on a Linux server. You can quickly list all installed plugins and their versions with a simple command. This is a fundamental skill discussed in Linux commands news and essential for maintaining systems like Ubuntu, CentOS, or Arch Linux.
# Connect to your Grafana server via SSH
ssh [email protected]
# Use the grafana-cli to list installed plugins
# This command provides the plugin ID and its current version.
sudo grafana-cli plugins ls
# Example Output:
# id: grafana-image-renderer version: 3.5.0
# id: grafana-clock-panel version: 2.1.2
# id: grafana-worldmap-panel version: 1.0.3
# You can get more details on a specific plugin
sudo grafana-cli plugins describe grafana-image-rendererImmediate Mitigation and Patching on Linux Systems
Once a vulnerability is identified and a patch is released, swift action is required. The update process for a Grafana plugin is generally straightforward using grafana-cli. This process applies broadly across most Linux distributions, whether you’re using apt on Debian/Ubuntu, dnf on Fedora/AlmaLinux, or pacman on Manjaro.
Manual and Automated Plugin Updates
For a single server, a manual update is quick. However, in a modern DevOps environment, automation is key. Tools like Ansible, Puppet, or SaltStack are indispensable for managing configurations at scale. An Ansible playbook can ensure that all your Grafana instances are updated consistently and reliably. This approach is central to current Linux DevOps news and best practices for Linux configuration management.
# ansible-playbook.yml
# An Ansible playbook to update a specific Grafana plugin on all designated servers.
---
- name: Secure Grafana by Updating Plugins
hosts: grafana_servers
become: yes # Use sudo to run commands
tasks:
- name: Update the Grafana Image Renderer plugin
command: grafana-cli plugins update grafana-image-renderer
register: plugin_update_result
changed_when: "'Installed' in plugin_update_result.stdout"
- name: Restart Grafana to apply changes
systemd:
name: grafana-server
state: restarted
when: plugin_update_result.changed
# This leverages systemd, a key topic in systemd news
- name: Verify the new version of the plugin
command: grafana-cli plugins ls
register: plugins_list
changed_when: false
check_mode: no
- name: Assert that the plugin is at the patched version (e.g., 3.6.1)
assert:
that:
- "'grafana-image-renderer version: 3.6.1' in plugins_list.stdout"
fail_msg: "Image Renderer plugin is NOT at the required patched version!"
success_msg: "Image Renderer plugin successfully updated to 3.6.1."Network-Level Mitigation with Firewalls
If immediate patching is not feasible, network-level controls can provide a temporary but effective mitigation. For an SSRF vulnerability, the goal is to prevent the Grafana server from making unauthorized outbound network connections. Using a Linux firewall like nftables (the modern successor to iptables) or a cloud security group, you can implement an egress filtering policy. This policy should deny all outbound traffic by default and only allow connections to specific, trusted endpoints (e.g., your Prometheus or PostgreSQL servers). This is a critical practice highlighted in Linux firewall news and Linux networking news.
#!/bin/bash
# An example script to apply restrictive egress firewall rules using nftables
# This script assumes 'grafana' is the user running the Grafana process.
# Flush existing rules
nft flush ruleset
# Create a new table
nft add table inet filter
# Create chains for input, forward, and output
nft add chain inet filter INPUT { type filter hook input priority 0 \; }
nft add chain inet filter FORWARD { type filter hook forward priority 0 \; }
nft add chain inet filter OUTPUT { type filter hook output priority 0 \; }
# Default deny policies
nft 'add rule inet filter INPUT iifname "lo" accept'
nft 'add rule inet filter INPUT ct state established,related accept'
nft 'add rule inet filter INPUT iif "eth0" tcp dport { 22, 80, 443 } accept' # Allow SSH and Web
nft 'add rule inet filter INPUT drop'
nft 'add rule inet filter FORWARD drop'
nft 'add rule inet filter OUTPUT drop' # Default deny for outbound traffic
# Allow Grafana user to connect ONLY to the Prometheus and PostgreSQL servers
# Get the UID for the 'grafana' user
GRAFANA_UID=$(id -u grafana)
# Allow loopback for the user
nft add rule inet filter OUTPUT oifname "lo" skuid $GRAFANA_UID accept
# Allow connections to specific internal services
nft add rule inet filter OUTPUT ip daddr 10.0.1.10 tcp dport 9090 skuid $GRAFANA_UID accept # Prometheus
nft add rule inet filter OUTPUT ip daddr 10.0.1.20 tcp dport 5432 skuid $GRAFANA_UID accept # PostgreSQL
# Allow DNS lookups
nft add rule inet filter OUTPUT udp dport 53 skuid $GRAFANA_UID accept
echo "Restrictive egress firewall rules applied for Grafana."
# To make these rules persistent on a Debian/Ubuntu system:
# sudo apt install nftables
# sudo systemctl enable nftables
# sudo nft list ruleset > /etc/nftables.confProactive Hardening for Your Grafana Instance
Reacting to vulnerabilities is necessary, but a proactive security posture is far better. Hardening your Grafana installation involves a multi-layered approach, often referred to as “defense-in-depth.” This ensures that even if one layer is breached, others are in place to limit the damage.
Using a Reverse Proxy for Security
Never expose the Grafana application server directly to the internet. Instead, place it behind a hardened reverse proxy like Nginx or Caddy. A reverse proxy can handle TLS termination, enforce strong cipher suites, add security headers, and provide an additional layer of access control. This is a standard best practice for deploying any web application, a frequent topic in Nginx Linux news and Linux web servers news.

# /etc/nginx/sites-available/grafana.conf
# Example Nginx reverse proxy configuration with security headers for Grafana
server {
listen 443 ssl http2;
listen [::]:443 ssl http2;
server_name grafana.yourdomain.com;
# TLS Configuration
ssl_certificate /etc/letsencrypt/live/grafana.yourdomain.com/fullchain.pem;
ssl_certificate_key /etc/letsencrypt/live/grafana.yourdomain.com/privkey.pem;
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers 'ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-GCM-SHA384';
# Security Headers
add_header X-Frame-Options "SAMEORIGIN";
add_header X-Content-Type-Options "nosniff";
add_header Referrer-Policy "strict-origin-when-cross-origin";
add_header Strict-Transport-Security "max-age=31536000; includeSubDomains; preload" always;
add_header Content-Security-Policy "default-src 'self'; script-src 'self' 'unsafe-inline'; style-src 'self' 'unsafe-inline'; img-src 'self' data:;";
location / {
proxy_pass http://localhost:3000;
proxy_set_header Host $http_host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto $scheme;
}
}Authentication, Authorization, and Configuration
Strengthen access controls within Grafana itself. Disable anonymous access unless absolutely necessary. Integrate with a centralized authentication provider like LDAP, SAML, or OAuth (e.g., via GitHub, Google) instead of relying solely on Grafana’s built-in user management. Within Grafana’s configuration file (grafana.ini), enforce secure settings such as setting the cookie_secure flag to true to ensure cookies are only sent over HTTPS and setting allow_embedding to false to prevent clickjacking attacks.
Supply Chain Security in a Containerized World
Many modern deployments, especially those managed with Kubernetes Linux news or Podman news, run Grafana inside containers. This introduces another layer to secure: the container image itself. The “supply chain” for your Grafana instance includes the base OS image (e.g., Alpine Linux, Ubuntu), the Grafana binary, and all plugins. A vulnerability in any of these components can compromise the entire container.
Integrating automated security scanning into your CI/CD pipeline is essential. Tools like Trivy, Grype, or Snyk can scan your Dockerfiles and container images for known vulnerabilities (CVEs) before they are ever deployed to production. This proactive scanning is a cornerstone of modern DevSecOps and a recurring theme in Linux CI/CD news.
# Dockerfile for a custom Grafana image
# Note: Using a specific version is better than 'latest' for production.
FROM grafana/grafana:9.2.5
# Set environment variables to install plugins
# This method is preferable to using grafana-cli inside a running container
ENV GF_INSTALL_PLUGINS="grafana-clock-panel,grafana-worldmap-panel,grafana-image-renderer"
# --- CI/CD Pipeline Integration Example (e.g., in a GitLab CI or GitHub Actions file) ---
#
# build_and_scan_grafana:
# stage: security
# image: aquasec/trivy:latest
# script:
# # 1. Build the Docker image first (steps not shown)
# # docker build -t my-custom-grafana:1.0 .
#
# # 2. Scan the image for vulnerabilities
# # The '--exit-code 1' flag will fail the pipeline if critical/high vulnerabilities are found.
# trivy image --exit-code 1 --severity CRITICAL,HIGH my-custom-grafana:1.0
#
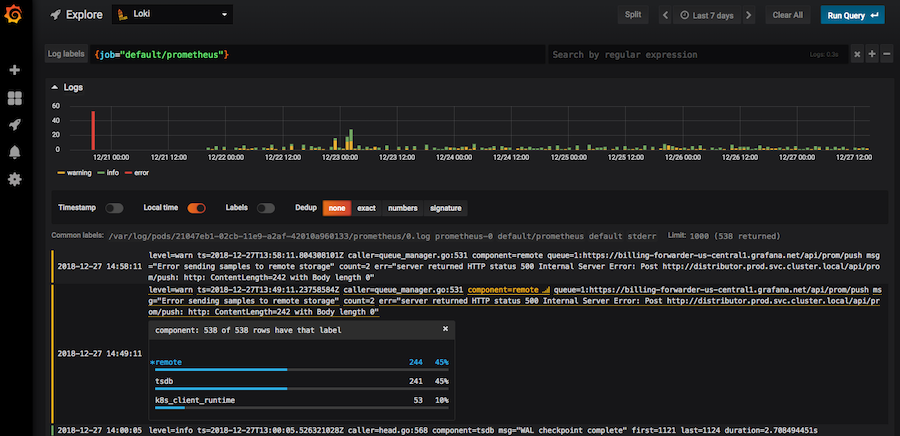
# # 3. If the scan passes, the image can be pushed to a registry and deployed.By building security scanning directly into your deployment process, you shift from a reactive to a proactive model. You catch vulnerabilities before they hit production, ensuring that your observability stack, powered by tools like Prometheus and Loki, is built on a secure foundation. This is a critical aspect of modern Linux observability news.
Conclusion: Vigilance as a Core Principle
The security of your Grafana instance is not a one-time setup but an ongoing process of vigilance. A vulnerability in a single plugin can have far-reaching consequences, potentially exposing your internal network and sensitive data. The key takeaways for every Linux administrator and DevOps engineer are clear: always know what software and versions you are running, have a plan for rapid and automated patching, and implement a defense-in-depth security strategy.
By combining timely updates with network-level controls, robust authentication, and proactive container scanning, you can significantly harden your observability platform. Treat your monitoring stack with the same security rigor as your production applications. In doing so, you ensure that Grafana remains a powerful tool for insight, not an unintended gateway for attackers. Staying informed through channels like Linux security news and vendor advisories is the final, crucial piece of this continuous security puzzle.



